“Nothing in the world could take us back/ to where we used to be,” as Mariah Carey sings in her 1990 hit, I Don’t Wanna Cry–recorded back in the very year Tim Berners-Lee and CERN collaborators unveiled the World Wide Web, using HTML to share documents across huge networks and URL’s to specify computer targeted and information requested. The coincidence of the design of such a document system that led TBL to build and design the world’s first web browser on an NeXT computer and Mariah Carey’s cooing soft-pop hit on only emptiness inside came together again in the release the WannaCry malware–malicious self-propagating code, able to exploit back-door vulnerabilities of Windows 7–which revealed a landscape from which nothing in the world can take us back to where reused to be.
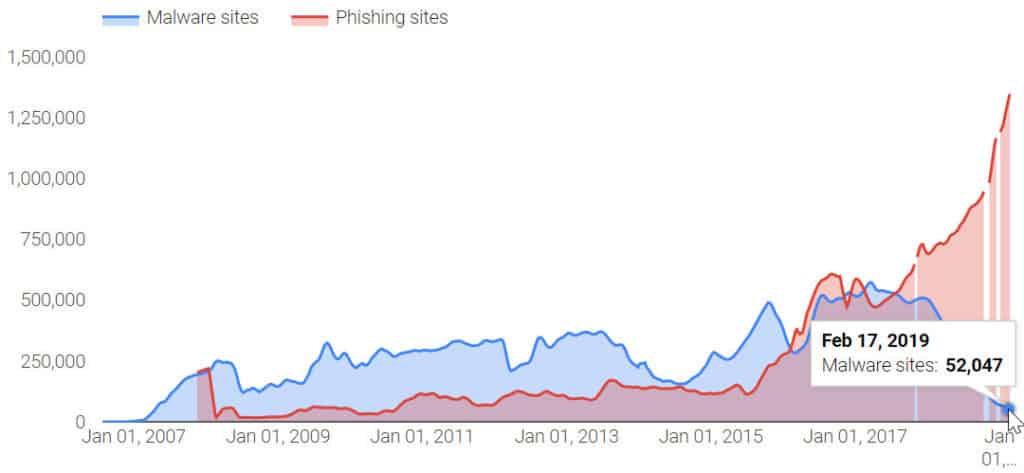
Indeed, the boom of Malware by which the world’s information highways have been afflicted may have in general declined since 2017, from when the number of malware variants has dropped considerably, malware attacks, from ransomware to cryptojacking attacks, have risen, and the number of malicious email attachments has ballooned, often by inserting malicious code into a website to allow hackers to view financial information and histories of corporate entities and other institutions. The absence of any guides to ransomware of different varieties have left many increasingly vulnerable, as networks gain the vulnerability akin to “skimmer” able to glean financial histories off of the magnetic strips of credit cards at ATM’s across the world, exposing the global vulnerabilities into an infrastructure allowing global financial transactions. And despite relatively wide consensus that one should not pay ransoms from WannaCry as doing so would neither ensure access to the compromised files and possibly only expose one to further vulnerabilities to future attacks, the current wisdom of disconnecting all devises from Ethernet cables and wireless dongles suggest that disconnection without rebooting the system is in fact the best option for compromised systems, with an installation of Microsoft’s security patch–in addition to windows security updates and a reputable antivirus blocker. But the fear of vulnerability in a world where WannaCry remains a threat that has continued to hit 13,000 plus organizations since 2020 has led to increased concern how to prevent WannaCry attacks.
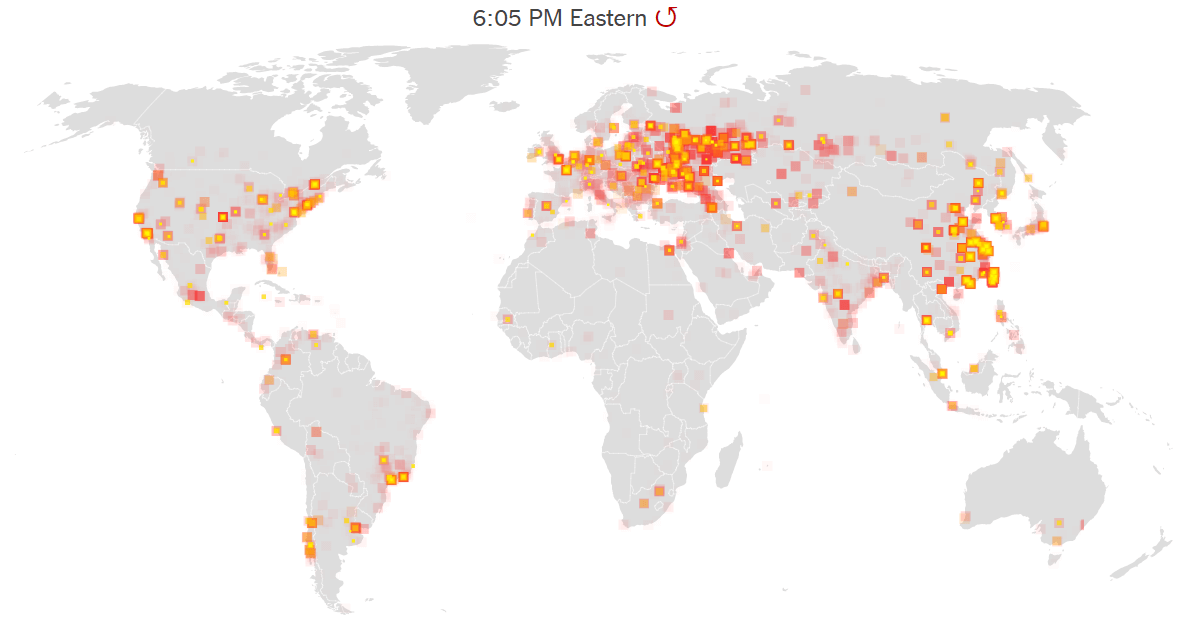
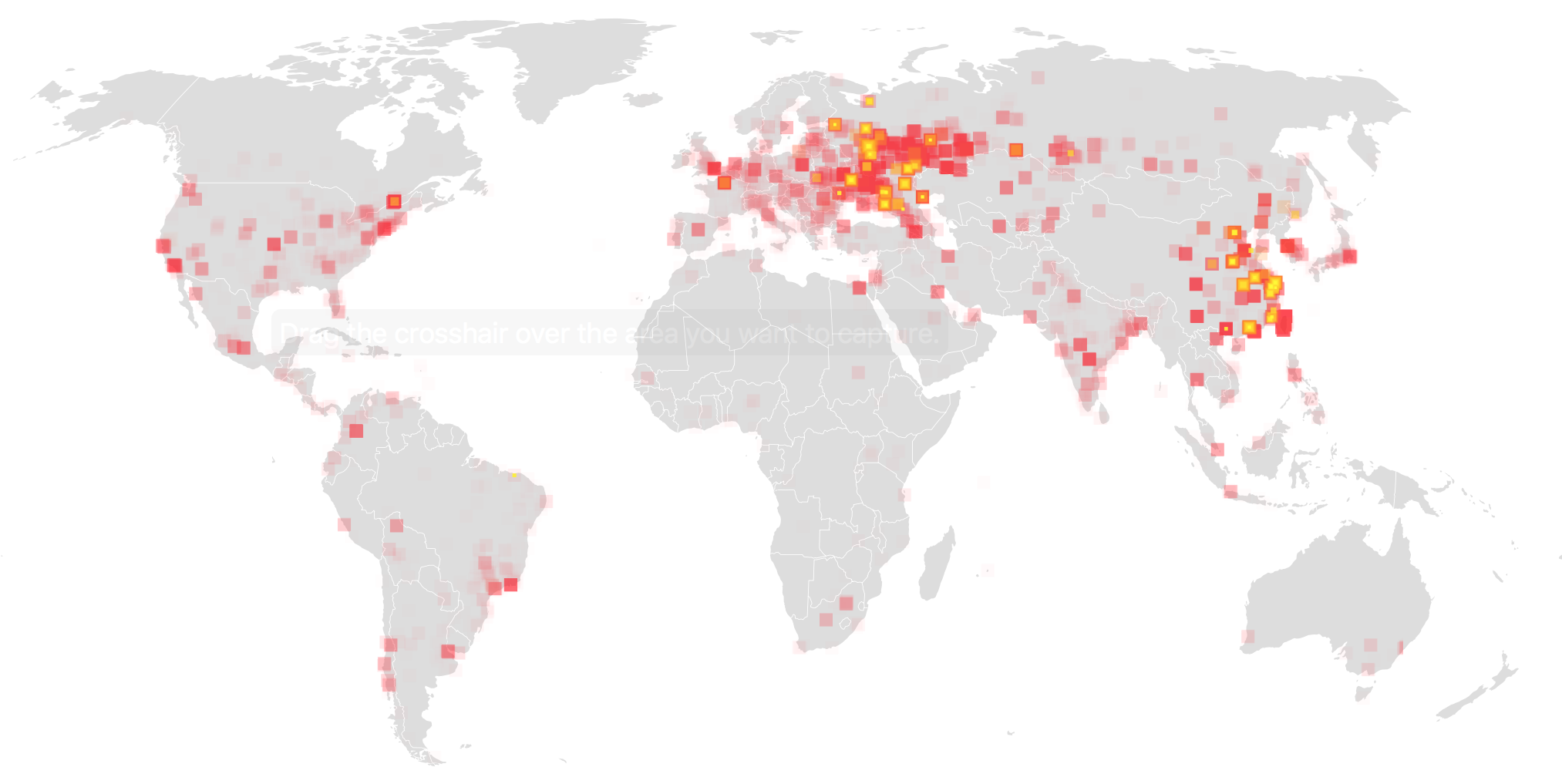
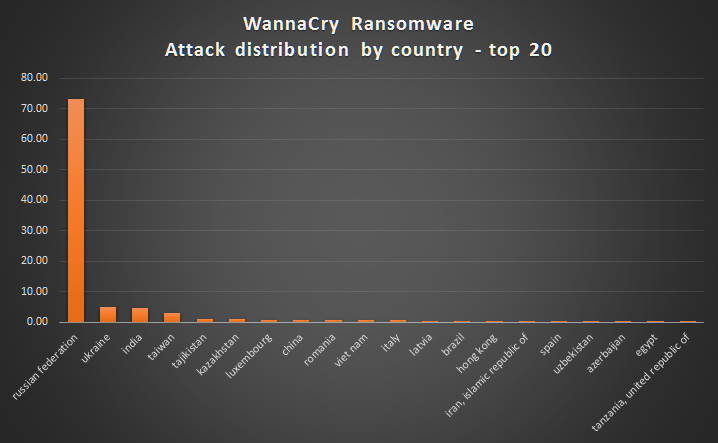
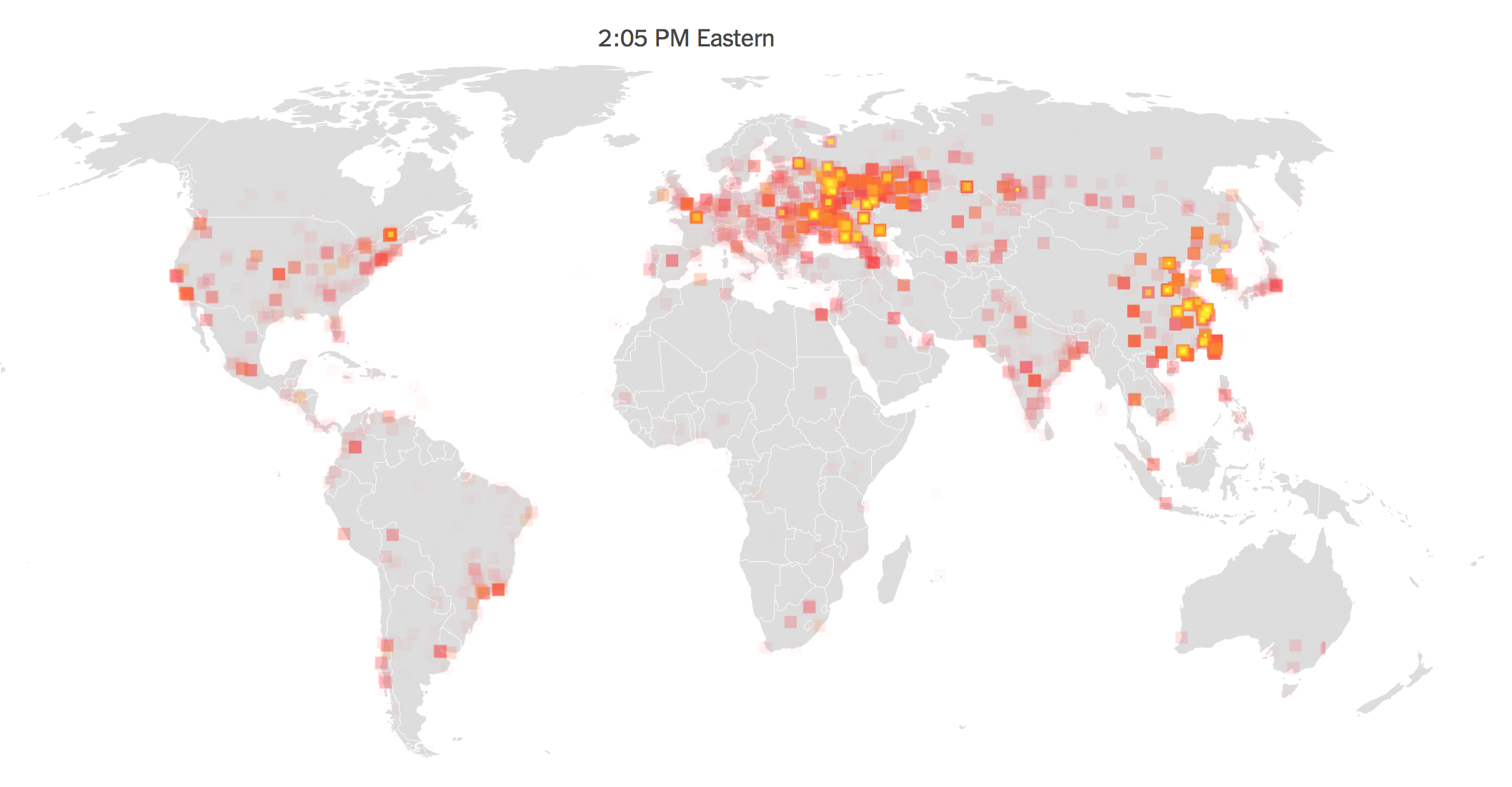
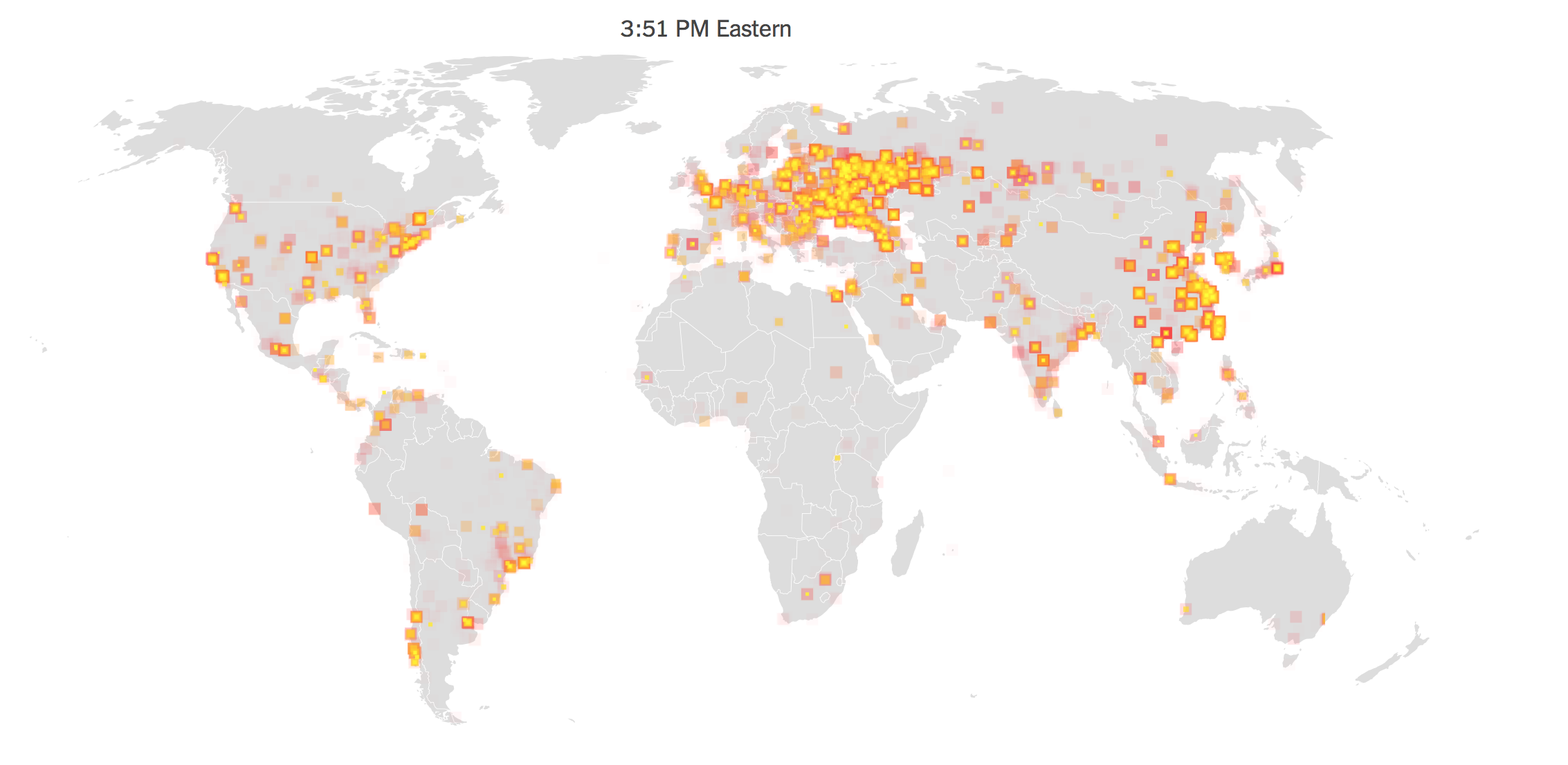
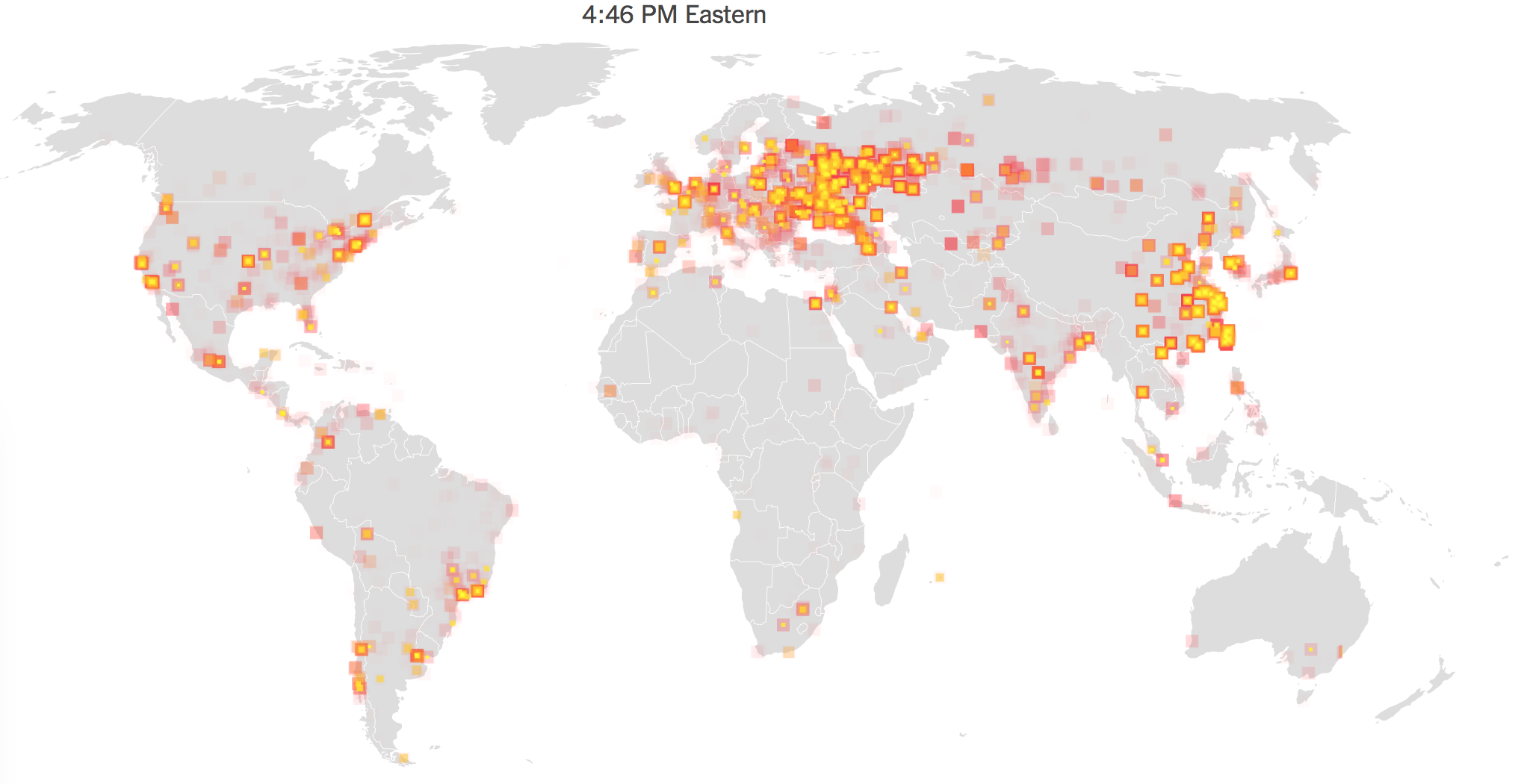
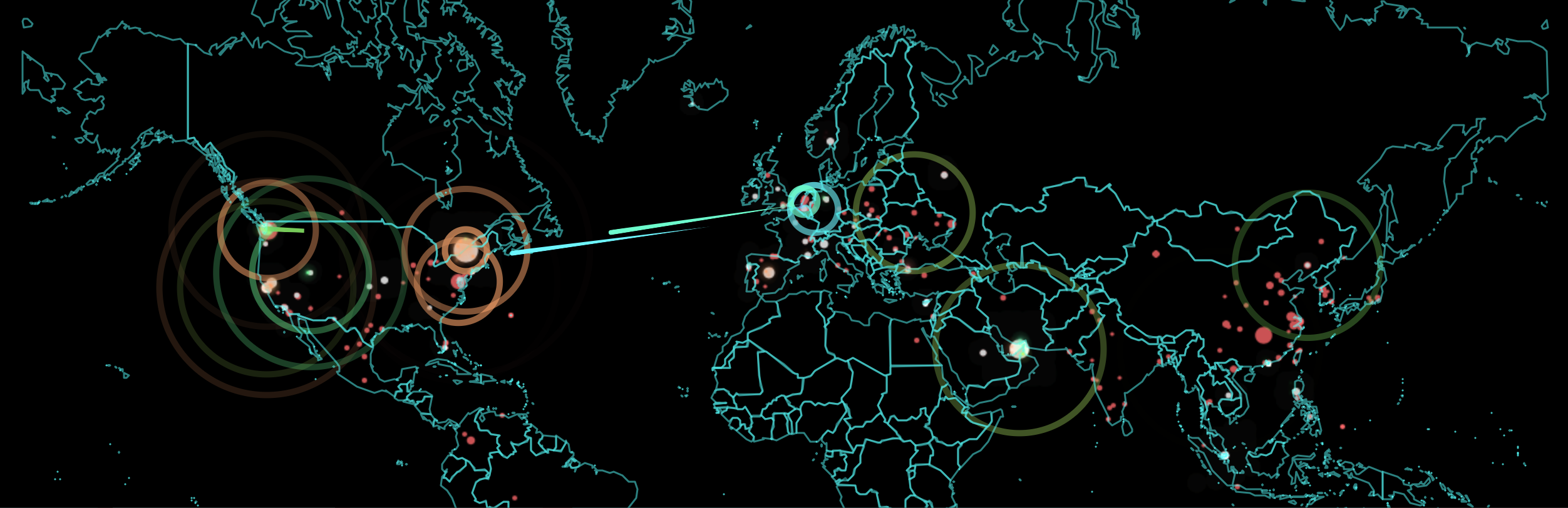
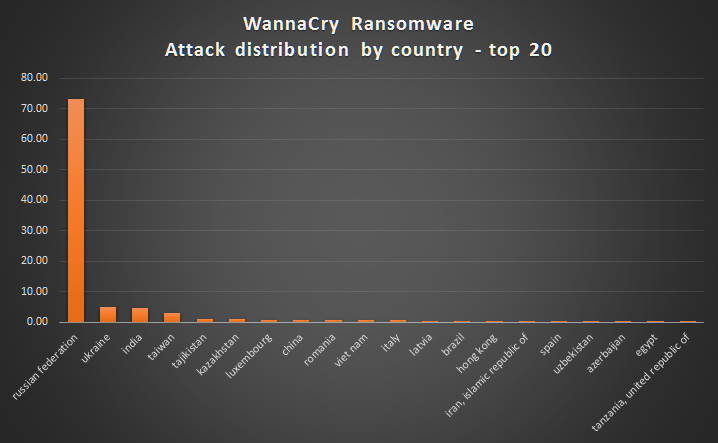
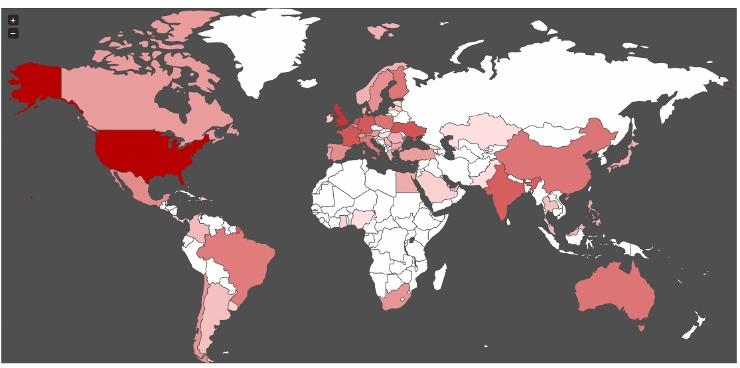
But the data visualizations we’ve used to describe the lateral progression of the encryption of data files from hard drives around the interlinked world lent a new prominence to the World Wide Web as a conduit for targeting destabilization. It not only revealed how the world wide web has reshaped what we still call the world, but posed questions of how to map such a change, as even Microsoft employees in Redmond, Washington scrambled to chart the outbreak of malware after hackers exploited vulnerabilities in the unpatched Eternal Blue, in cyber attacks alternately known as WannaCry in 2017, and Non Petya when it later hit Ukraine, together with all companies, including large American ones, who did business with that nation, in an attempt to undermine its economic viability. From command central in what seems a concrete bunker of the future, before large screens, non-state Microsoft workers in Redmond, Washington tried to maintain a sense of security in their systems around the clock, and conduct repairs, in the weeks after the United States Department of Homeland Security urgently warned that out-of-date software was a global crisis and a national vulnerability. The malware just posed problems that local governments, municipalities, and law enforcement institutions could not bear, and which it seemed only Microsoft could be able to have manpower, incentives, and infrastructure to complete.

Wanna Cry left many literally crying for the sudden encryption of data, and many without services–and was intended to leave an unimaginable number of people desolate, if not quite with the absence of love that Mariah Carey wistfully evoked. But the virulence of its spread should offer a wake-up call to possibilities of global disruption we are still working to be able to track, map or fully comprehend in adequate fashion–but record as a virulent virus blocking systems most densely in nodes of a web-linked world.

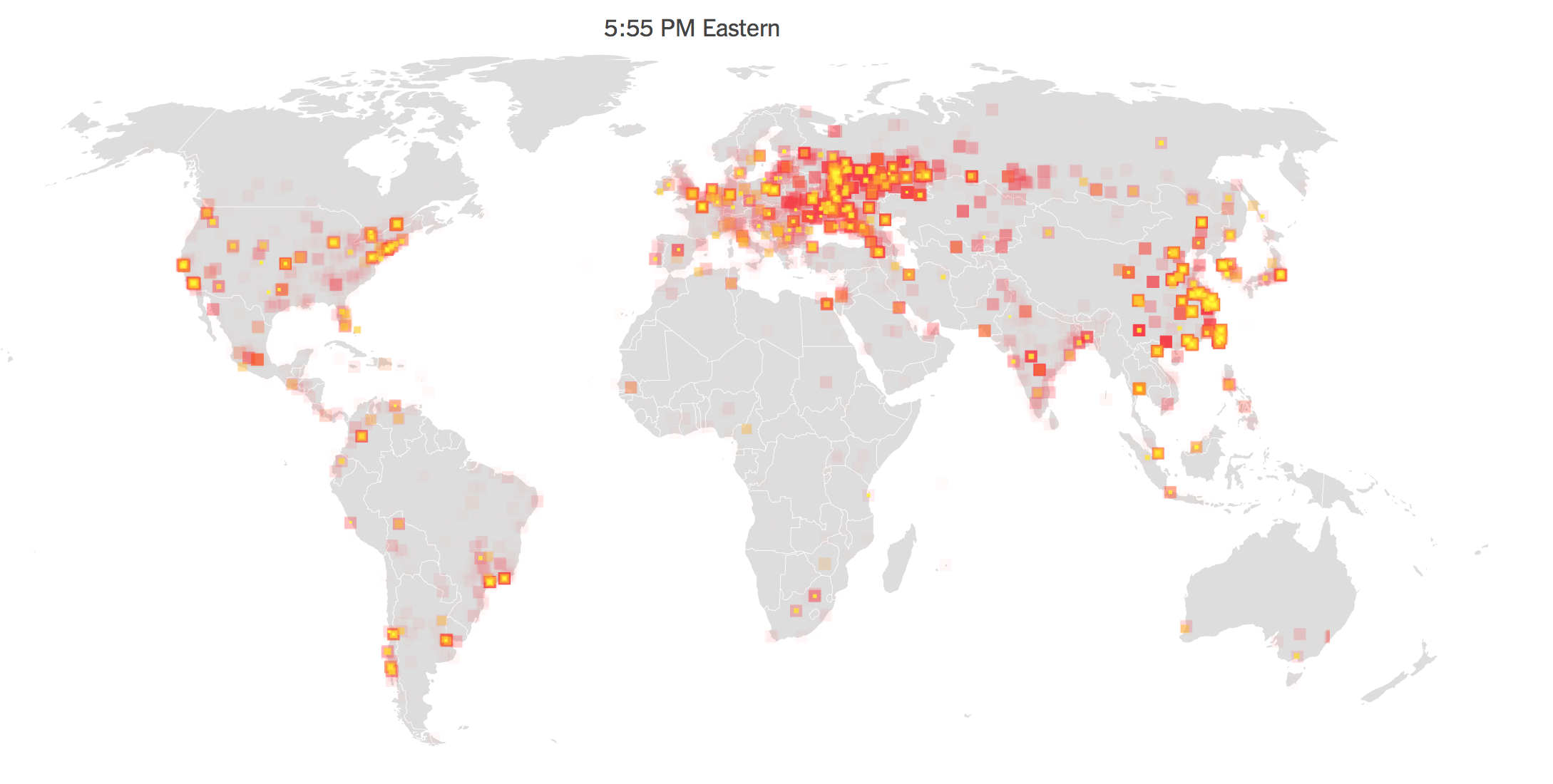
New York Times
The very same visualizations indeed obscure, by oddly rendering it as distributed, the agency that underpins such carefully orchestrated cyber attacks of global consequence, by almost naturalizing its spread. For by moving the sites where data was most encrypted into a geographical frame of reference, the graphic doesn’t help orient us to its spread, so much as overwhelm us with the data-laden content to visualize a paralysis of global systems; it removes it from context or human agency, in order to capture the omnipresence of the self-propagating cyrptoworm as much as tell a story that helps to orient us to its spread. Perhaps that is what was intended.
The mapping of global disruption is perhaps a nightmarish puzzle for members of the interlinked world, and demands a place on the front burners of data visualization: the inadequate nature of considering the spread of systems-wide corruptions can be visualized by cases of the compromising of data, we lack the symbolic tools to grasp the rise of a new map of global dangers. While such data visualizations provide a terrifying premonition of the destabilization that might result from the encryption of data on a broad scale, they obscure the possibilities of specifically targeted attacks on data and visible infrastructure that are now able to be developed, and the nature of targeted threats that we have only begun to imagine. The redefinition in this new geography of document-sharing Tim Berners-Lee and friends developed has prepared the way for a landscape of interaction between removed places broadly adopted as a protocol for information-sharing– but one that, as Mariah Carey sung, and instigators of the malware hoped, left one only wanting to cry from behind one’s screen, devastated at the scope of the unforeseen swift data loss.
The data visualizations adopted to depict the flare-ups in compromised hard drives that the cryptoworm created in a manner of hours show the particular virulence with which malware crossed national divides in unprecedented ways, displacing relations of spatial proximity, geographical distance, and regional divides. In crippling databases including Russian and Chinese private and public institutions in but a day, demanding immediate payment for data to be restored, the ransomware raised the curtain on a new age of uncertainty. But was the threat eclipsed by the scale of the attack by which information was encrypted? If the spread of malware seemed to grow across computer systems without apparent relations, the distributed agency that was invested in how the malware spread worldwide seemed to obscure the possibility of agency of the attacks, concealing the tracks of any perpetrator by placing a problem of urgency on screens worldwide.

Websites of news media of record widely adopted animated data visualizations to orient their readers to the proliferating corruption of data on tens of thousands of computers and computer systems on account of the malware caused. Such elegantly animated maps don’t claim to be comprehensive, and are information-laden to the extent that seek to capture the unprecedented speed and range of the spread of the cyberworm launched Friday, May 12, 2017. We have trouble even comprehending or grasping the scale or speed with which the virus spread on systems, of course, and speed at which malware was propagated itself across networks and spread laterally across systems, rather than by geographic relations, working without a phishing hook of any sort but exploiting an NSA-developed backdoor vulnerability in the Windows 7 operating system to infect networks across national bounds, as it spread laterally across systems worldwide.
The spread of the encryption of hard drives data across space occurred in apparently haphazard ways, spreading globally in the first thirty minutes of across more advanced web-reliant regions of what we still call the globe. While their spread “followed” systems whose operating systems had not been fully updated, it is important to remember that rather than spreading laterally along a system of their own accord, their release was planned and released by agents, rather than being a casualty of the World Wide Web; a map of instances of hard-drive vulnerabilities however can offer few diagnostic signs or clues to interpret their spread, but offer only a catalogue of individual instances difficult to process in their entirety, so overwhelming and geographically dispersed was their occurrence to defy easy interpretation or processing–they provide little that might be suggested as forensic evidence about their spread.
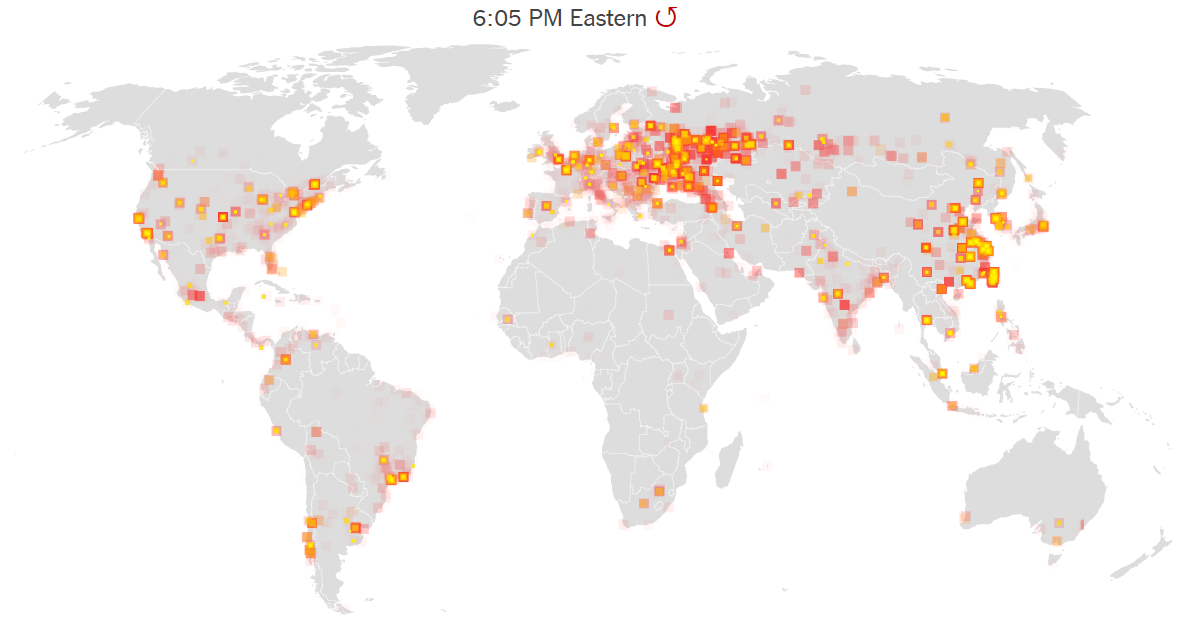
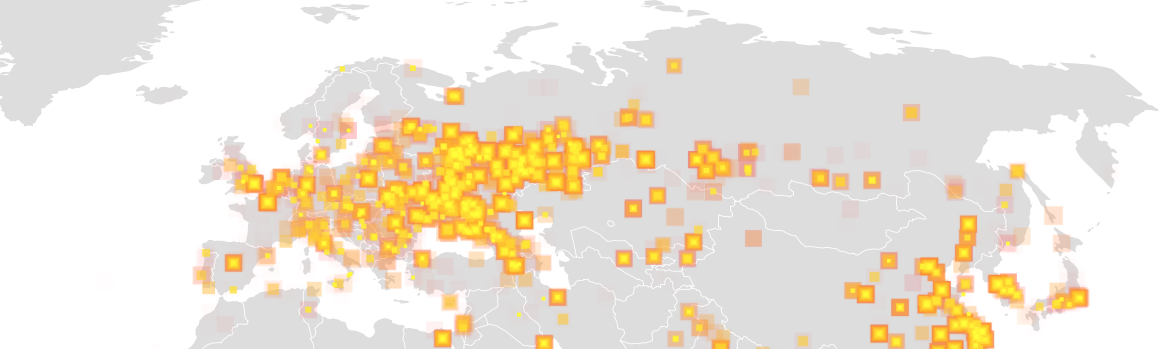
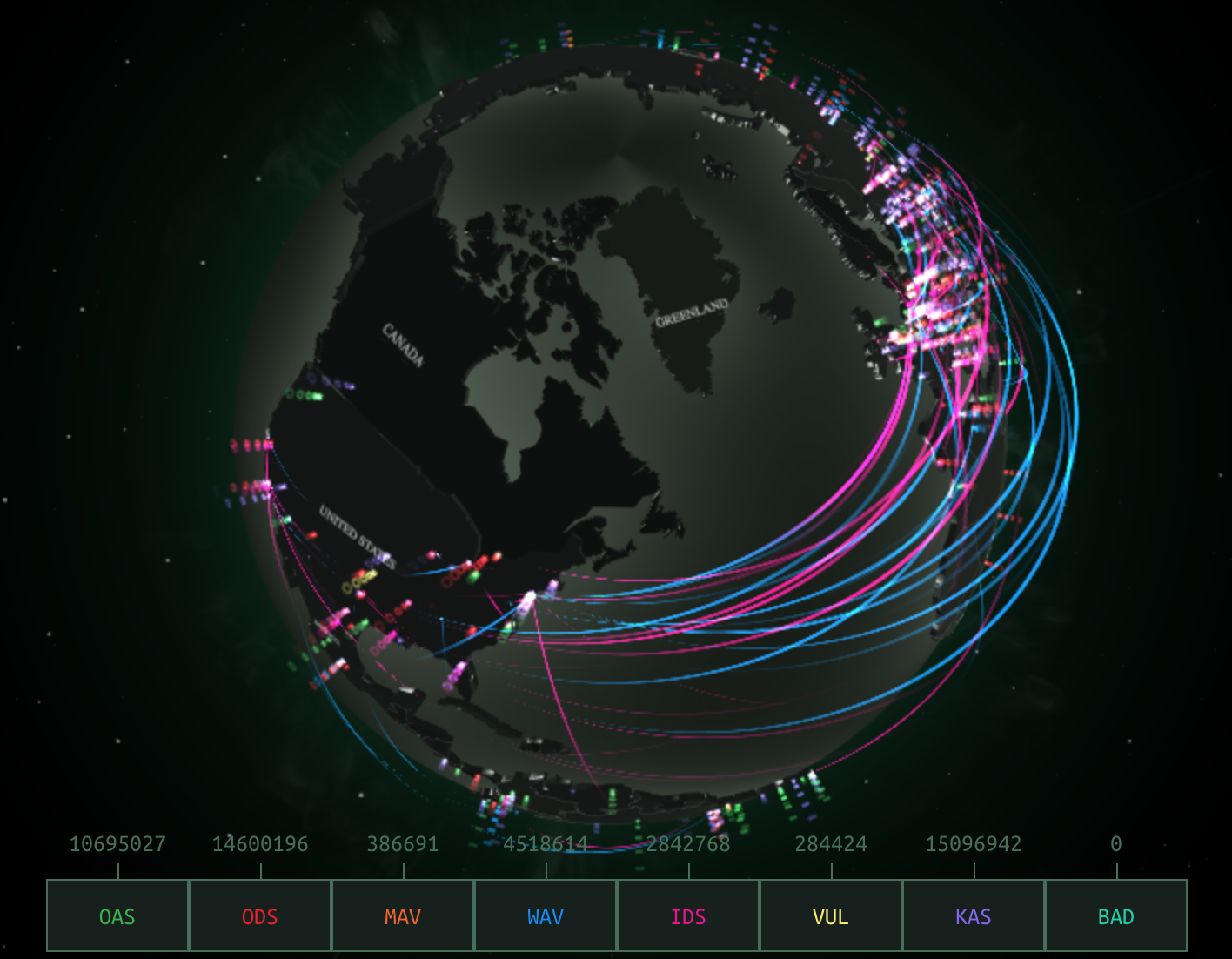
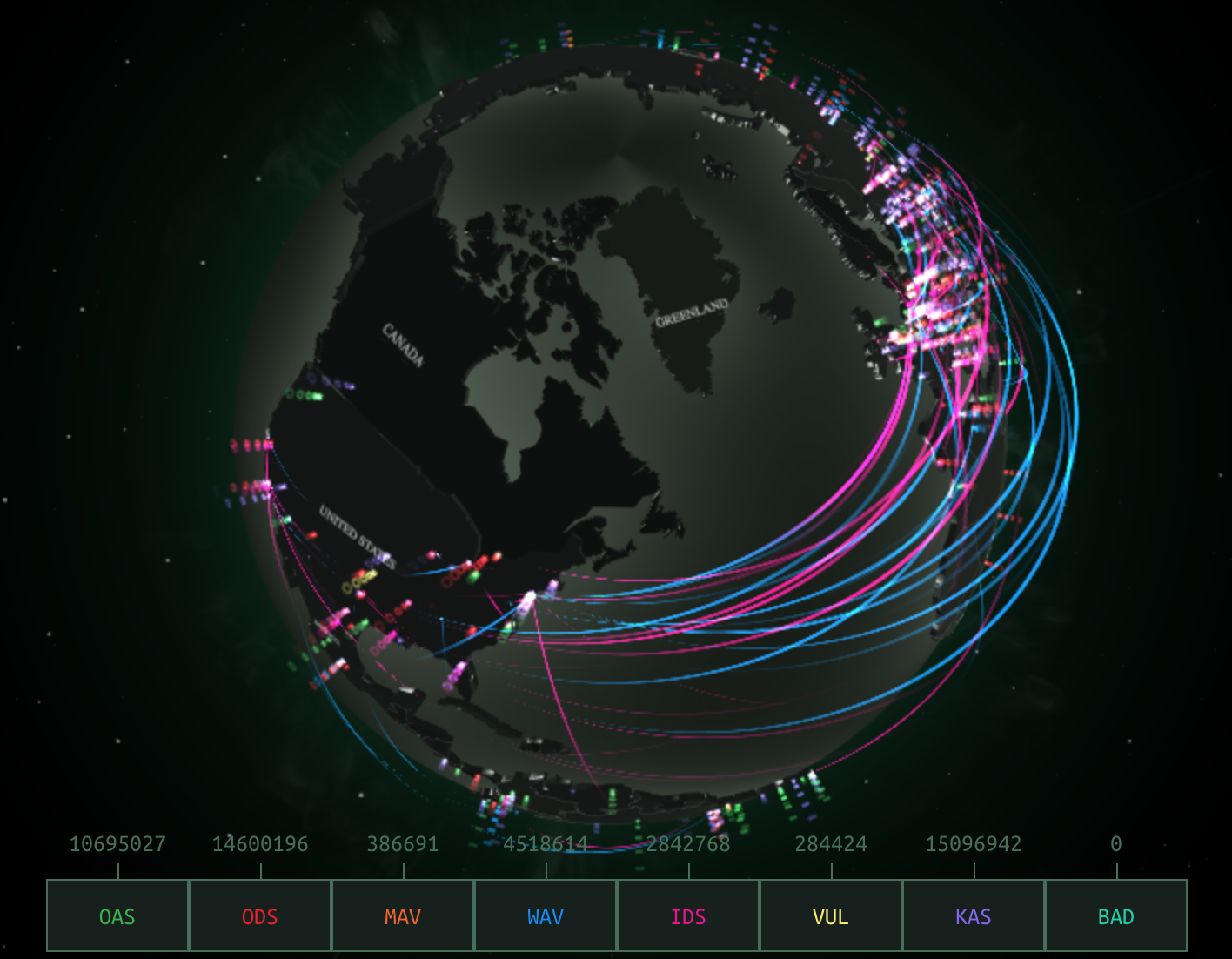
Red Socks Security: Malicious Threat Detection
If the growth of the virus’s spread across nations made it seemed to progress in ways that lacked a target, we may lack the tools to visualize the attack. The systems afflicted were not linked on a geographical register, and in some senses didn’t make sense to read in a map–but if they spread on internet traffic, the broad scale of the attack of ransomeware only foregrounded the fears of where it had arrived from or offer any signs to appreciate any agency within its systems-borne spread. But if the map seemed the best way to the speed of its growth, it was a distraction from the potential targeted threats of the malicious worm–until a lone British researcher, known as “MalwareTech,” saved the compromising of global systems as he serendipitously identified its kill switch to stop its spread: what dominated the headlines conceals the dangers of losing sight of the specificity of the wide-ranging attacks, even while registering them in real time.
The rest of the world could only sit in silence, as Mariah Carey once sung, and watch the range of attacks unfold in space in real time: something went wrong in the mode of sharing data across online systems that had to be couldn’t quite be understood. If Maria Carey’s hit single contemplated the definite break in time, “only emptiness inside us,” the shock of the screens informing users across the world that their data had been definitively compromised made then realize that any notion of data security vanished, and any hope for composure in the face of cryptoworms had disappeared, as Mariah Carey’s softly-sung lyrics described, and as far away as a network-free world, or one where inter-connected users didn’t define the primary routes of its transmission, without considering the dangers of the compromised infrastructure–not only in banking, but in traffic system, airport controlling, water quality monitoring, and even traffic flows.
But we continue to rely on geographic registers, as if we can’t let go of them, and it is what we have to explain the global spread of compromised systems and a collapse of data security. The cryptoworm successfully obtained advanced user privileges that allowed it to hijack computer systems that allowed hackers to encrypt documents worldwide in one day, reaching such a broad range of hard drives to make it seem the attack was random or haphazard. The attacks used code to release a self-propagating worm that didn’t really move spatially, but progressed online, using a vulnerability for which Microsoft had released a patch only two months previous, in March, in devices that share files across local networks. After the patch arrived, we were still mapping its spread, and contemplating the prospects of the return of a similar virus, so clearly had it asked us to redefine internet traffic. But was did the broad spread of the worm and broad scope of systems compromises, which was quick to provoke deep fears of the vulnerabilities that exist from ransomware erase the targeted nature of a similar subsequent malware attack? The spread of thousands of infections in over a hundred–and then over a hundred and fifty countries–across hard drives across the world exploited the failure to update software systems so broadly to obscure the origins or coordination of such malware attacks, whose use of normal language to alert users of encryption made them seem as if it were an isolated standard operating failure, able to be resolved by individual payment–

–even as the malware crippled networks in different countries without having the appearance of any fixed target. And if masquerading as a form of ransomware, later variants of the cryptoworm suggested a far, far scarier version of the scope of data corruption.
We were of course struck by the unprecedented speed with which such worms replicated along these dispersive networks–following paths that are not made evident in the map of compromised hard drives provided by data security firms, which show the progression of a disease that, like a cancer, creeps invasively along a hidden network, suggests a nightmare of the distributed agency of the internet, invaded by a particularly vicious parasite that for a considerable amount of time even experts saw no way to resolve.
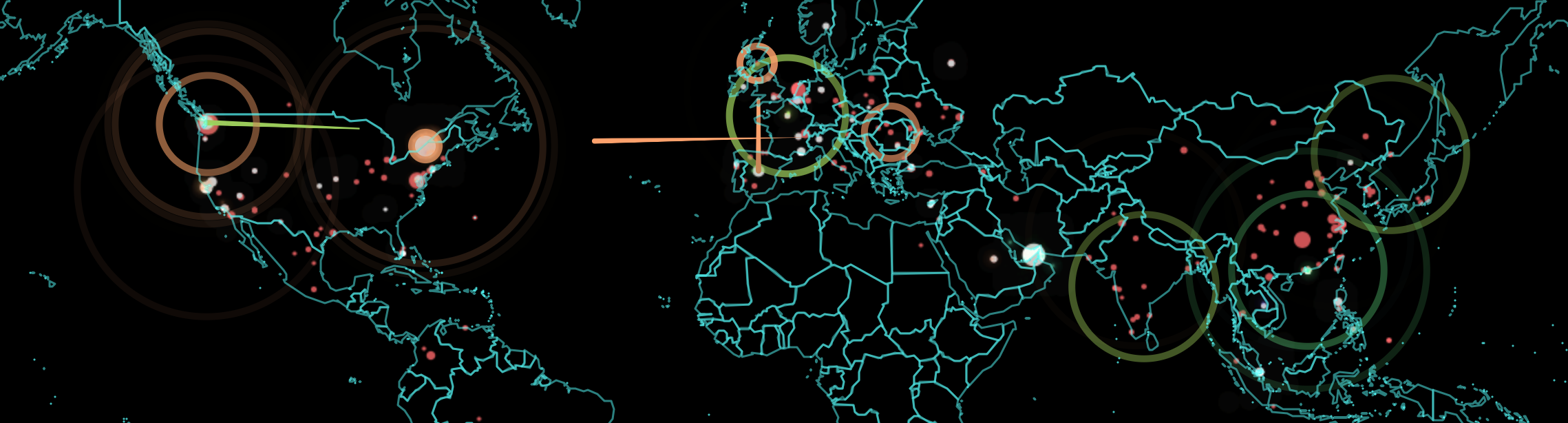
We can now watch the spread of internet attacks in real time, looking at the threats of hacking in real-time, in ways that reflect the emergence of the internet and World Wide Web as a real-time battlefield, even if this is only a representative tracking of hacking attempts tracked by Norse. It doesn’t include the ten millions of daily attempts to hack into the Pentagon, or the similar number of threats that the National Nuclear Security Administration tries to fend off–and the millions of attacks universities daily confront. But if we are apt to be mesmerized by the range of such attacks, impossible to fully comprehend or track, we’re likely to be overwhelmed by the serious fears of the security vulnerabilities of which they cannot but remind us, although the abstracted sense of a constant barrage of online attacks can remove us from all too real dangers of their infrastructural effects–and the dangers of destabilization of specifically targeted strikes.
And if we might do well to take stock of the range of attacks by hackers to which the United States is vulnerable, mostly from China and Chinese sources, privileging our country as the target of future strikes–
–we loose sight of their increasingly global nature, now that much of the software to exploit vulnerabilities is available in the Dark Net. The origins of such attacks aren’t really clearly able to be mapped–hackers are experts at deflecting or rerouting their signals, and bouncing around their traces to make hacks that are located from one site appear to emanate from another from another. And infrastructural vulnerabilities of infrastructure are increasingly on the table for nations other than the United States, often without the means to monitor such cybersecurity issues or strikes.
In an age when the pathways of internet links may have spawned spontaneous revolutions, uprisings, and unexpected results of elections, non-human communication and propagation of such malicious malware viruses seem an apotheosis of the absence of any agency–a worm that is able to replicate itself within hard drives world wide, removed from any intent. To be sure, the range of sped-up animated maps to track the progress of the viruses that compromised data across the world produced a sense of wonder at our vulnerability of a sort that has not been widely mapped since the Cold War: the images generated of internet threats mirrors the map of the danger of missile strikes that emerged in Life magazine back in 1945, at the end of the Second World War–only months after the destruction of Hiroshima and Nagasaki by American atomic bombs, that increasingly stand as a premonition of the new nature of things to come.
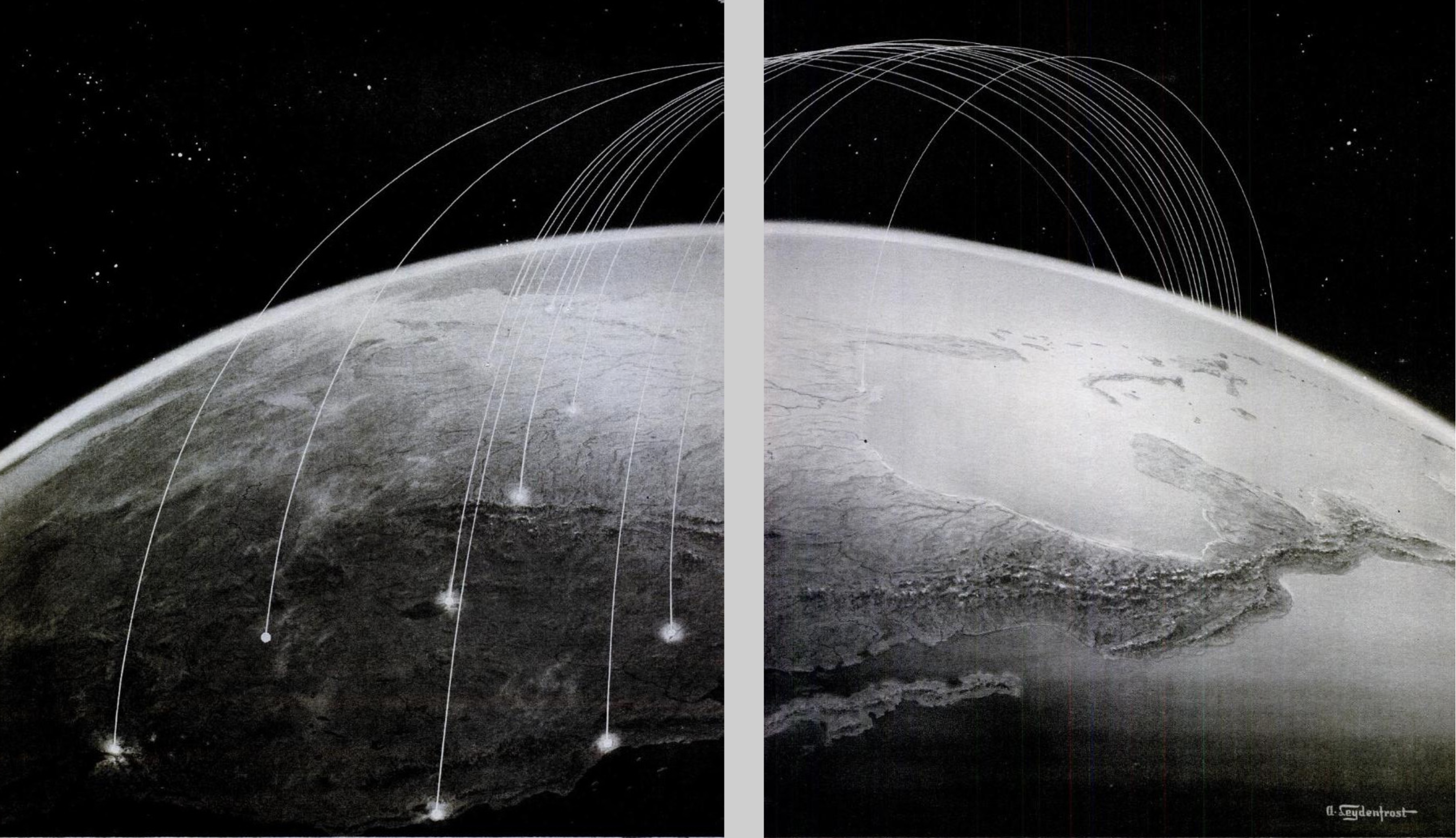
Life Magazine: The Thirty-Six Hour War (November, 1945)
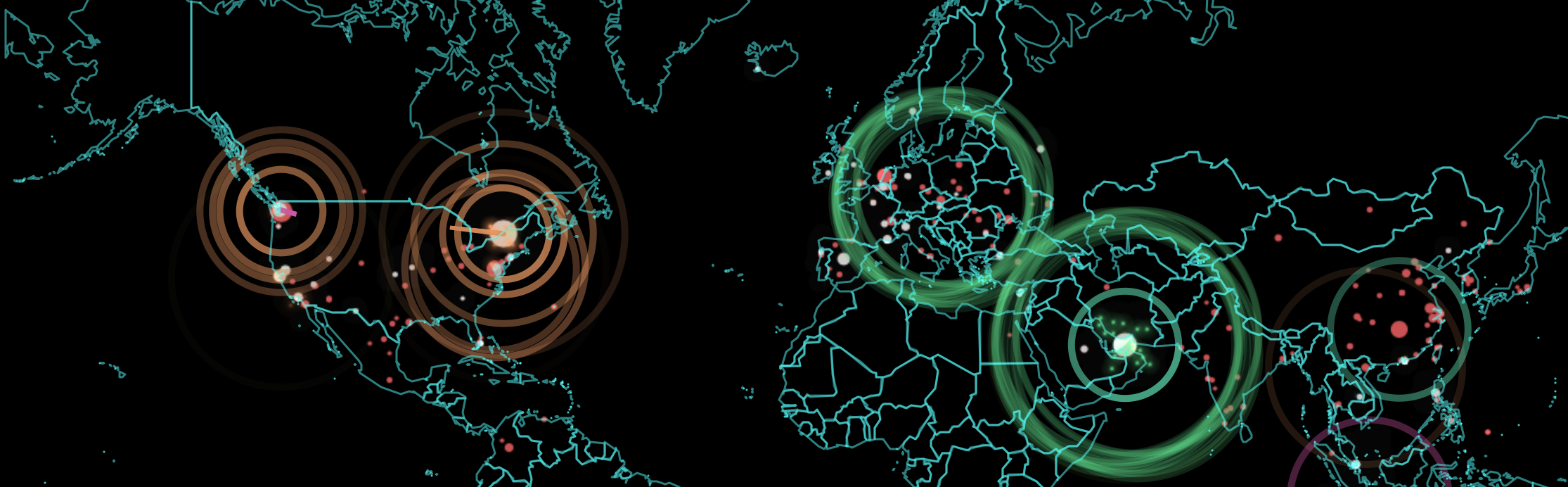
Mutatis mutandi, the image of the visual culture of the early Cold War was adopted by the Russian internet security agency, the Kapersky Labs, as a strategy to image the globally expanding threat of hacking to compromise hard drives and data-based systems.
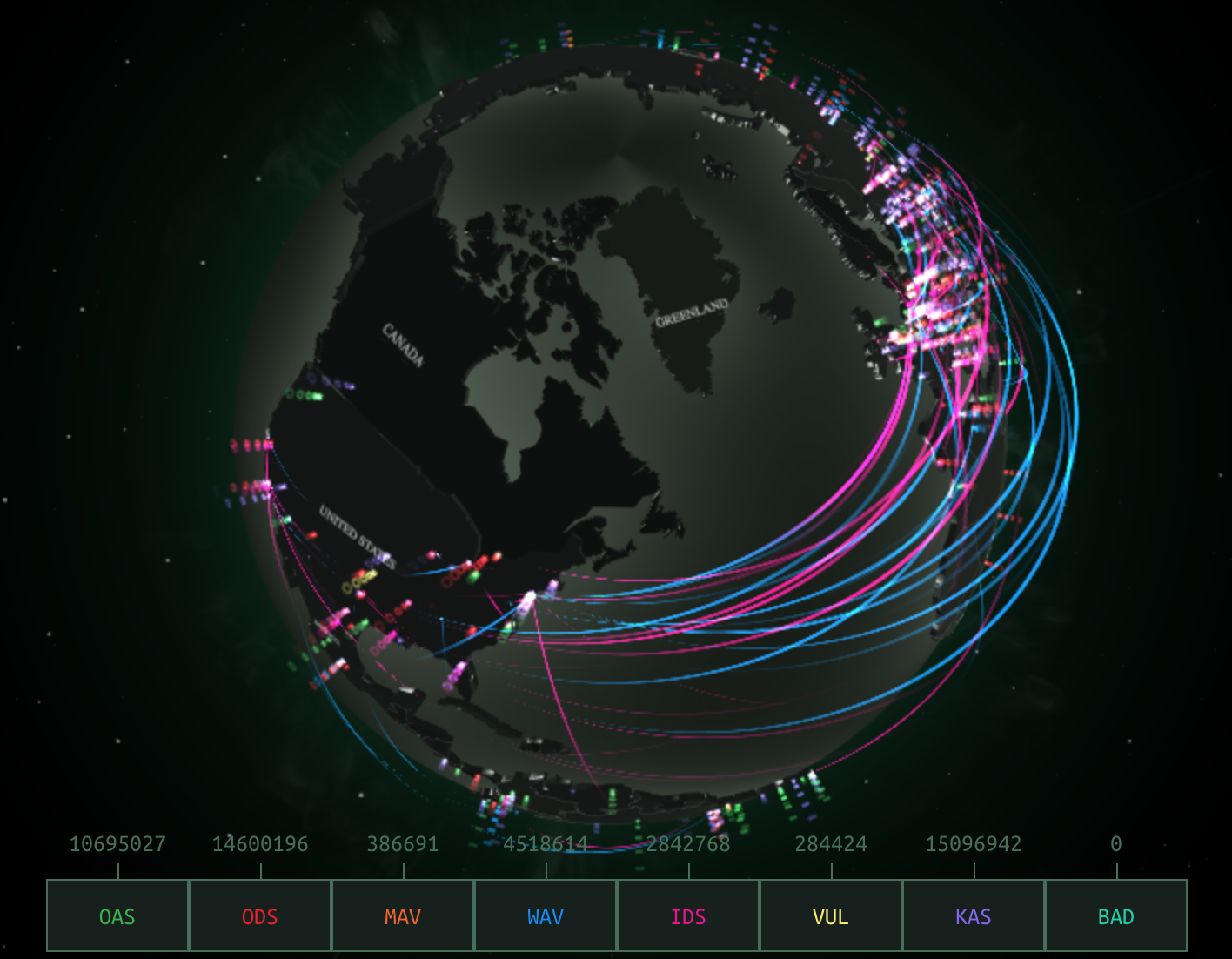
In an era that was defined as after or following the thaw of the Cold War, the internet emerged in 1990–just a year after the fall of the Berlin Wall heralded its thaw–as a new battleground to wage global conflict. To be sure, the cybermaps of phishing schemes and potential email attacks are traced by the Kapersky labs in real time, to monitor for global security on the interlinked world-wide online systems. But their dynamic images retain the symbolic structure of the arcs of a violation of national airspace to suggest the magnitude of the incursions into cyberspace they monitor and report on round the clock.
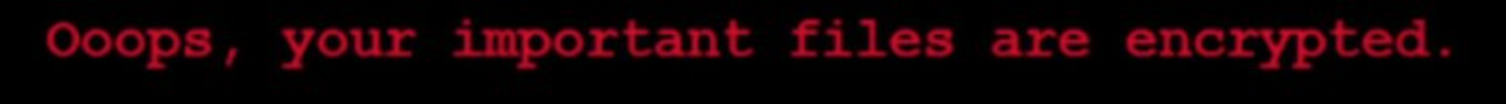
We continue to map the global spread of malware as if to wonder at its scale: the distributed compromising of data as an animated sequence of simultaneous flare-ups of intensity from yellow to burning red across the world, as if to pose the question of its communication in terms of spatial continuity and proximity. In some of the best data visualizations of the scare of WannaCry and Petya viruses, the brightly burning flare-ups signalled a fire that burned so brightly to become impossible to contain as if a metastisizing online cancer spread across the world’s wealthiest regions. Despite the power of the animated visualization, we may map it wrongly, as if to imply it can be diagnosed as a spatially transmitted contagion without a target or destination. In using the data-laden information of cybersecurity firms to map the occurrence of data corruption and systems infection, the political antagonisms and animosities that have fed the growth of malware are cunningly left absent from the map at our own peril.
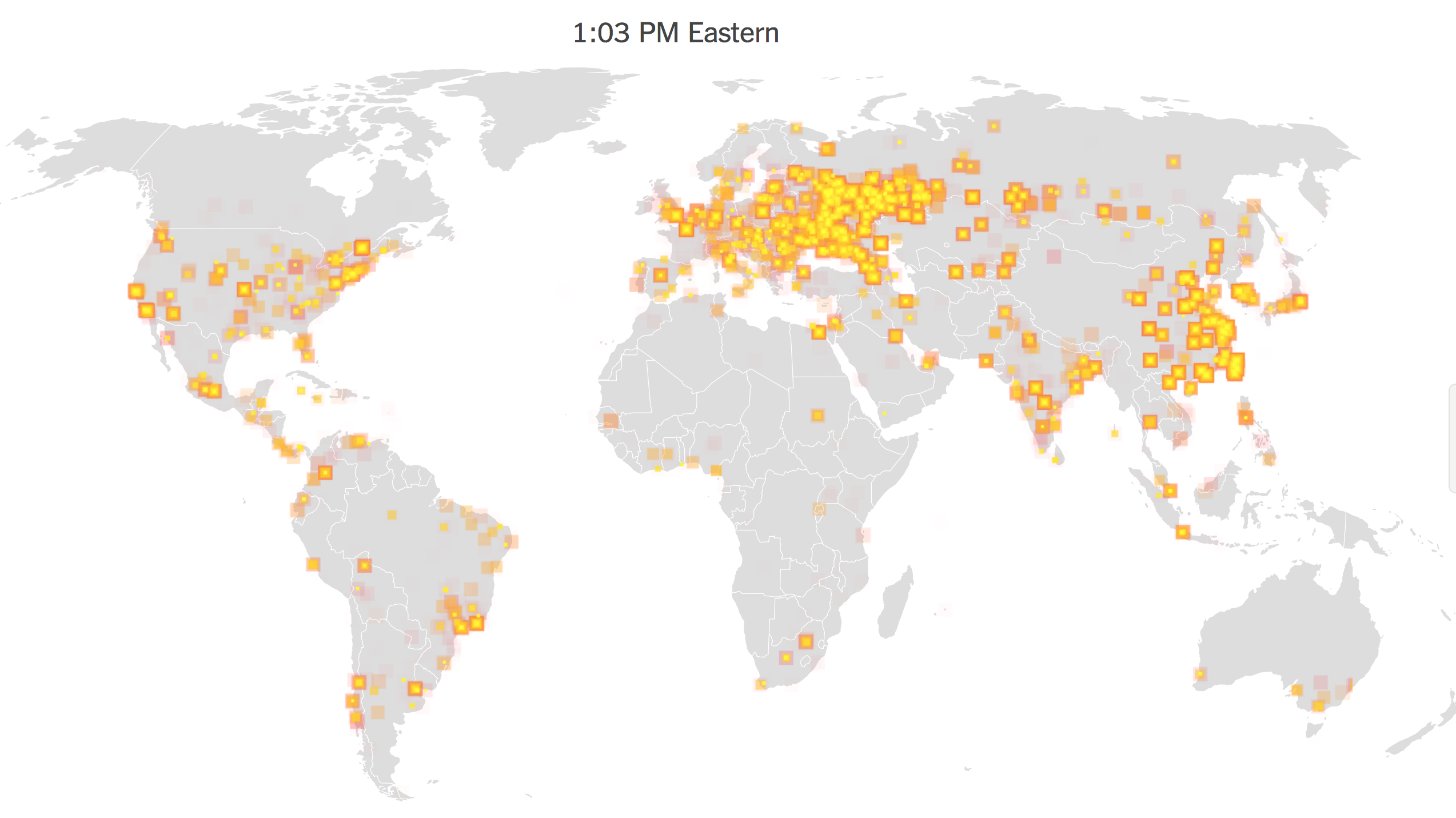
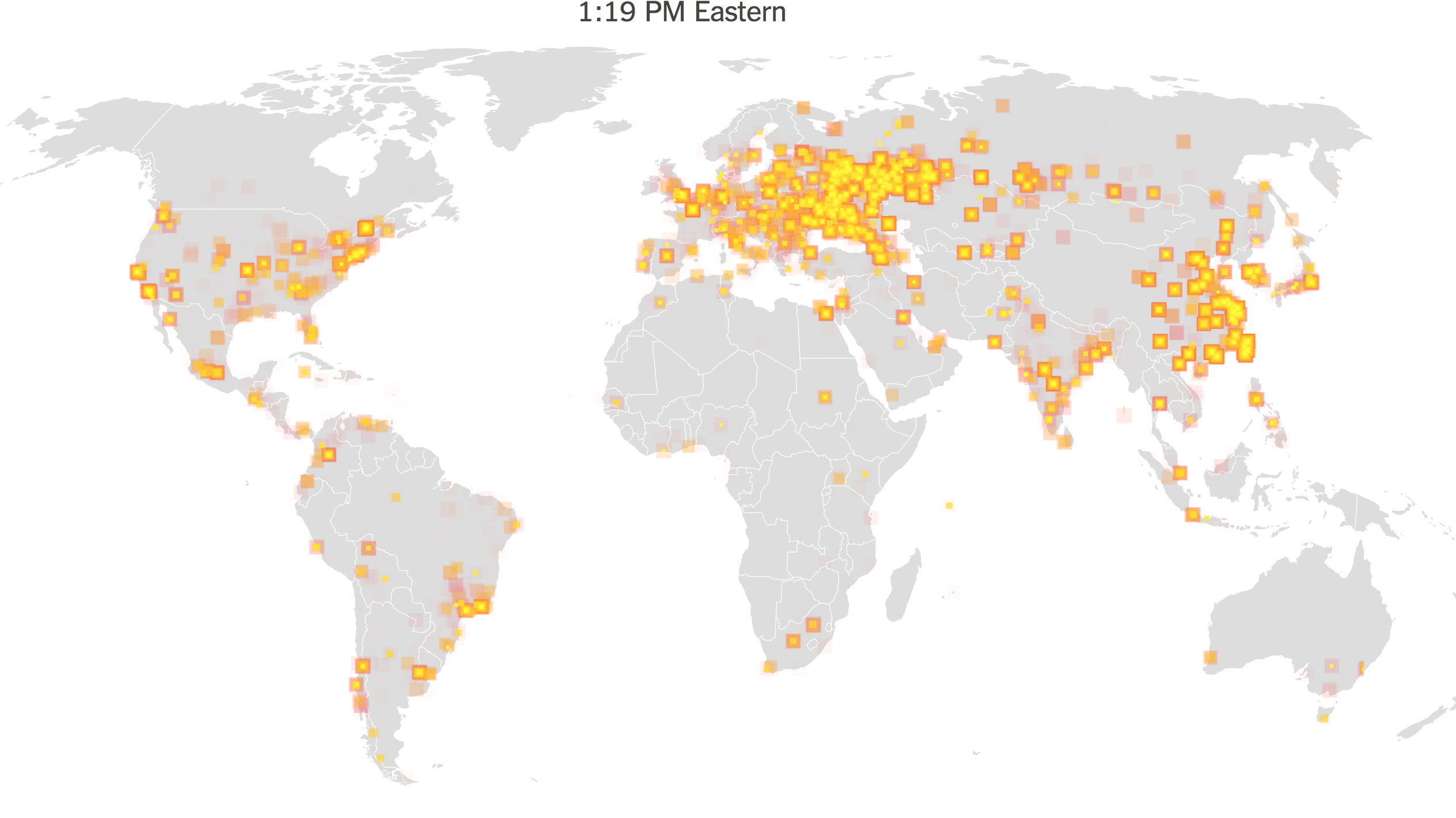
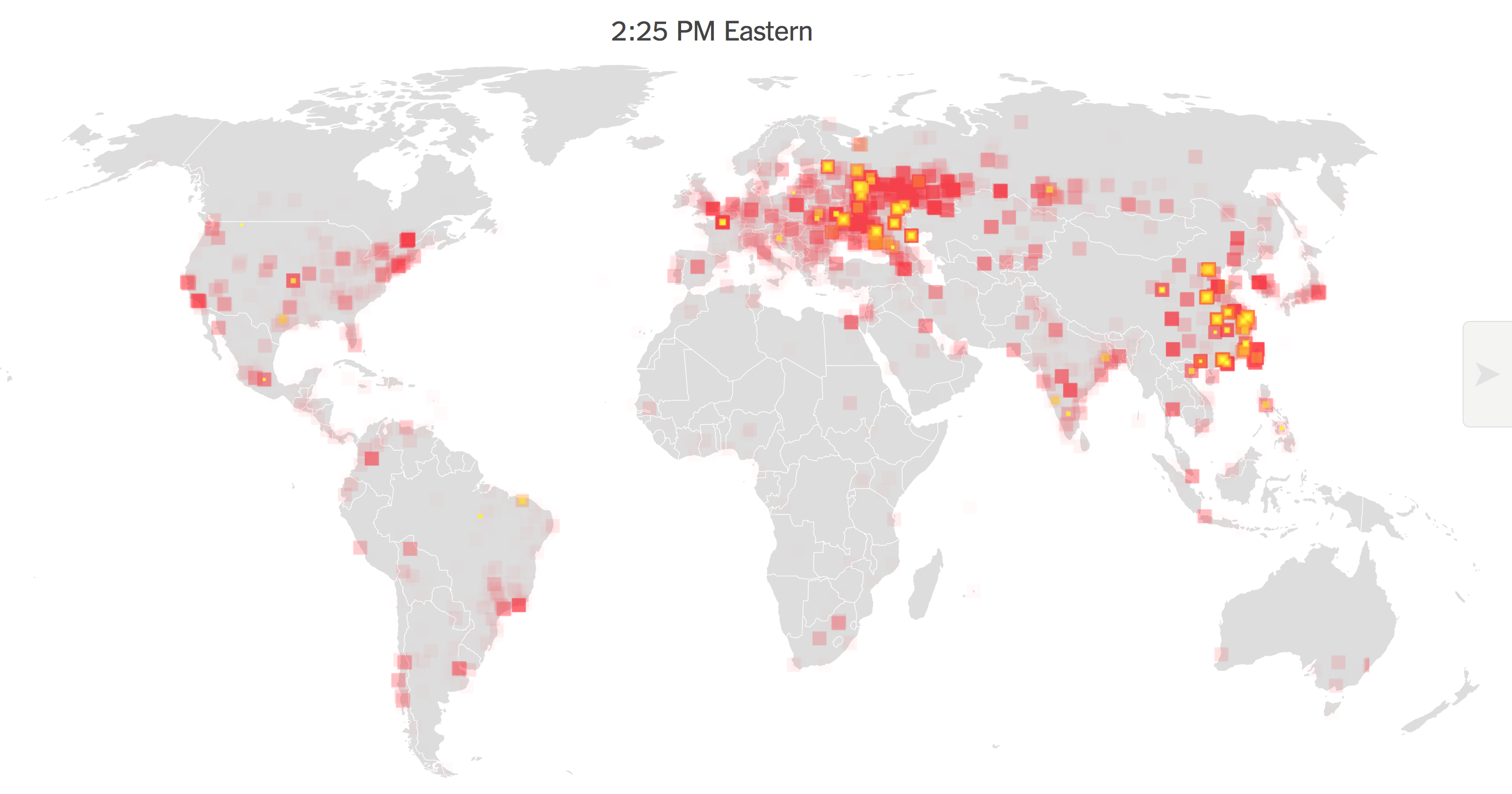
Although these maps suggest the scope and nature of the self-replicating cryptoworm, they may take the metaphorical value of a computer virus in literal terms, as a disease map, or biological virus whose contagious could be explained,–like the famous Snow Map, created by a founder of modern epidemiology, Dr. John Snow, to devise a mode to convince readers of the transmission from a water source of the 1854 London cholera outbreak. Of course, the malware maps do not try to communicate the pathways or mechanics of the virus’ spread. For rather than showcasing an event that was planned and of human agency, and whose propagation was in some sense designed, they run the risk of naturalizing both the incidence of systems’ compromises and the malicious nature of the very phenomenon that they describe. While the meaning that each bring pixel cannot even be understood or processed in a global scale–its impact was local–the intensity of the outbreak seemed almost a skin disease on the surface of the world. The intensity of its transmission surely mirrors the density of online connections or an economy that was web-based, as networks allowed its contagion spread from Indonesia to Europe the United States, raising alarms as it seemed to actualize some of the worst fears of a cyberattack, of the de-empowered nature of a computer system suddenly devouring its own data, but like a faceless god, from 11:00 one Friday morning, so that by 1:20, the spread of the malware had dense sites of infection on five continents.
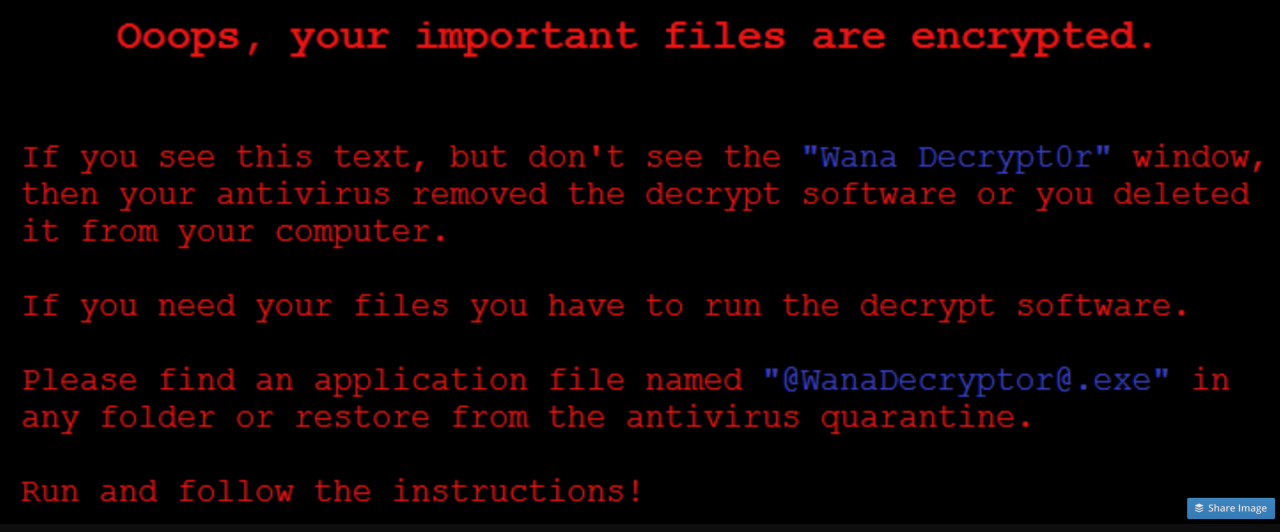
The local merged with the global, however, in ways difficult to map: the maps of real-time tracking of the spread of the worm across a grey, global map made it seem totally removed from human actors, in hopes to capture the speed by which the worm managed to rapidly to spread laterally across systems, using an onslaught of randomly generated IP addresses as a way to target an ever-proliferating range of hard drives through multiplying packets sent to remote hosts, whose own hard drives were hijacked, leaving anonymous-sounding messages of no clear provenance to pop-up on users’ screens, in ways that seem to imitate the “normal” logic of an algorithmic process entertaining the possibility of implicating the user in the encryption of their hard drive or the deletion of necessary valuable files.
The communication of the virus–a biomedical metaphor that seemed particularly unable to offer any diagnostic value, suggesting either the banality of the infection or its nasty spread–was not nosologically helpful, but suggested the virulence of its spread. The natural history metaphor of the worm–or, better yet, the coinage of the cryptoworm–better expressed the lack of clarity as to its provenance or the seriousness of its damage. Although subsequent investigations found that the first infections appeared, globally, on computers in India, Hong Kong, and the Philippines, according to SophosLabs, the stage was set for a three-pronged global spread–as if in a negative version of the Trans-Pacific Partnership, moving from South-East Asia worldwide–that began from 7:44 UTC with such startling rapidity that it will demand detailed unpacking to understand the target or decipher any of the aims that underlay the attack, or the extent of its destructive scope. The spread of the self-proliferating worm was only stopped by the inadvertent discovery in the code of the ransomware of a kill switch, which allowed a security researcher known only as MalwareTech to register a domain name able to slow the spread of the infection in a compromising manner, effectively halting its viral spread. Despite the rapid proliferation of visualizations of the unprecedented sale of its virulence, in retrospect, it might make sense to ask whether the undifferentiated global nature of the visualization, while stunning, distracted from the malicious operations of its code, and what better metaphors might exist to describe the spread of something dangerously akin to cyberwar.
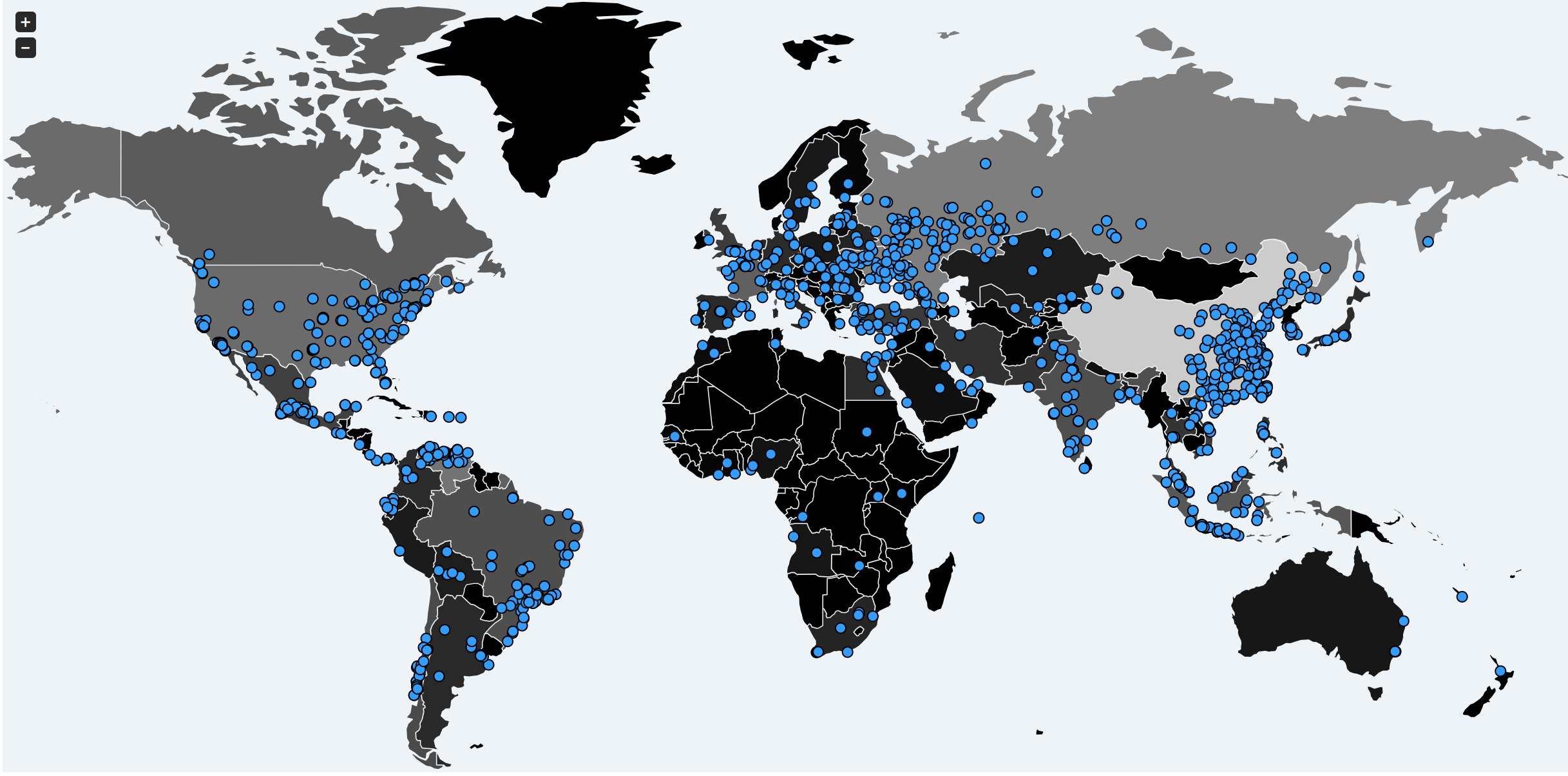
We only have a few cartographic metaphors to describe the lateral spread of online compromising of computer data and the infiltration of networks, because of the speed with which it spreads challenge human cognition. Even if it can be schematized in a format that suggest the density of data compromises or the amount of encrypted files, the visualizations offer a limited basis to orient oneself to the seriousness or the danger of these infections, which once they start offer little possibility of stopping their spread. The later visualizations of the global impact of the release of Wannacry network worm are usefully foreground the rapidity of its spread, and raise the specter of its unstoppability. But the visualizations of the rapid flare-ups of malware that infect hard drives and encrypt their data may conceal the targeting of instability. If the spread malware and ransomware have been primarily linked to extortion, the spread of self-propogating cryptoworms cannot only be seen in numbers of systems compromised: for they are released and created in order provoke instability, as much as for Bitcoin revenues. Although theft of data is usually seen as most valuable to the owner of the dataset, the potential interest in ransomware as a service–and much ransomware is now available on the darknet in different forms, suggests a needed growth in cybersecurity.
If ransomware collectively netted about $1 billion during 2016–and stands to become a growth industry of sorts–the latest Petya virus netted but $10,000, although the benefits of the attack might have been much greater–in the form of the disruptions that it creates, often not so clearly racked or visible in the data visualizations of its spread, whose animated explosions suggest its out of control migration across networks as wildly crossing boundaries of state sovereignty, encrypting data on computer systems across space as it travelled along the spines of the internet as if without any destination, as tens of thousands od systems were entered and compromised via ‘back door’ disrupting hospitals in the UK, universities in China, rail in Germany, or car plants in Japan, in ways that were far more easy to track as a systems collapse by locking its victims out of critical data that allowed their continued operation. The demand for ransom payments to restore apparently stolen data was a screen for the disruption of invasive attack on companies’ computer networks, whose compromising can only start to suggest the infrastructural disruptions they created as they rapidly globally spread, whose apparently anarchic spread revealed the new globalized nature of system vulnerabilities.
While malware is distinguished by the demand to hold hostage the encrypted files of one’s hard drive, the viral spread of worms targeting systems vulnerabilities can disrupt systems and infrastructure in ways particularly difficult to defend against. Although the attacks depend on failures to update systems and to preserve retrievable back-ups, the vulnerabilities invite disruptions on a scale only so far imagined in futuristic films. These apocalyptic scenarios are perpetuated by security firms–and by the video games of the global imaginary that require only greyed out background maps to treat data visualizations as having sufficient complexity if they register the intensity of attacks, even if this only gives cover for the malicious actors who perpetuate their spread. But the assault on systems by the backdoor vulnerability first discovered by the NSA, in its program for targeting and infiltrating select foreign computer networks, but now for sale on the Dark Web, may only raise the curtain on a far more malicious range of malware, able to backdoor systems that are connected to transportation networks, water treatment plants, traffic systems, credit card systems, banking and airport controlling, far beyond cel phone systems, and able to–as the attack, just before WannaCry plagued web-based systems, compromised IDT Corporation–evade security detection systems. While regular, complete and restorable systems back-ups may be the only response to ransomware, the possibility of already backdoored systems has lead to fears that the Shadow Brokers group who unleashed the Eternal Blue code from the NSA is a group of Russian-backed cybercriminals, and the hackers who released WannaCry who cyber researchers believe have tied to North Korea, may raise the threshold on cyberwarfare of a scale unheard of in previous years.
“Nothing in the world could take us back/to where we used to be.” Golan Ben-Omi–who views the analytic skills honed in studying Torah as good training cybersecurity in the Chabad-Lubavitcher community– Chabad-Lubavitch communities are interested in preserving the integrity of their websites from profane pollution, but are attuned to the dangers of data breaches. The attack that was made on his company, IDT, by means of an NSA tool with the capacity to penetrate computer systems without tripping alarms–named “DoublePulsar”–enters the kernel of computer systems, or its inner core, to trip the connections between hardware and software that would allow hackers to steal systems credentials in order to compromise systems with far greater impact than earlier breaches and infections, appearing as ransomware, but perpetrating far more serious damage on a system. The sequential flaring of compromised computer hard drives suggests a landscape that Ben-Omi has been studying for over fifteen years–and believes that the analytical skills honed in the study of Torah will allow his students to analyze.
While we lack the tools to start to map disruptions on such broad scale, the If the attacks on hard drives that occurred in over one hundred and fifty countries on Friday, May 12, 2017 may have been a case of intentional disruption, but the Petya ransomware attack of July, which successfully targeted the same vulnerabilities, exploited similar vulnerabilities in a potentially more targeted weaponized manner. Although it “is only code,” the lateral spread across the spines of the internet created fears of impending disaster across the most digitally rooted areas of the world, spreading fears of data disruptions, crashes and infrastructure collapse whose potential won’t be able to be so clearly mapped for quite some time.
The terrain of the crypto worm’s spread is better able to be understood, if not quite familiar. During the most recent space of malware attacks left most untouched places those farthest from the most unreflective internet-dependent, the map only can suggest the real-life inconveniences that can hardly be captured by the burning flares of yellow-red bursting at spots across the globe at unprecedented velocity.
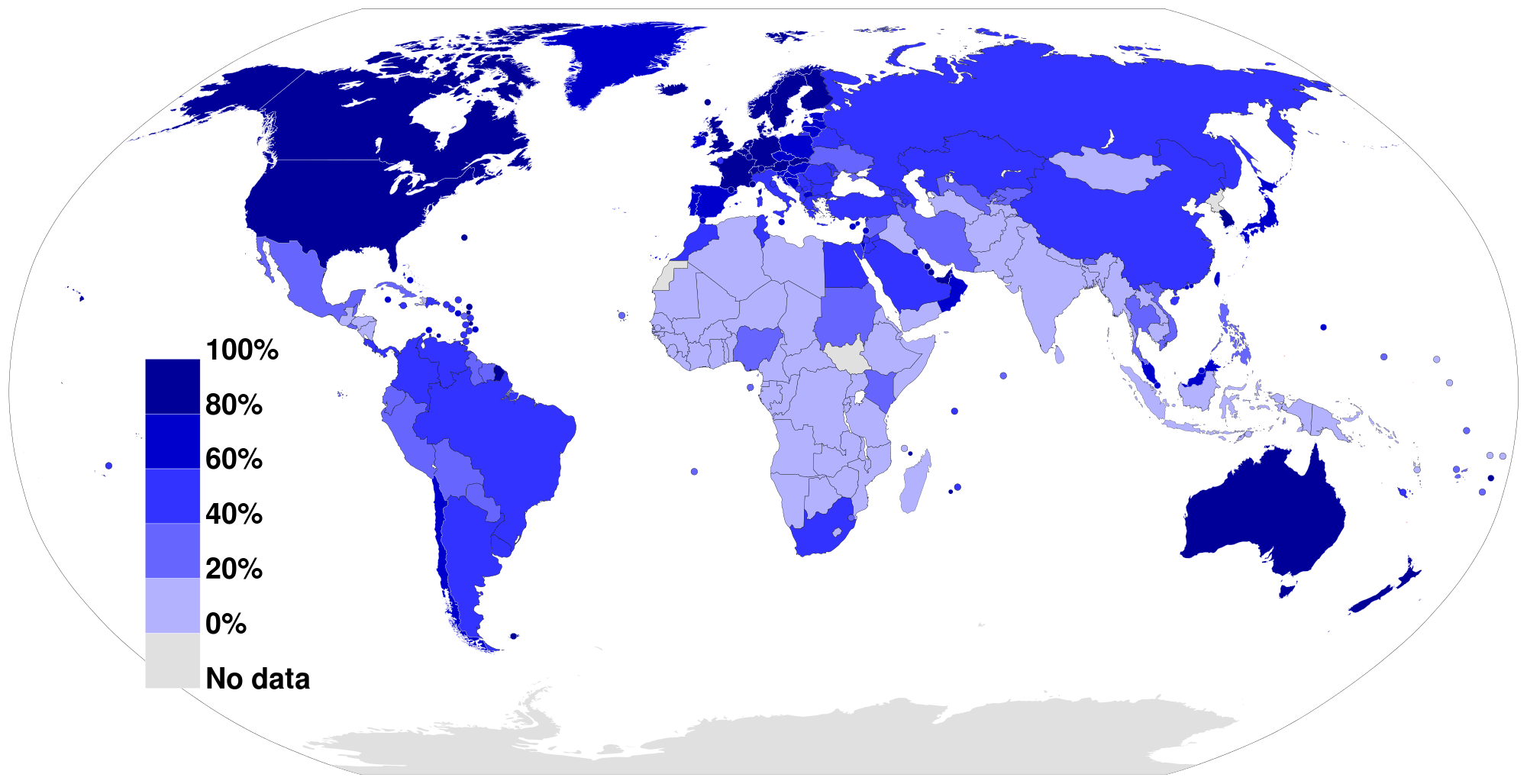
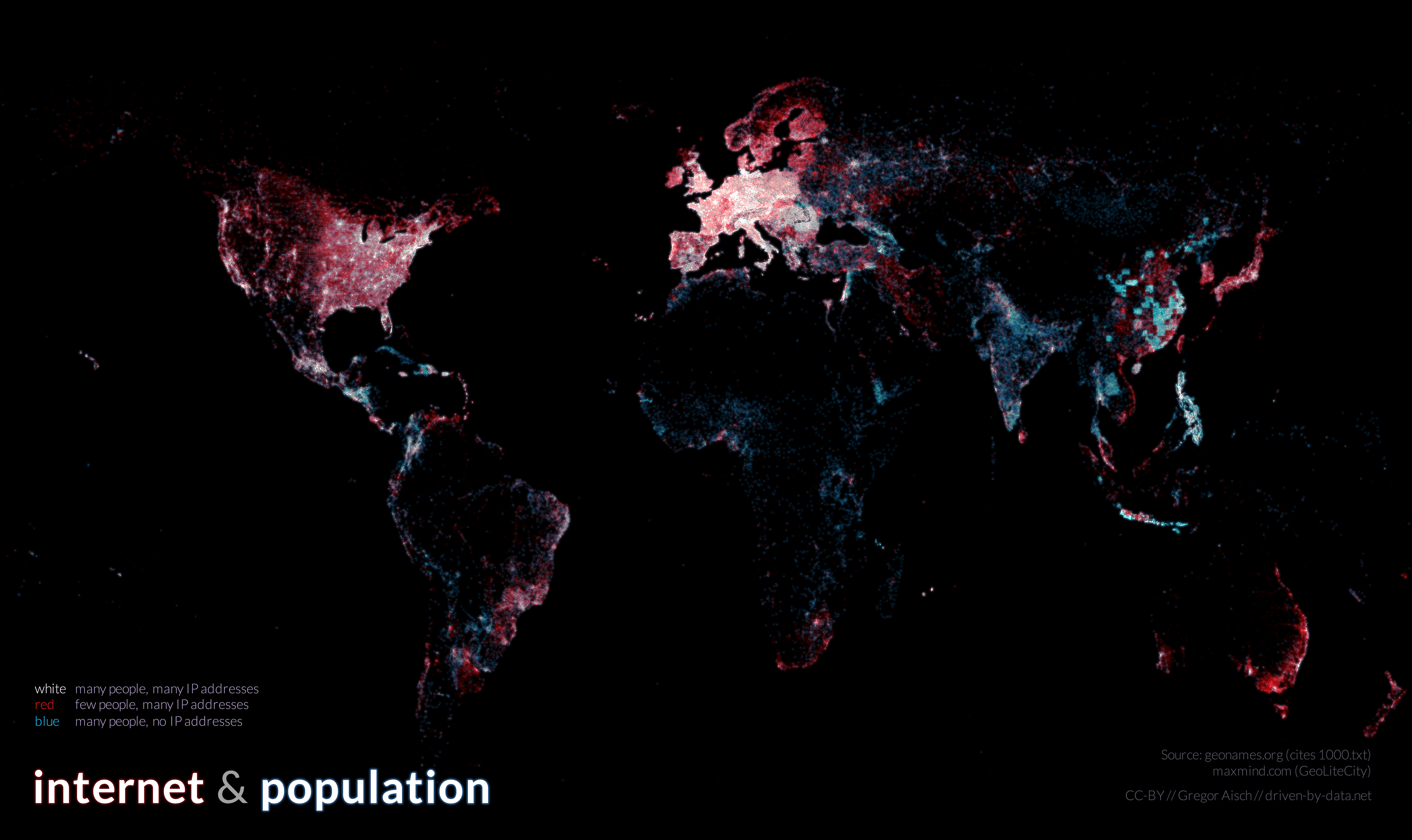
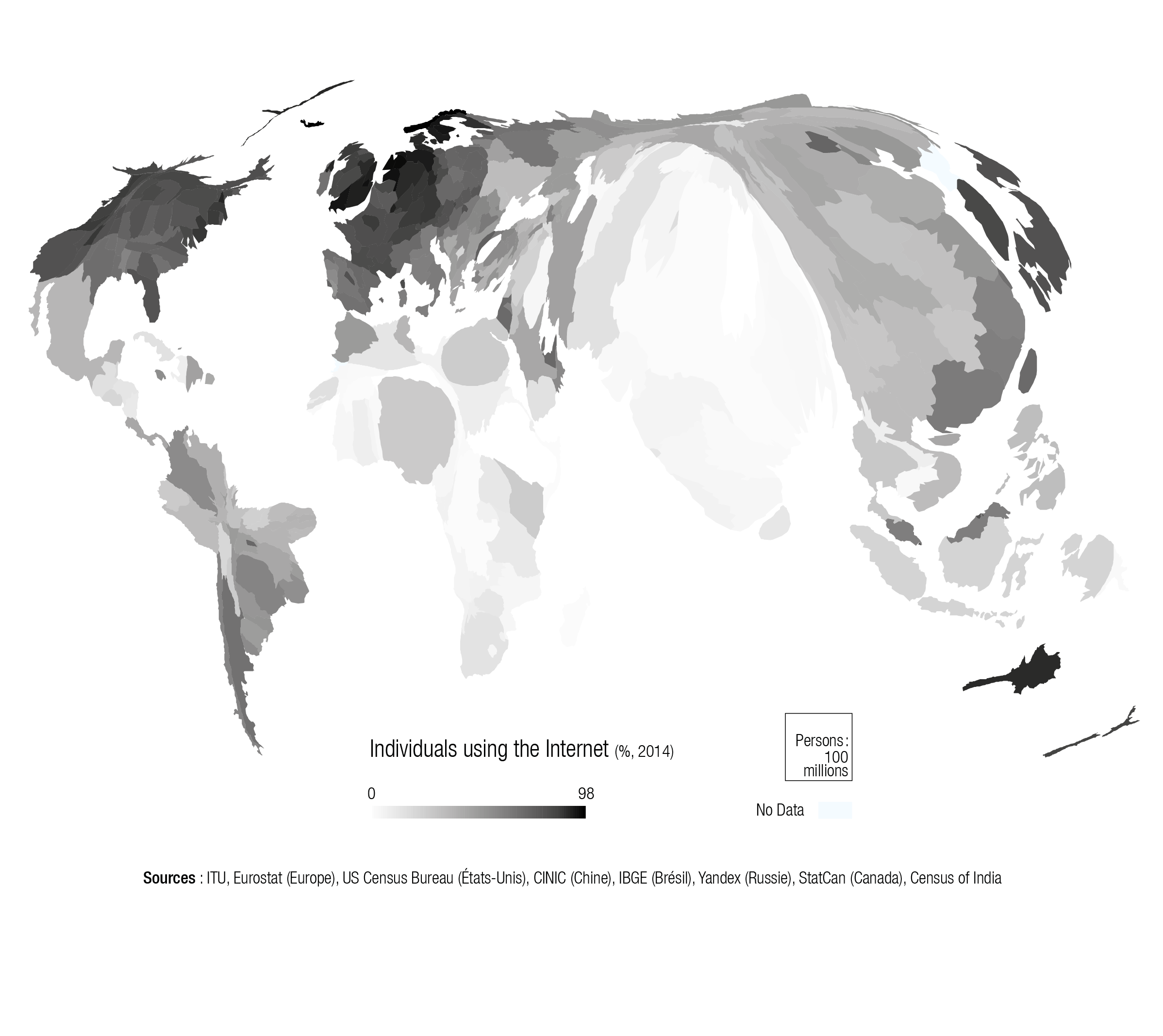
Global Internet Penetration 2012/Jeff Ogden
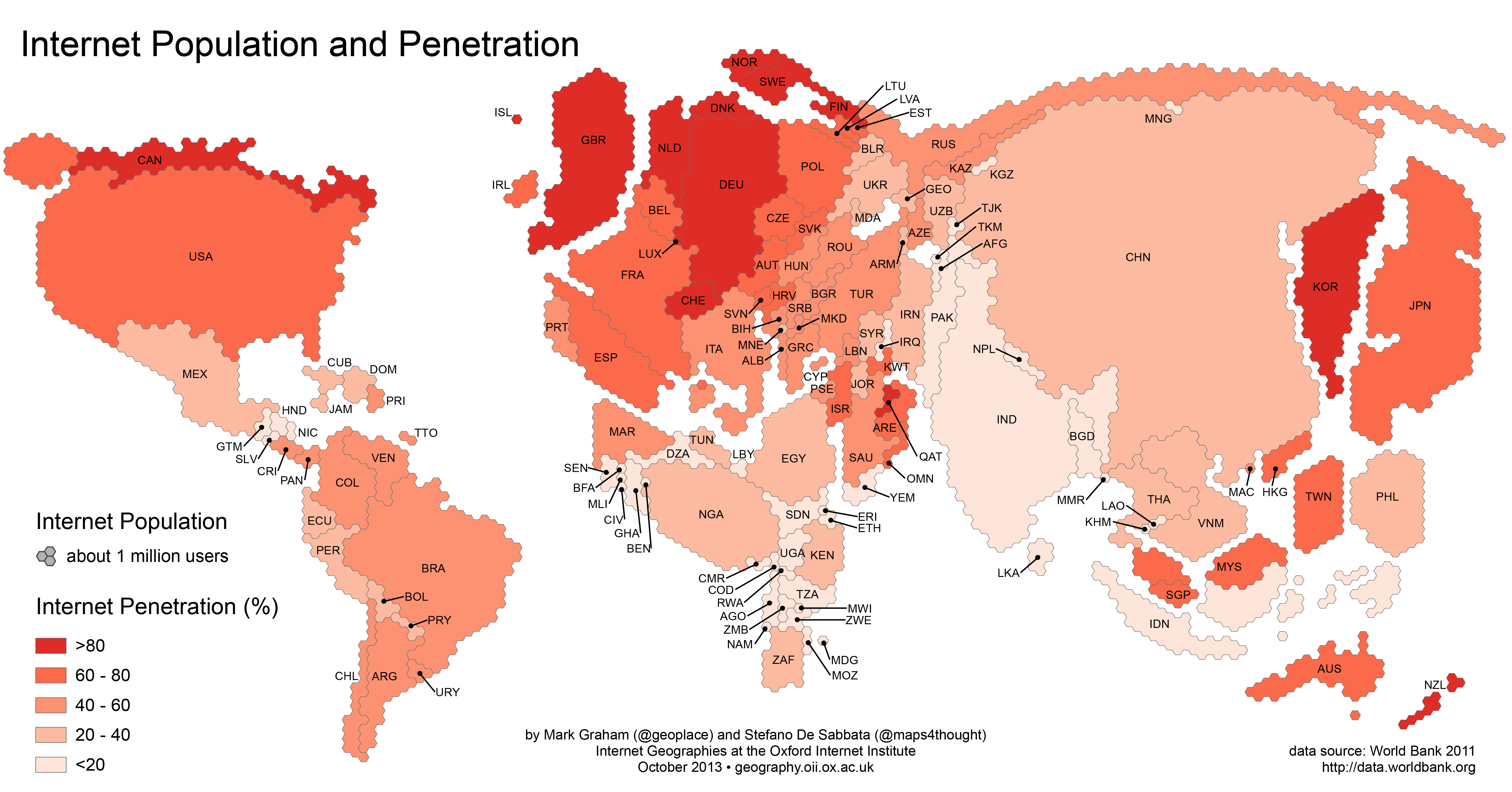
Oxford Internet Institute (2011) Data on Internet users and population from World Bank
For while not only communicated–as at first believed–by malicious email attachments, internet links clicked by users whose unreflective response unleash lost data, frozen systems, or looted bank accounts, the spread of ransomware parallels the amazing intensification of net-dependence and systems-based communicative tools, revealed below in the new information ecosystems that have arisen, illustrated in the quite spread of Facebook use over a short amount of time.
The relation between online activity and real-time consequences are difficult to map.
All maps serve to help tell stories, and the intensity of Facebook connections suggest more than a huge time-suck of human lives: it reveals the increased homogeneity of the systems we use, and the similarity of what we see and read. But if all maps tell stories, the necessarily partial nature of the dense visualizations of the global disruptiveness of malicious attacks on computer systems seem compromised: while over-laden to challenge the abilities of viewers to process their content, they only tell the most superficial part of real-time story–the compromising of data–and not the consequences that the widespread collective compromising of hard drives will effect both immediately and in the long run. And here we get onto thin ice in terms of what can be visualized, and the limits of counting the datasets of the corruptions of computers or systems, and the difficulty of counting beyond the density of compromised hard drives to the real-world implications of systems’ collapse. One can only start to imagine the implications of such collapse in maps contracting the real-time compromises of computer systems, in ways that reveal the global nature of an infectious spread of malware, but also obscure the different places that might be targets of weaponized malware attacks.
What we can track is the most immediate end-product of the malicious attack, but it offers few clues to interpret the basis for the attack or indeed the different scale of its real-time long-term consequences.
The visualizations track an almost near-inevitable progress of red flares in internet-dependent hubs that appear to overwhelm viewers with their over-laden information in ways that run the risk of obscuring any sense of human agency–or intent–as if to track the spread of a virus across a system that lacks internal logic of its own. The intensity of attacks on computer networks tracked from the Wannacry ransomware showed the astoundingly rapid spread of the infectious cryptoworm that caused the attacks. But it presented them as if they were in fact geographically localized, but the disruptions were purged of any explanatory context, geopolitical or other. For the inevitability of the spread of malware that the images provoke–and the fears of the unstoppability of further crypto worms–may obscure the dangers of their weaponization. If the launching of cyberthreats is often depicted as a real-time war by cybersecurity firms as Norse–
–we may be increasingly in need of mapping the intersection of such live attacks on data and their real-life consequences beyond the compromising of datasets.
We were recently warned how the expansion of malware and ransomware would soon propagate over networks in more virulent ways. Earlier worms that infected hard drives as Conficker in 2008 and SQL Slammer back in 2003 or SamSam, spotted in 2016, offer but “a harbinger of a new wave of more malicious, tenacious and costly ransomware to come,” of even greater scale, warned Joe Marshall of Cisco Talos, with “bigger payouts.” Marshall warned of the greater goals of hackers to infect networks, and his warnings might be augmented by suggesting the dangers of hackers working with governments to use malicious code to “cast a wider net” through self-propagating crypto worms able to laterally traverse huge corporate networks as tools by which to target nations–and national infrastructure–in ways that the fear of network intrusion have only begun to come to terms. When Marshall and his co-author Craig Williams noted in 2016 that the rise of ransomeware was an “ever-growing problem” that will involve greater payments to restore databases in Ransomware: Past, Present and Future with greater “intrusive capabilities,” with the repurposing of network vulnerabilities, on a massive scale, presumably including the targeting of entire systems. The maps of data encryptions and corruptions that WannaCry caused worldwide served to capture these fears, and their broadly trans-national consequences; the trans-national nature of such a strike on hard drives may well obscure and conceal the strikes and intentions of other malicious actors. Although some believe payment the easiest option to retrieve data, as the worms are developed that target vulnerabilities in systems, they will potentially be able to compromise targeted banking, transportation, and emergency infrastructures.
Do visualizations of the immediate fears of the spread of one virus conceal concerns of the weaponization of such internet-born infections on specific targets and nations, despite the seemingly unplanned ubiquity of their spread across interlinked systems? Despite their shock, such visualizations of the intensity of compromised systems, often echoing hubs of internet service, raise pressing questions about how to map the operations and actors behind them that are far more complicated to process fully–and lie off of the map.
1. Viewing visualizations of such rapidly spreading worms that compromised computers on a global scale, one wants to be able to peel away layers of the visualization, to reveal, as layers of an onion, the networks along which the cryptoworm laterally spread and the extent of disruptions that its spread caused. For the scale of the disruptions, and the intent of the hackers or those who launched the malicious code, may only be revealed in a more localized map of the sorts of destabilization that cryptoworms might produce. While leaving us to wonder at the unprecedented scale of their recent spread over a few hours or minutes, the visualizations take geographical space as their primary register, blank background maps bleached of underlying history, may make them all the more misleading and difficult to read, as they are removed from human agency and context, and treated as an artifact of the spread of the reliance of increasing multinationals on internet services and web-based networks.
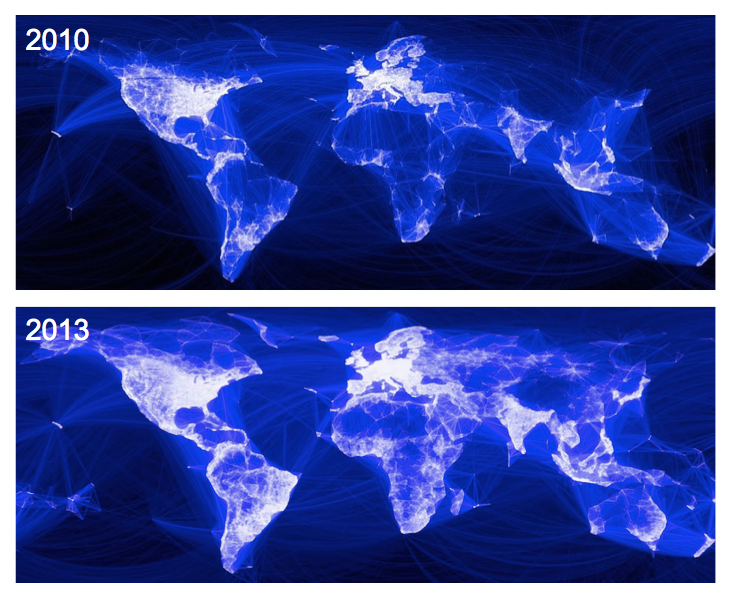
Differences in online activity are far less lopsided across geographic space than in previous years, as shown by the Oxford Internet Institute by a cartogram warping of global space showing the relative density of online activity by 2013 data, in ways that allow the broader targeting of systems to conceal a malicious attack on a country.
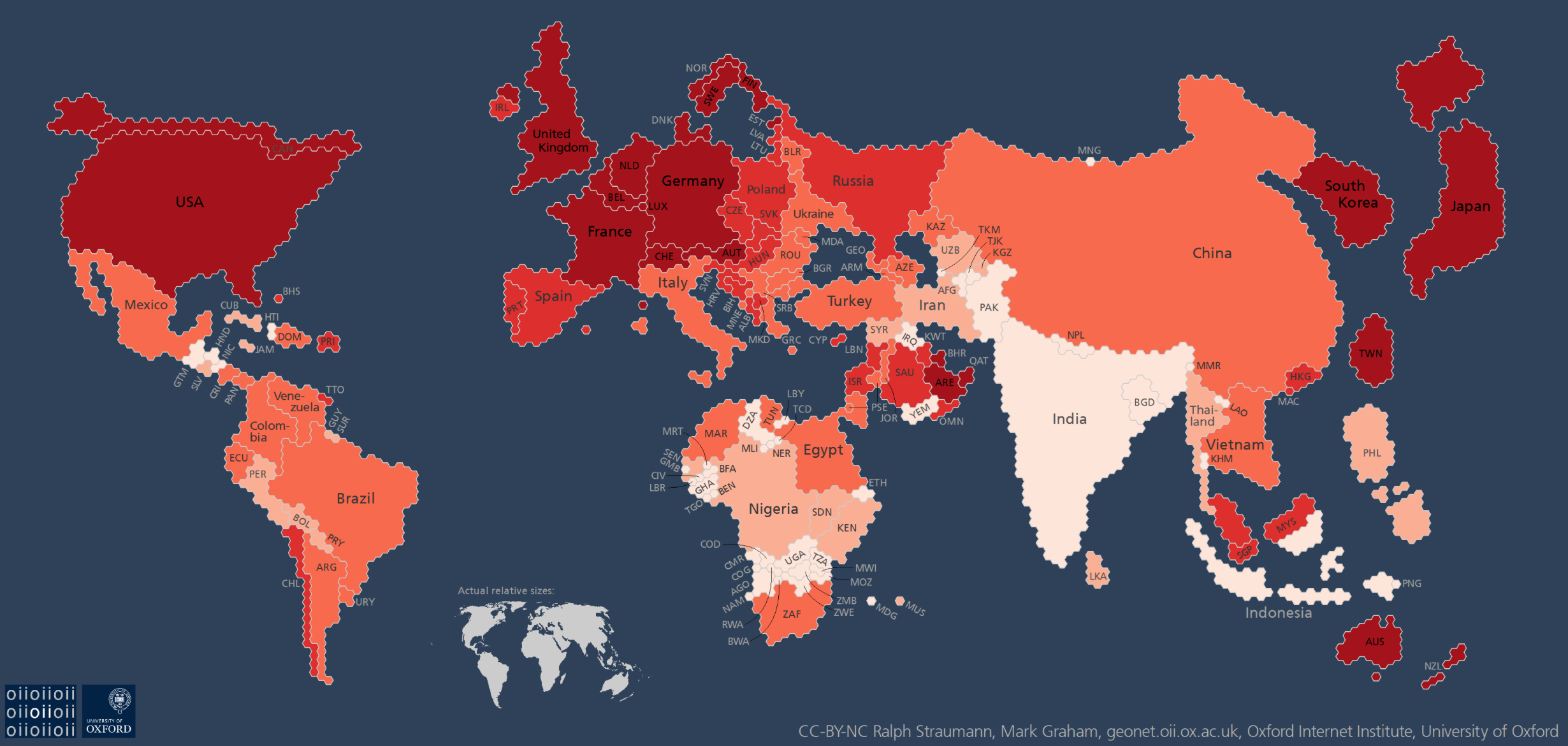
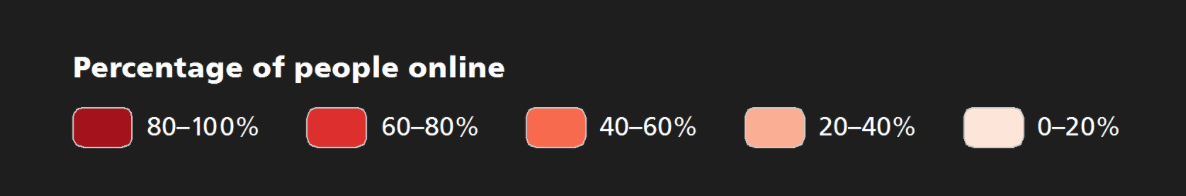
–which might also be read as a record of the increased vulnerability of specific areas, and the systems vulnerabilities might offer to compromise local infrastructure, and start to focus on the implications for those places. Doing so would consider the growing intersections between The Real World and the internet in a complex social continuum, where stability can be disrupted at select nodes more dependent on how worlds of finance, banking, shipping, health, and traffic are increasingly interlinked. Given the inevitable nature of such vulnerabilities, the frequent backing up and smooth restoration of backups are necessary to erase the growing threats not only of malware or ransomware, but the disruptions of critical infrastructure future attacks might allow.
Mapping instabilities within this continuum are in a sense not new. But the mapping of destabilizations is not only an increasing concern, but is less easy to detect within a global map of compromised systems. In many ways, the shock of the spread of malware infections that was so difficult to process draw on cartographical metaphors of the weather conditions even as they show global networks of web-traffic. Yet despite their far more apocalyptic images of a global disruption of networks, and a loss of data as it is encrypted and removed from hard-drives in multiple nations at the same time. This makes it hard to focus on the geographies of disruption that they produce. For as much as raising terrifying questions about the potential pathways of digital disruption, can their global purview also conceal and distract from their targeted nature?
Indeed, the absence of control for the spread of infections that are able to evade firewalls and cripple multinational businesses worldwide seems their primary message. What if the global scale of such blooms of malware infections not only of limited forensic use, but actually able to conceal the targeted nature of many a malware attack? (Even though the Wannacry ransomware was revealed to suggest strong links to the Lazarus group in a few weeks, the mapping the virulency of the global spread of the virus was terrifyingly mapped by its broadly unpredictable spread to hundreds of thousands of computers.) But in an era when mapping global disruptions seem increasingly important, the proliferation of compromised data, the spread of such a self-propagating virus may be more dizzying–and attract for more mapping–than the less visually striking aspects of the targeted nature of a malware strike, revealed in how such online disruptions intersect in real-time with systems-run infrastructure.
Perhaps maps is not the primary optic to orient us to the information the contain, or to detect or discern the motivations of the intentionally disruptive attacks they stage. The immediate shock of the WannaCry and Petya attacks created an instant demand to visualize the speed of their attacks on a global economy. But the appearance of indiscriminate appearances in a rush of proliferating dots denoting compromised hard drives worldwide are hard to process: appearing as attacks set loose on the world wide web that seemed to raise the bar on cybercrime and posed to engulf multinationals in their own failures to preserve or back-up data in an easily retrievable manner, the spread of malware seemed a symptom. The readiness of western and American media to view the scale of the malware infections as a consequence of the interlinked international economy provided a dominant interpretive filter of open internet traffic, rather than regional history or the geopolitical map that might motivate such attacks and underlie their occurrence, as we all too easily cast hackers as the pirates of a new digital age. The global pathways of the proliferation of infections designed to compromise data, so recently augmented to unprecedented scale, may even provide a veil for targeted disruption of infrastructure and a weaponized attack.
Cybercrime offers a likely remote vector to disrupt local infrastructure linked to the public internet, by breaching security firewalls in ways that so rapidly proliferate to undermine human reaction time. Such was the intent, after all, of the Stuxnet computer worm, able to spy on and subvert industrial controls via a Microsoft Windows vulnerability, that was used to remotely target IP addresses at Iranian centrifuges suspected of nuclear enrichment, in a surgical strike on that nation’s infrastructure. If argued to exploit ties to the public internet, the innovation of Stuxnet was to allow the infiltration of operating systems thought secure–a “digital bunker buster,” to quote the German hacker organization known as the Chaos Computer Club, a large human rights technology group, created a new level in the “declaration of cyberwar.” The cyberattacks not only evaded the military protections of nuclear facilities to shift speeds of the centrifuges in a thousand reactors, and fatally compromise the function of the entire system, recognized as crossing a threshold of weaponized cyberwarfare in the possibility of attacking civilian infrastructure, previously seen only before in films, able to fool computer systems into not recognizing the attack’s existence or occurrence: the complexity of the single targeted strike provoked the creation of national cyber defense centers protecting against targeting industrial infrastructure or internet disruption.

Iranian Military Defenses of Reactor in Natanz Targeted by Stuxnet
For the unprecedented scale of digital disruption seemed removed from geopolitics. By casting the work of cybercriminals as the pirates of the digital age, using ransomware to extract and encrypt data from their users, we run the risk of failing to grasp the dangers of such a weaponization of malware. The very density of the crowded data visualizations of global scale, whose spread seems to press against our cognitive grasp, may mask the clarity of the targets of the weaponization of malicious attacks compromising computer systems. For if they fail to orient viewers to their content, the dizzying details of the propagation of the malicious virus challenging viewers’ abilities to process any actual interconnections or causal relations in the spread of a worm-like virus like WannaCry or Petya that spread laterally over distributed networks, in vain hopes to grasp their origins or provenance, or to find sign of a smoking gun. Our own abilities of detection threaten to be intentionally obscured in the maps created by cybersecurity systems, which note the sites of compromised computer to indicate the malware’s range and conjure specters and fears of the inevitable rise of greater malware threats, but not to illuminate the dangers of their scope.
2. While we may be able to partly discern the rapid spread of the infection between geographically removed cities, the powerful maps showing the incredibly broad geographic leaps of malware attacks suggest networks that seem removed from any clear agency. Set against a blank static global map that only raise questions about their inter-connection, but notes national borders, the images of dots of flare-ups or eruptions of encrypted data leave absent the pathways on which they travel, looking for clues in its virulent spread as a symptom or a result of the interlinked landscape. The danger is that they over-write our own abilities of judgement.
Malware has never spread on such a scale or with such success, but the destabilizing effects of the virally spreading worms that reached computers using Microsoft Windows that were not updated since 2012 demand to be considered on another sort of map. The images of dots of disappearing data, often made by cybersecurity teams, terrorize us by showing the increasingly interconnected nature of hubs, the spread of sporadic eruptions of viral attacks on what we have the illusion of imagining mastery and security of the virtual data we think secured in our laptops or systems databanks, and which stabilize so much of our infrastructure. The self-replicating payload inserted in WannaCry hit a huge global terrain mushrooming laterally almost instantaneously, and not only from information hubs, infecting systems and disrupting data that provoke computer shut-downs crowding a global map at a truly unprecedented scale: if this seems a symptom of globalization, it makes detection of the sources of such viral spread impossibly difficult to map, and the promise of ever doing so seem increasingly remote.

Kapersky Lab maps suspected email attacks by tracking cybersecurity and monitoring threats from data encryption to identify theft in real time, synthesizing such threats in updated “vulnerability detection flows” that offer animated object-lessons of global insecurity for the digital age, based on malicious URL’s, phishing schemes, malware hashes, botnets, and hashes of malicious scripts, all of which are usually understood as describing the new terrain of the brave new world cybersecurity in comprehensive fashion, color-coded in terms of the levels of risks of each cyberthreat.


(c) Kapersky Labs
Norse Security tracks the range of attack origins targets, and live attacks in the model of an ongoing digital game of global scale, with rockets fired and targeted strikes hitting with varied degrees of impact in ways slightly easier to process, but such racing live attacks suggest a constant onslaught of pings that Norse showcases to magnify the ongoing onslaught of global attacks and attack targets as a new status quo–and suggest the potentially powerful asymmetric attacks on the cutting edge of cyberwarfare.


The sudden punctuation of the screen track rapidly proliferating cyber threats in real time in mesmerizing fashion on Norsecorp’s dynamic website, as arrays of instantaneous arcs shoot across the globe, creating pings of varied intensity that hit cities noted by colorized rings which ripple out to simulate a range of attacks and counter-attacks that might well be new frontier of constant warfare: the world is appropriately colored black to suggest the apocalyptic undertones of this new, under the radar front.

The growing scale of global traffic of digital attacks from phishing schemes and malware won’t stop, and has emerged as a new frontier in cybercrime that is not only run by hackers, but stands to be increasingly weaponized. It is not by coincidence, perhaps, that the Norsecorp’s dynamic website suggests changes between countries and sites of impact in something like a simulated war. The constantly increasing appearance of malware threats accessed by computers are now charted round the clock by Kaspersky Lab, which boasts an ability to detect 315,000 unique malware daily threats on computer systems. The explosion of possible variants of malware has increased problems of protecting against the online infections that threaten to disrupt data sharing and data security, according to F-Secure’s State of Cyber Security 2017 report–increasing the risks of infections long before the leak of NSA secrets on Windows’ systems vulnerabilities.

In ways that replicate the difficulties to contain the spread of ransomeware, the visualizations stun viewers by showing the quick succession of sporadic eruptions on a global scale. The broad intensity of attacks on computer networks began to be tracked from the Wannacry ransomware erupting in the UK and Europe, to the infection of thousands of systems of multinational corporations in the new strain of ransomware of the Petya attack that inflicted broad damage using the same software believed to have been developed by the NSA, by exploiting a MS Windows vulnerability, identified as MS17-010. The broad reach of the operating systems vulnerability giving it a broader reach by compromising vulnerabilities of organizations, including Russian cybercriminals formed plans to adopt the Shadow Brokers leak to frame their own malicious attacks, although without as yet clearly defined motives.
But the geographic location of such planned attacks get lost in their proliferation over a globally distributed network, traveling in packets spreading malicious software by social media, mass emails, website or, increasingly, by being concealed in apparently trusted updates to infect machines whose hard drives and data is suddenly able to be controlled remotely. At the same time as the globe grows increasingly crowded with compromised systems and data, denoted by the crowded dots of most visualizations of the virulent spread of infections among affected networks, lack a clear frame of reference and is stripped of agency–perhaps due to the very cybersecurity specialists who made the visualization. In fact, the maps offered by internet security systems offer evidence of the ever more dangerous nature of an interconnected nature of systems.
The maps tgenerated by cybersecurity experts seek to materialize and magnify the potential dangers that we already fear such attacks might bring: the rapid lateral movement by syntax designed to encrypt data among systems is not clearly apparent, although we might trace its progress by connecting the dots in time-stop images. But the images foreground the break-neck speed of the virus-like spread of encryption by worms doesn’t even suggest the ability to trace its pathways or stop or contain its spread by the worms that contain and run the virus, which seem to travel along systems pathways free from a guiding plan and without any destination, but creating generalized disruptions on a global scale that can potentially compromise infrastructures in unexpected ways, suggesting the possibility of an unstoppable progress of a global paralysis.
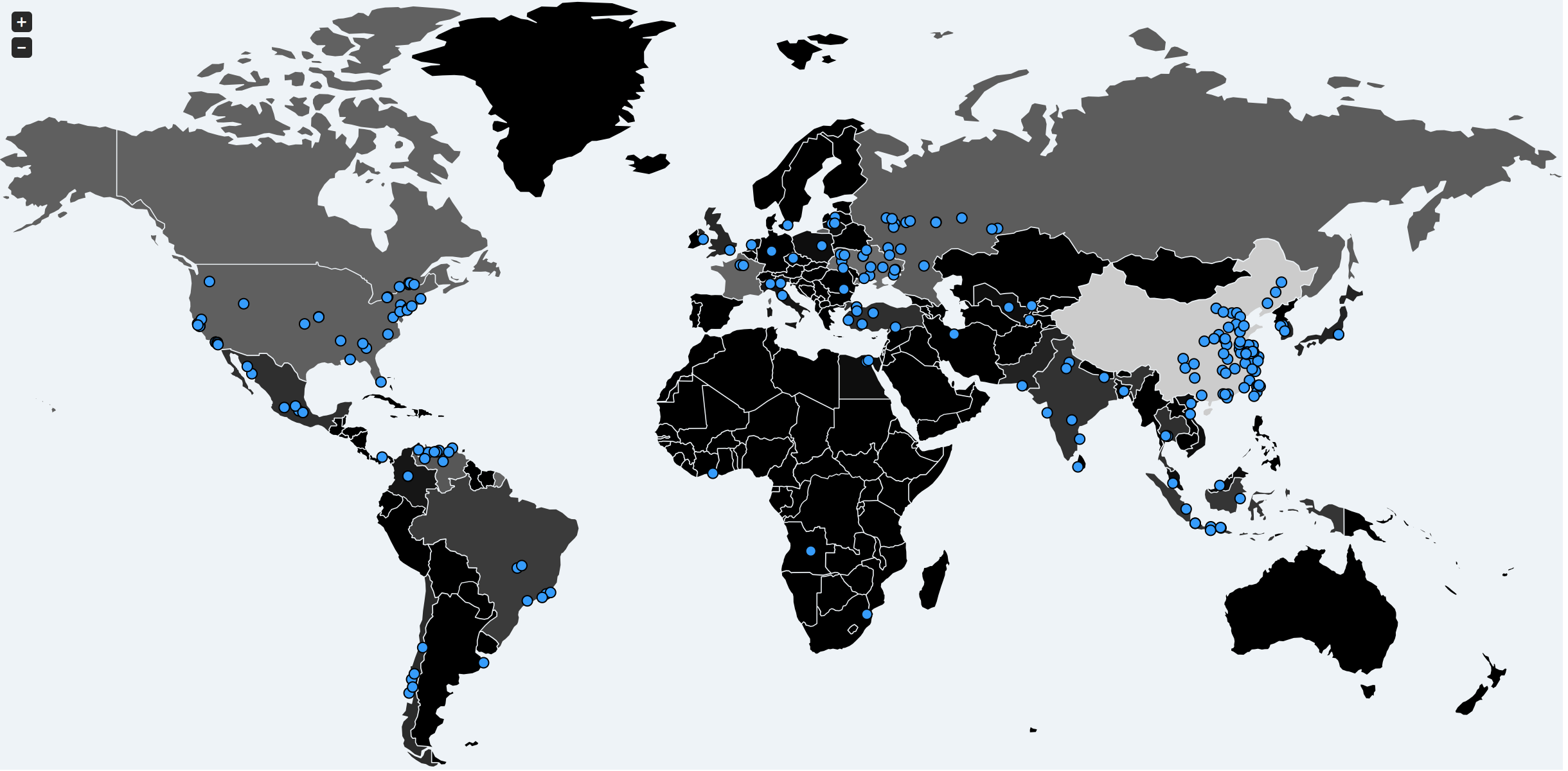
MalwareTech–Infection Spread of WannaCry 0 hours 0 minutes 15 seconds
Malware WannaCry Ransomeware/ MalwareTech
MalwareTech Spread of Wanna Cry at 0 hr 30 min 0 sec

MalwareTech Spread of Wanna Cry after 24 hours
The attractiveness of such visualizations of the corruption of computer systems and encryption of files suggest the limits of the visualizations of its spread and difficulty of maps that might tell stories of the increasing threat of global destabilization by viruses. In a sense, the spread of malware may be perhaps particularly challenging to track for American viewers, ready to see, interpret and accept its spread as evidence of the speed of a digital divide, rather than a targeted attack. The scope of the outbreak makes such a tracking down of its communication and site of origin far to complex.
For once they are liable to see the threat of hacking by malware like Ransomware, they are less likely to read its place in a geopolitical map. Once habituated to view the interconnections of a globalized world, the rapid spread of compromised systems seem so removed from individual agency. The power of the map describing the rapid global spread of malware effectively over-writes our judgement of the way hacking is often coordinated by malicious actors, removing us from the geopolitical map such viruses threaten to be weaponized–against which may most make sense, as well as through infrastructures that malware is designed to corrupt. The breadth of the worm may be something of a useful feign or disguise.
The map to be sure reflects the distribution of IP addresses, in part, as its transmission by Windows vulnerabilities may suggest. But the naturalization of the rapid spread of contagion by interlinked systems of internet traffic only offers a basis to see the points on which the malware travels, rather than the scope of its intent: the intensity of online use in many regions of the most densely populated regions of the United States has brought something of an addiction to speed, and the rapidity of ties among inter-linked networks that many of the recent world-wide spread of cyber threats and network infections seems to magnify threats of vulnerability in an online age.
The vulnerabilities of the United States to cyber infection were disproportionate , although cyber hackers focussed on networks, rather than individual users.

The synthesis of visualizations of vulnerabilities were pioneered in the Kaspersky Cyberthreat real-time map, which offer almost a spectator sport of online infections, with millions and millions of computer hosts being infected in minutes at breakneck speed, in ways that the pathways seem randomly seeded, reaching and infected all internet addresses without discrimination or a targeting of geographic locations.
We increasingly rely on data visualizations and infographics to process global change and web-based traffic after all, as if in hopes to establish its global scope and purview as it travels irrespectively of space. If Christopher Nolan suggests the three levels at which time moved in World War II in Dunkirk–on the ground, at sea, and in the air–these maps suggest the tyranny of the break-neck speed of the world wide web, and the terrifying ease of data encryption’s multiplication across space. The next war is perhaps to be fought in blinding speed, so compressed to challenge human response. But the incommensurability of our data feeds may blind us to the pointed geopolitical force destined to motivate cyber attacks. If the motivations may be concealed in a distributed network, exploiting vulnerabilities in software programs to launch ransomware or wiperware attacks with effects only able to be visualized in global terms–at the risk of obscuring the spatial situation or motivation of such hacking attacks. It has been suspected by security researchers that destabilization may be at the root of ransomeware threats–which rarely make that much money, even if governments have so far argued them to be enabled by the lack of links of Bitcoin exchange accounts to locatable addresses; the digital fingerprints of North Korean hackers appeared in the WannaCry code–although the fingerprints may have been included to attach throw governments and blame the malware on state actors. The new aliases of such cyberattacks make them difficult to trace, as the signs of compromised accounts provides little trace of its origin.
Yet hacking tools stand to emerge as weaponized, and a dangerous expansion of cybercriminality to state actors seeking to make destabilizing attacks by infecting energy, military, or commercial infrastructures. Yet rather than map the pathways of provenance, the victim geography of how many enteprises or mjltinationals were effected in different countries aren’t surprising, and fail to suggest the motivations to which they respond or the motivations of cybertheft.

3. The extent to which we rely on maps to process such distributed relations may make the process of destabilization all the more difficult to discern and discover in the global compromising of computer systems. For they obscure the delivery mechanism of malware, ransomeware, or other means of taking advantage of system-wide vulnerabilities spread so difficult to trace back to a starting point or individual actor(s). As we seek to track the speed by which the data on hard drives is systematically encrypted, as if to visualize our greatest nightmare scenarios of how many computer systems and networks switched off, the map of systems of affected threatens to become something of a smokescreen the spread of viruses by worm-like viruses that exploit openings on operating systems to compromise files and clean event logs on networked devices, and wipe them clean.
The compromising of systems malware prompts infection maps that provide little basis for retroactively diagnosing their spread, and whose pathology remains stunningly opaque–and offer little illumination of its epidemiological spread. For it erases history, or indeed geopolitics, by suggesting the vulnerability lies in the networks whose weaknesses and vulnerabilities cybercriminals use to infect hard drives that are so broadly distributed–and distract from the mechanics or disruptive intents cybercrime have increasingly gained to disrupt digital systems.
Pathways of communication so obscures the vectors of attack to leave one exasperated at the interlinked networks that allow such a global multiplication of compromising networks by a single command line can pass user credentials system-wide across large multinationals, but whose provenance cannot be easily or ever mapped, and is able to spread globally more quickly than we can actually comprehend in real time.
Christopher Nolan’s film only reminds us of the increasing pace at which we live. Security networks have already warned us of the “the beginning of the end of the world as we know it“ as the speed of malware viruses grew and their discovery multiplied annually at increasing rates, as new forms of malware were discovered at a rate of one every half second by 2013, potentially compromising electricity, water, and banking, turning to state-sponsored hacking systems, including the United States and Israel, to target networks as in the 2013 Red October attack of which China was suspected, or the 2009 launching by the USA of the Stuxnet virus by which Iranian nuclear centrifuges were targeted, opening up the possibility of increasing web-based attacks against which immunity cannot be promised. And the recent relentless scope of cyberattacks on Ukraine, as one that cut electricity to nearly a quarter-million Ukrainians just before Christmas in 2015, cutting electricity to 80.000 lines. The coordinated intrusion into system hosts, corruption of servers and workstations and blinding of dispatchers was masked not only by the surprise of power loss, but masked the goal of compromising gas shipments to the European Union. By targeting a cyberattack far from the military front to the west, the attack seemed unrelated to the theater of war, but of course was not. The ability of hackers to strike infrastructure suggests an under-the-radar spread of war, in which Ukraine’s president has noted over 6,500 cyberattacks in two months, in an attempt to nudge the geopolitical map by sustained destabilization of the country.
The need to better map internet-based forms of stability and destabilization have become increasingly difficult in recent months, as the demand to locate destabilizing techniques has grown, as if lifting a veil on new forms of international relations. If we should be increasingly concerned to map destabilization and instability, the problems of mapping digital disruption through the spread of malware represent among the most dangerously difficult areas to visualize or grasp as their vectors multiply–either as phishing schemes, Word attachments, or compromised software. In recent months, the spread of cyber attacks that seem to target businesses worldwide challenge us to map a sense of agency, hitting organizations from multiple countries simultaneously that trigger our worst fears of globalization, and raising red flags simultaneously world wide, that so quickly cripple computer systems in apparently indiscriminate techniques to disrupt global systems extensively in ways that even cybersecurity is challenged to grasp the TTP’s–tactics, technique, and procedures–especially as they infectiously spread among group with little training in “cyber hygiene” who are more susceptible to malicious ransomware or other malware attacks able to paralyze infrastructure and create massive blackouts.
Despite clear needs to take a hard line against nation states that encourage malware such as the “wiper” virus that has the potential to spread globally, quickly and irreparably crippling computers networks indiscriminately and leaving organizational chaos in its wake, the mapping of the recent outbreaks of disruptive malware and cybercrime from ransomware to wipers face fundamental challenges if they are not able to be adequately mapped. If the images that we use to map their spread are misleading, moreover, the very distributed nature of the networks of disruption serve to conceal their true nature and make them more difficult to assess. For the cyberattack was not only another case of worm-like malware or ransomware, that spread online without any logic across distributed interlinked networks, but was timed to be launched on the anniversary of Ukraine’s adoption of its own constitution, as if to puncture the celebrations of independence in what was not only a global cyberattack that forced many to isolate the spread of the virus on their computer systems, but a targeted destabilization of a nation. A virus seems to have been put up on offer on the Dark Web as “ransomware as a service” in ways that were almost impossible to trace or track down. The problem we will increasingly face is both to map the communication transmission migration of malware that moves so quickly–and track its agency either to hackers or to a state actor.
The resulting visualizations of the extent of such a cyber attack can be a convenient way of covering one’s tracks. The dangerous spread of the aggressive worm-like virus demanded to be mapped, in an initial attempt to process the scope of its damage, although the sort of global map was perhaps the most misleading in attempts to map the intentions of its perpetrators who unleash data-destroying parasites into live systems to compromise their integrity. The spread of such malware viruses delineate an all too familiar template of digital disruption and instability. On May 17, the “WannaCry” virus spread through computers, tauntingly referring to the response it tried to provoke in human users. The ” WannaCry” malicious global cyberattack so rapidly migrated to some 230,000 computers distributed across over 150 countries to remap links between computer systems, data and users in globally compromised systems, in ways fortuitously blocked by discovery of its kill switch from outside the cybersecurity community.

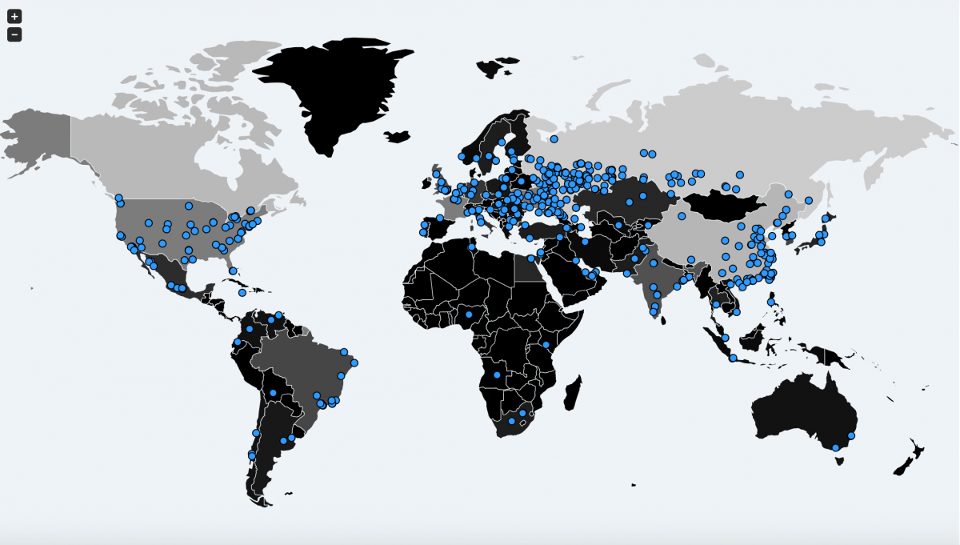
Countries Hit by WannaCry Malware/Woke

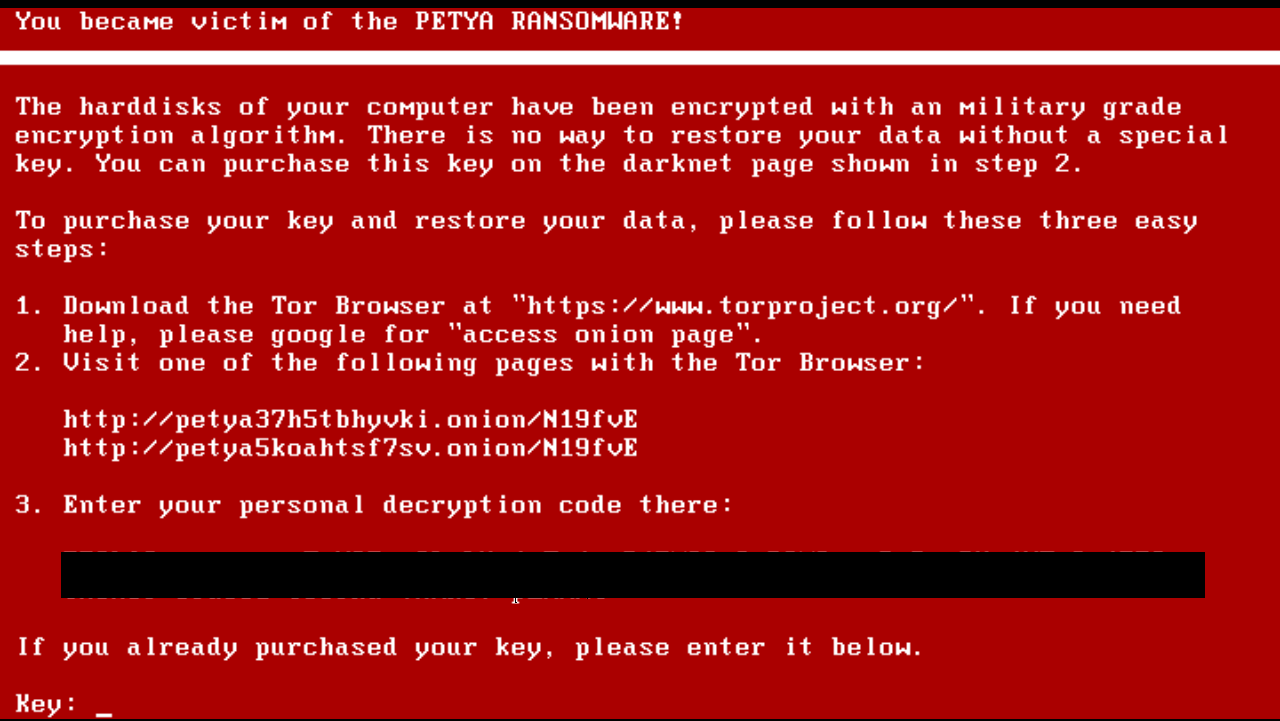
In contrast, the subsequent malware infections of the Petya cyberattack was only apparently a next generations version: and it may be that the deep dependences between Ukrainian and Russian computer technology, while changing, has made Ukraine a testing ground for escalating a military conflict into a global cyberwar. It similarly crippled corporations across 60 countries and led users to freeze before formerly friendly screens, who were suddenly threatened with the disappearance of all their data and given only a threatening message that reminded them of their lack of access to hard drive files guaranteed to drive panic reflexively, as if a diabolical psychological study of collective observation. But the similar specter raised by Petya of another globalized assault on computer network that failed to hit few sites concealed the newly targeted ends of such extortion letters, which were less geared to extracting funds, of which the first infections were concentrated in Ukraine, but spread to 64 nations, including the United States, Germany and Brazil after affecting over 12,500 users’ machines in Ukraine alone as it spread quickly on June 27, 2017. Ukraine quickly accused Russia of the hack.
But did the power of familiar data visualizations of what seemed a similarly global onslaught either obscure or erase the epicenter of what was an actually quite clearly targeted attack? Was the release of WannaCry something like a trial balloon or a test run for new techniques and practices of cyber-attacks? Or did it just suggest the abilities of cybercriminality to figures already practiced in operations of infrastructural disruption? Although Vladimir Putin stonily intoned “Russia has absolutely nothing to do with it,” his denial may have appeared to be confirmed by the reported targeting of many of its networks–and seems, in the odd post-Trump world but an echo of the outright deception of The Donald, whose interrogation of Putin on the subject of tampering with the American elections–“I said, ‘Did you do it?’ And he said, ‘No, I did not. Absolutely not,’” the American President Donald Trump so memorably and incredibly described his exchange with the Russian strongman, gaining the same response after “I then asked him a second time in a totally different way.” (When asked in the 2016 Presidential debates whether our own national institutions were victims of cyberattack, Trump famously incoherently veered far afield with a string of odd associations that started from musings on “the cyber” to vague incriminations of the United States: “As far as the cyber, . . . We should be better than anybody else, and perhaps we’re not. I don’t think anybody knows that it was Russia that broke into the DNC. She’s saying Russia, Russia, Russia—I don’t, maybe it was. I mean, it could be Russia, but it could also be China. It could also be . . .“)
Few would seem so gullible as The Donald about the levels of interference of Russian operatives to destabilize the 2016 elections; indeed, the excitement that this must have created in some government circles for similar tools of destabilizing societies by exploiting digital tools to target government systems. As NSA Director Michael Rogers, who from 2014 directed United States Cyber Command, dryly counselled “now is probably not the best time” to set up the cyber security cell Donald Trump proposed with Russia, allowing himself remarks even if he was “not a policy guy,” as such cooperation was “something that you might want to built over time were we to see changes in [Russia’s] behavior“–much as President Trump’s plan “to move forward in working constructively with Russia” by “forming an impenetrable Cyber Security unit” with the Kremlin raised eyebrows from Preet Bharara to Ashton Carter to John McCain. The rebuff from Rogers may have been well-timed, as Trump’s assertion of such a working group at the G20 was ill-timed.

The difficulty of mapping digital disruptions after the fact is surely helped by the state of disbelief and search for stability that occurs after the disruption, and the difficulty in moving to a clear attribution of agency in a distributed system. Yet the suggestion of Russian losses as a result of the worm-like virus seemed but an excuse to conceal the far greater damage done in China, where some 30,000 systems were compromised–even if Russia claimed to be hardest hit. In the following hour, and before the week was out, it became clear that mapping damage in national terms was a red herring, since the attack exploited Windows platforms rooted in software rather than geography, and was limited by the discovery of a kill switch: while it bears note that vital Russian servers were largely using domestic Russian software that was developed in the last years of the Soviet Union remained unaffected, this would provide a perfect cover for the disruption of non-Russian software platforms.
4. That the spread of the malware deployed tools that could be traced to the United States government served to muddy the question of national responsibility. The theft of Shadow Brokers led to a warning from cyber-security experts based in the UK that the future danger of “copy-cat authors” altering the virus code in new ways. But this danger was partly buried in the collective sigh of relief that the global impact of damage on what seemed an interconnected network had been averted as a twenty-two year old ended up registering a domain name that halted its global spread.

Spreading across the world after the resurfacing of WannaCry ransomeware resurfaced both in a Honda factory in Japan and traffic cameras in Australia. the similar distribution of Petya 2017 seems to have intentionally concealed the concentration of targets located within Ukraine’s infrastructure, from the Kiev metro to the major state power distributor, Ukrenegro. As the worm hit such international entities as Maersk, WPP, and even the Russian oil giant Rosnoft, and radiation-monitoring system of the Chernobyl reactor, which had to revert to manual checks, the predominant concentration on the targets in Ukraine was somewhat masked, as was, in initial moments when it most mattered, the potential origins of the broadly disruptive malware worm that was so disruptive. (Indeed, the most ransomware individual attacks occurred in Russia, if Ukraine was a very distant second, though the data tabulated by Kapersky Lab seems self-reported.) The result is to muddy the waters a bit about which critical infrastructures of nations were hit in what was the latest large malware attack to have occurred through an update originateng from the Me.Doc software, manufactured in Ukraine. The focus on immediate disruptions among the data held by civil institutions like from banks, commercial services, train stations, and other mission-critical organizations obscured the local costs it inflicted on the software provider itself.
The scale of disruption and the dangers of the virus have been more difficult to qualitatively describe or measure over the long term at this point. The degree to which infrastructure was affected in Ukraine is moreover skewed by the most common maps, based on the reporting of infections to McAfee, whose wide use in the US led it to be privileged as a target, but minimize the extent of infrastructure damage in Ukraine of Petya’s worm capabilities. The inability to restore data by decryption conceals the greater damage created by the irreversible damage that was created by wholesale wiping of data from hard drives in multiple sectors in Ukraine, designed to provoke instability, as the anonymity of attackers rapidly increased frustration and panic at data loss, and creating sudden power grid shut downs: the erosion of defensive and security capacities under Victor Yanukovich in previous years was immediately exploited by the fake ransomware, whose launch suggests that Ukraine–site of continued cross-border aggressions–in fact might be a sort of laboratory for weaponizing malware.
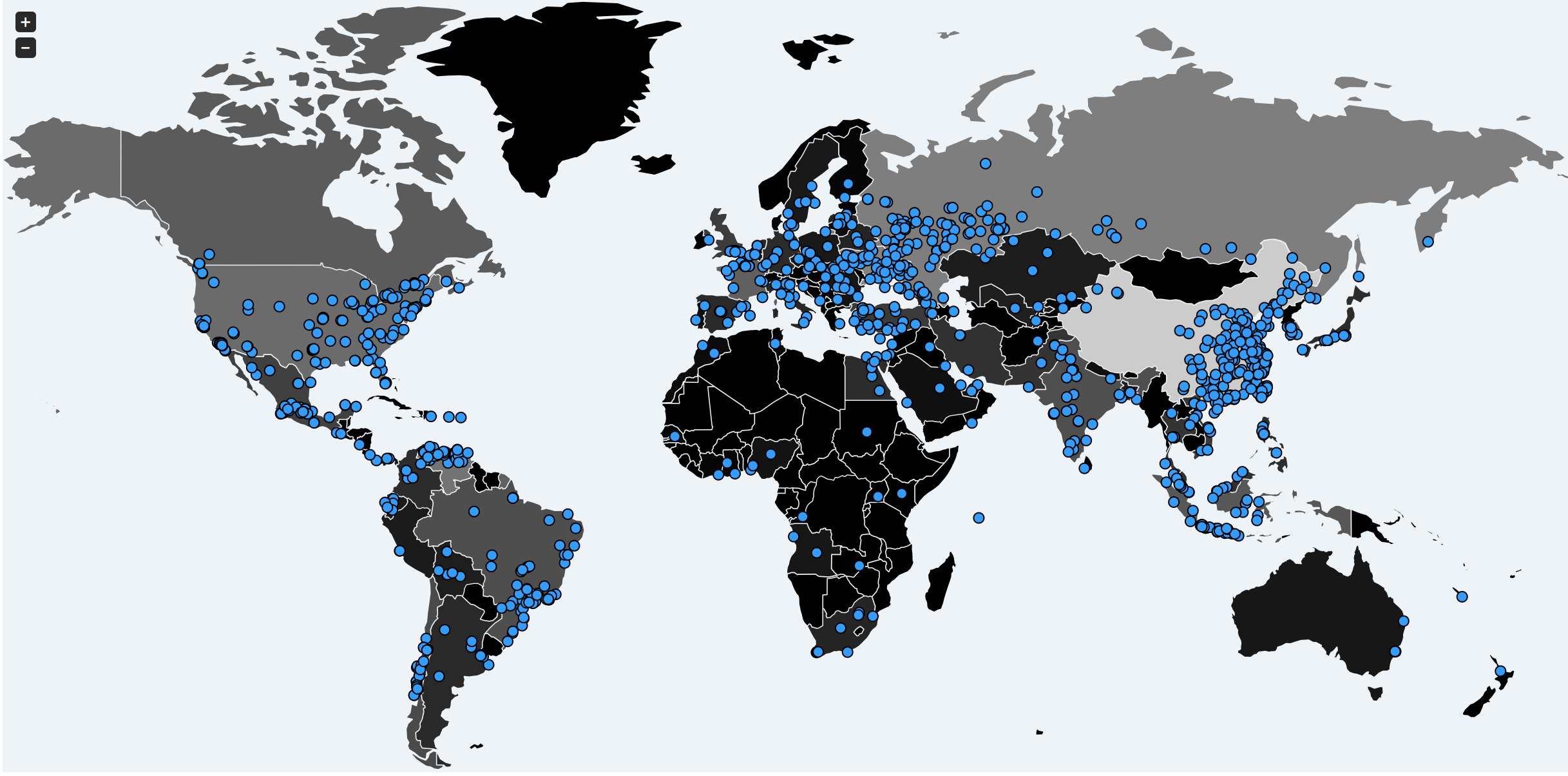
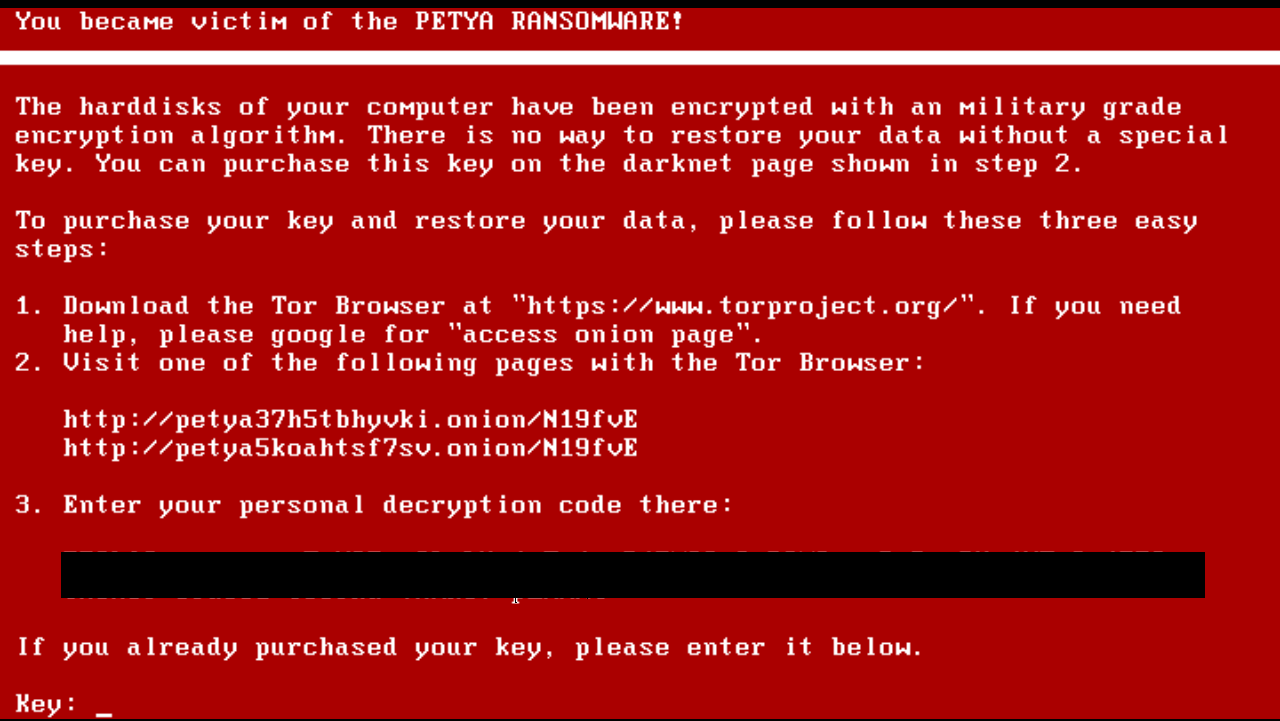
Much as Russian military forces that entered Ukraine in 2014 effaced all signs of their identity or the nationality of their weapons–in a blatant breach of international law–when entering the Crimea, and Putin refused to acknowledge the 11,000 troops without military insignia as national agents and deceptively cast them as a spontaneous “self-defense” militia, malicious cyberwarfare removes any fingerprints from the disruption and suffering it inflicts–as the attempted hacking of the Ukrainian election in 2014. The importance of reading the history in the distribution of the malicious encryption of files beneath the data visualization seems a necessary contextual framing of the “military-grade encryption system” that users were panicked to find had so suddenly locked their computer screens that didn’t allow their hard drives to log onto Windows.
McAfee–Countries hit by Petya 2017 virus
And when the dust settled, as it were, the bulk of the attacks that occurred from Petya 2017 were localized far more prominently in Ukraine–where almost 70% of the attacks on individual computers were located, in ways that put into perspective the diffusion of the worm-like virus across the world that was attempted–although this only later raised suspicions as to whether the potentially global disruption masked a targeted attack.

5. Viewed in more detail, the targeted focus on Ukrainian infrastructure, and Ukrainian companies’ clients and software becomes even more evident, beyond the over 2,000 affected companies that Ukraine Cyber police has confirmed had their files encrypted. By taking advantage of concealing such a destructive payload by disguising ransomeware within a legitimate update, by an email vector, the unknown perpetrators used the Me.Doc update as a proxy to reach connections that would undermine the credibility of the firm, as well as Ukrainian corporations and to multinationals doing business in Ukraine, providing a new basis to isolate the nation by a manipulated server update, unleashing something that seemed ransomeware without even ever intending to restore the data that they encrypted from hard drives in a particularly destructive manner: as a tool of undermining trust in an Age of Trump, the worm-like cyber attack provided an under-the-radar way of isolating Ukraine further. Such attacks echoed the BlackEnergy malware cyber attacks of 2015, and the Petya 2016 ransomeware; but this time targeted Me.Doc software that the Ukrainian firm Intellect Service devised to interact with Ukrainian tax systems as if to isolate Ukraine internationally on the geopolitical map. Without such context, the “mapping” of the virus is incomplete.
Although the encrypting of files provoked an immediate international response by June 29–and threatened to spread globally, as its malware infected corporations and organizations without known ties or connections to Ukraine–a response to staunch damage that lead to the discovery an unknown actor had stolen the credentials of an administrator at M.E.Doc to insert a backdoor into the Me.Doc server to conceal the targeted strike and begin a broad panic which had the effect of only further sowing confusion and masking their agency.

As the cases of the vicious malware infection encrypted data from Lithuania to France, Greece, Spain, and Israel, shutting down shipping channels and sowing international chaos perhaps even more than the still unidentified hackers had intended, the British Defense Secretary alerted the world that similar future cyber attacks could result in military retaliation by missile strikes or force, raising questions of the conversion of ransomware to cyber warfare. The predominance of Ukraine among compromised computers suggest the specially strategic sense of prying the region apart from central Europe–and indeed isolating it from the compromising of software from Me.Doc which had increasingly tied it to Germany, and so disruptive to individual users who had used their accounting services. But the global nature of the virus concealed the deep compromises of Ukraine’s infrastructural networks, form traffic and postal to banking systems to government networks to shopping, in a colossal strike deemed “the largest in the history of Ukraine” that upped the ante on how Ukraine became a testing ground for a playbook of destabilization.
The disruptive disturbances suggest a war waged on screens, as much as on a battlefield, which exploited not only network dependencies, but disrupted the broad dependence on screens as sources of information. The sudden generation of faceless extortion notes demanding immediate payments of $300 in BitCoin that appeared across terminals were only slowly identified as a lure and a ruse. The disguise as Ransomeware concealed the intentionally disruptive effects and their focus on Ukraine and Ukrainian networks, most specifically the M.E. Doc tax accounting software, which effectively targeted financial institutions in the Ukraine and critical infrastructure imitating previous cyber attacks that included previous hacks of Ukraine’s electric grid which provoked the occurrence of widespread power outages across Ukraine, which appear tied to hacking groups affiliated with Russia, increasingly active in the region having seized Ukrainian territory in the Crimea and backed separatist movements largely based in Western Ukraine. The fact that the Petya attack also affected private-sector organizations in the U.S. and its allies including hospitals, transportation firms and other critical infrastructure could be seen as a basis for increased vigilance both to define the norms of aggression in cyberspace but remap the role of cyber-attacks in disrupting Ukraine’s global ties, as well as maintaining its civil space.
The sudden erasure of data that seemed to be taken hostage temporarily upended the links that once provided easy access to information seemed evidence of the webs that globalization had created, as if perpetuated by the speed of delivery the internet promised and a scope that cannot be grasped but as a set of system-wide failures, disrupting far-flung systems in ways that seemed impossible to map or visualize. Users might accept the attack as a new normal, precisely because of the dehumanized address that seemed to multiply mockingly across screens and monitors, offering instructions to recover your lost data in almost smirking tones. Petya 2017 alerted its victims of inability to access any of their encrypted data with all the monotone solemnity combining the tones of a gangster and Russian border guard: “If you see this text, then your files are no longer accessible . . . . Perhaps you are busy looking for a way to recover your files, but don’t waste your time. Nobody can recover your files without our decryption device.” But no clear ways of recuperating data existed, as the goal was to compromise infrastructure, rather than extort.
In ways that contrast with the “normal” speech of the step-by-step instructions that users were given to respond to the sudden disappearance of access to files that coyly mimicked Microsoft or Apple’s own language that seem to strip users of agency by addressing them in calming tones as if they were children–“Oops! Your files have been encrypted” led to bolded headers including “Can I recover my files?” and “How can I pay?“–the unfamiliar screens suddenly provided instructions to email necessary funds to a personalized Bitcoin account in order to recover their extracted data within but a week, in an interface of especially alienating tone. The barely concealed disdain of Petya almost harangued the user with particular urgency: “If you see this text, then your files are no longer accessible, because they have been encrypted,” red the red-lettered message visible on screens. “Perhaps you are busy looking for a way to recover your files, but don’t waste your time. Nobody can recover your files without our decryption device.” And they largely didn’t recover the lost data encrypted in a military-grade encryption algorithm whose sophistication revealed the offensive ends of its release, even as the wide distribution of the virus globally concealed its targeted nature. The goal was to disrupt, or to undermine the services that software providers provided.
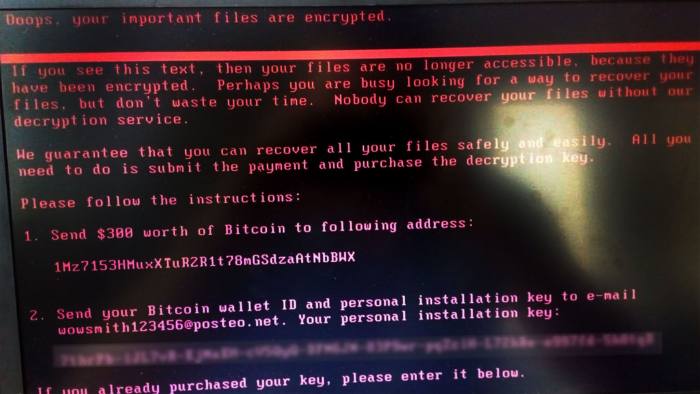

WannaCry’s Demand to forward $300 of bitcoin currency via email
The generic nature of the instructions that replaced one’s familiar screen saver seemed particularly dehumanized, and were paired with an eery timer that allowed one three days to pay the demanded ransom. The hacking tool believed to have been created by the United States’ government’s National Security Agency (NSA) became weaponized for unclear ends. Repurposed in ways its devisers never dreamed, the ransom notes of unidentified extortionists spread rapidly to infect tens of thousands of computers in nearly 100 countries, in so doing temporarily destabilizing world systems for ends never intended by its creators, and that were not even clear, illustrating a sense of distributed agency that was difficult to grasp if easy to trace to an old Windows 7 or 8 bug, insufficiently patched by many, but providing a back door to their data in a modern plague, as remote extortionists used spam email attachments to demand sudden payments to restore access to data on one’s own hard-drive, disrupting the National Health System in England by courting inexperienced victims, and apparently targeting computers in Russia, Taiwan and Ukraine especially.
The heightened levels of panic that ensued from the extortionists’ demands may have saved to distract attention from the particular targeting of Ukraine in the variant of “WannaCry” that spread not via a bug in older versions of Microsoft Windows operating systems, but with a far more unclear rationale: the files were not restored, after payment, this time, and the email address was itself rather quickly killed. As it was realized that Petya was, unlike WannaCry, not Ransomeware but out-and-out Malware disguised as Ransomeware, the worm-like abilities by which it navigated world-wide networks made it far more nefarious but exploited similar Microsoft vulnerabilities. The notion of ransomware creating failures that started from the appearance of tantalizing anonymous warnings in the systems of global companies as AP Moeller-Maersk in shipping, the pharmaceutical group Merck, the St. Gobain construction group, the global law firm DPA Piper and Rosneft, apparently across national bounds. The apparently placeless nature of the operation that simultaneously erupts worldwide makes its logic and spread particularly difficult to grasp in terms of agency, or even of targeting–while probably created by a state actor, it targeted systems with near-ubiquity, including power grids, petroleum corporations, airports, global shipping giants, and even nuclear power plants like Russia’s Chernobyl reactor reported malware infections that froze operations.
Rather than being a symptom of globalization whose very propagation seems to conceal its own hidden logic, wasn’t attributed to any state or non-state actor, even as paying ransoms to restore service was discouraged by governments and cyber security monitoring systems. The challenges of mapping the break-neck speed of infections and compromise were startling, and test both the abilities of data visualizations to plot sites of compromised systems. They can create something of a ‘data visualization fake out’ for its perpetrators by distributing agency globally, as one marveled at the scale of infection that began from Eurasia, where it gained the greatest density of systems disruption. but spread globally over the afternoon as it was propagated world wide with a terrifying simultaneity, rapidly infecting networks world-wide:
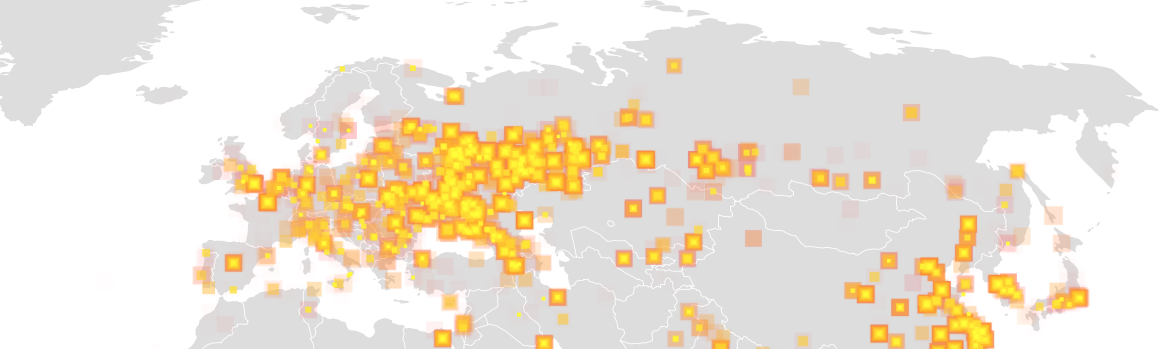
Malware Explosion, 12:52/New York Times
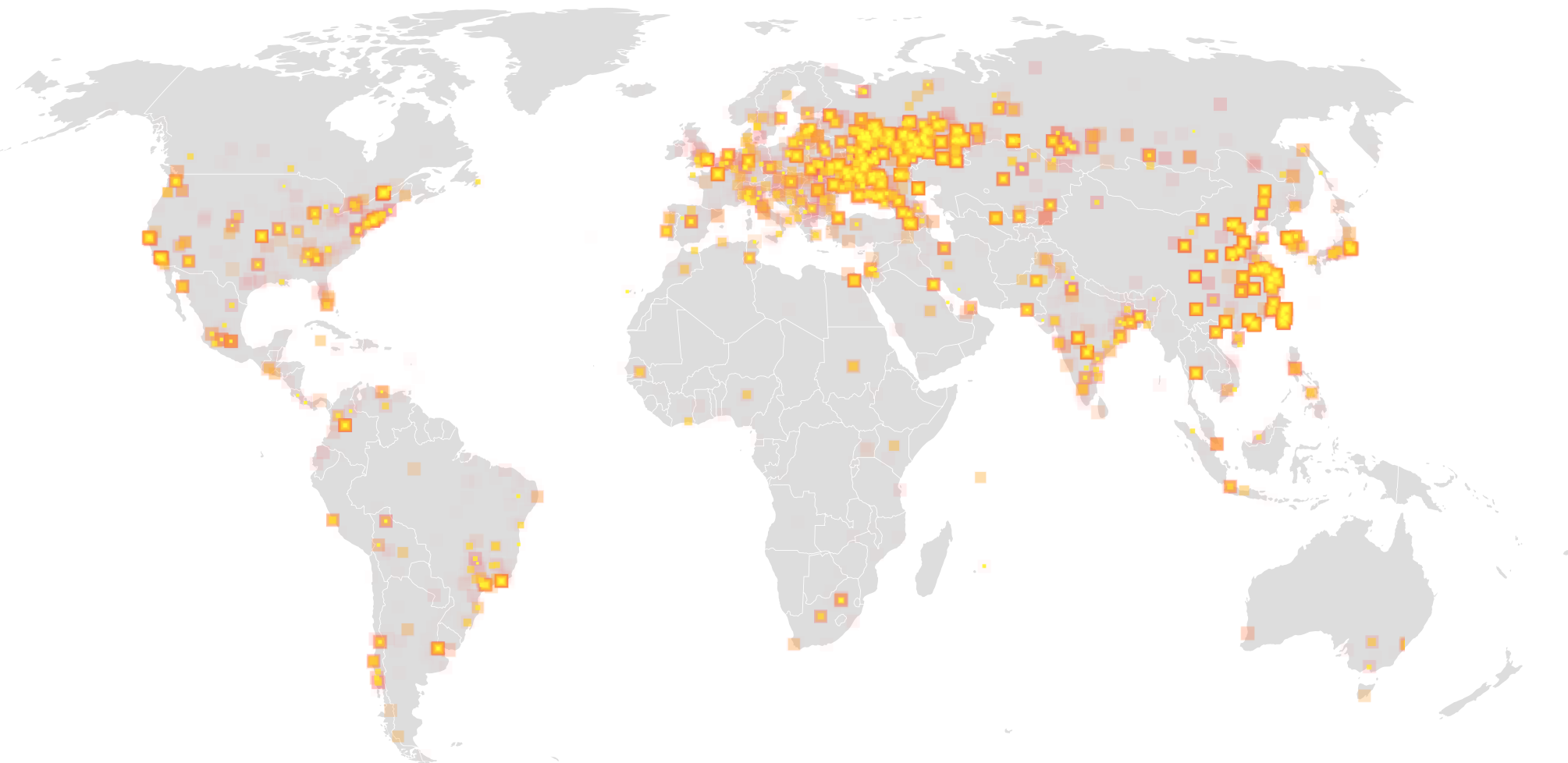
Malware Explosion Spreads Globally, 1:21/New York Times
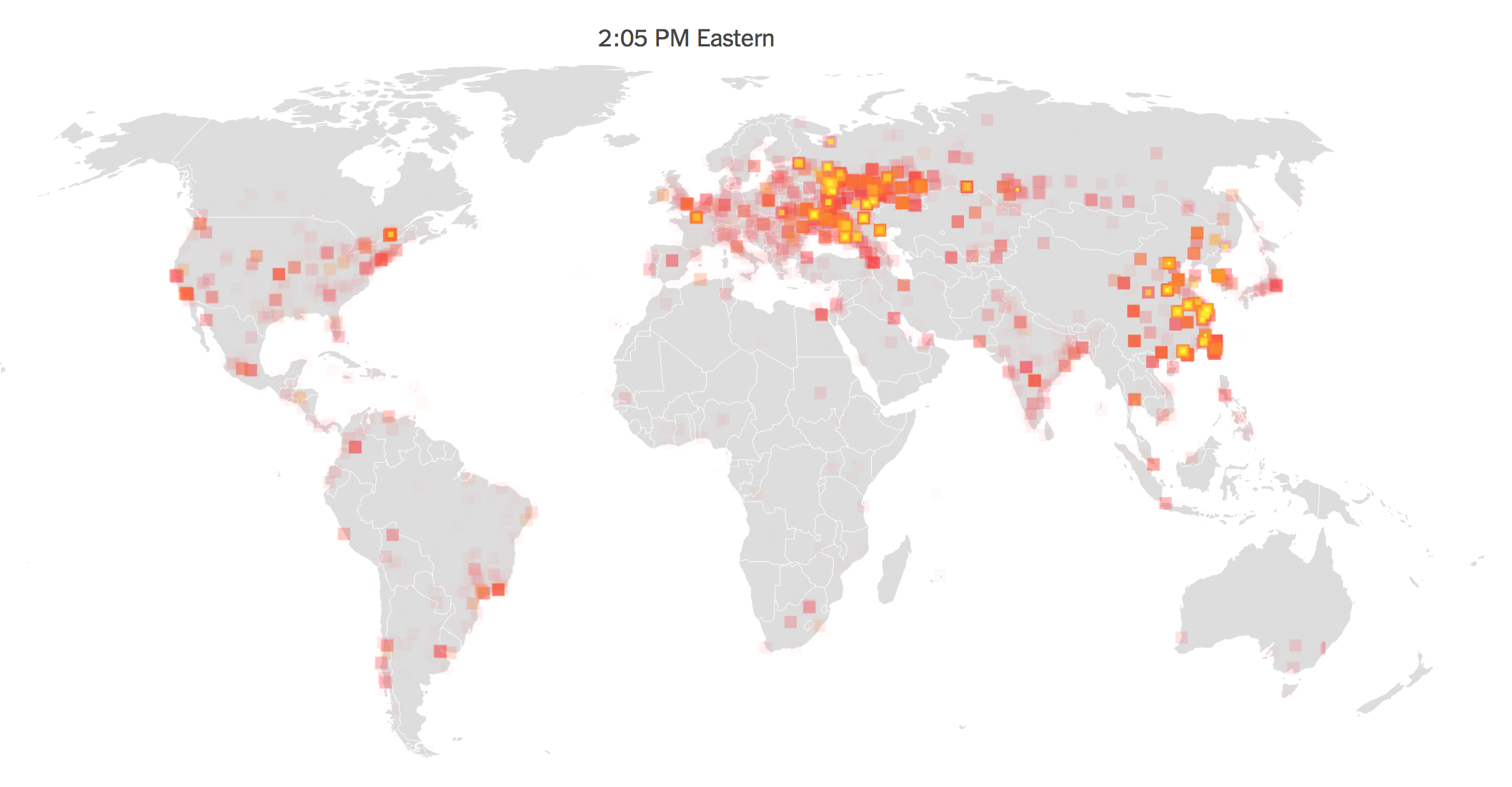
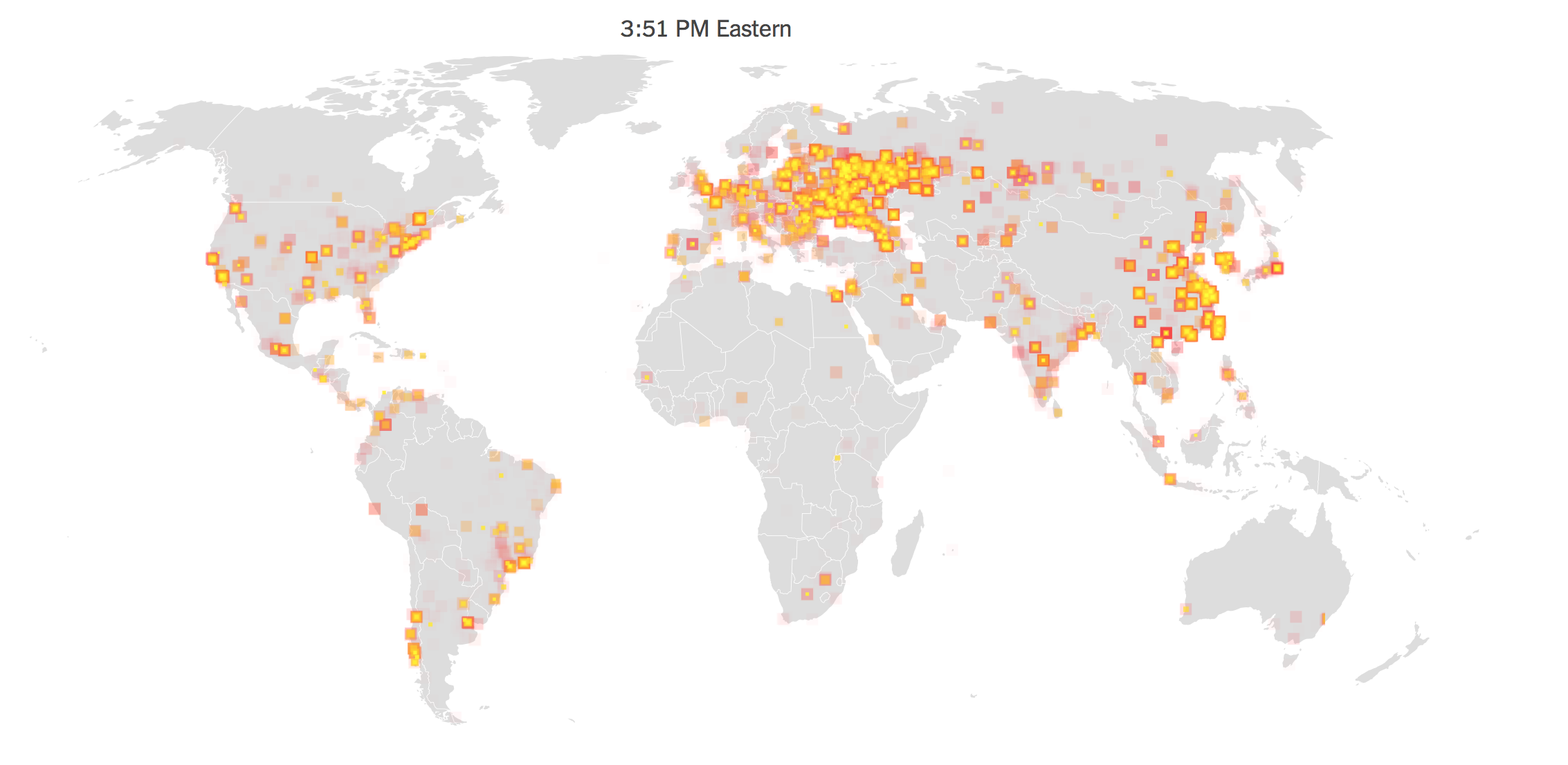
New York Times
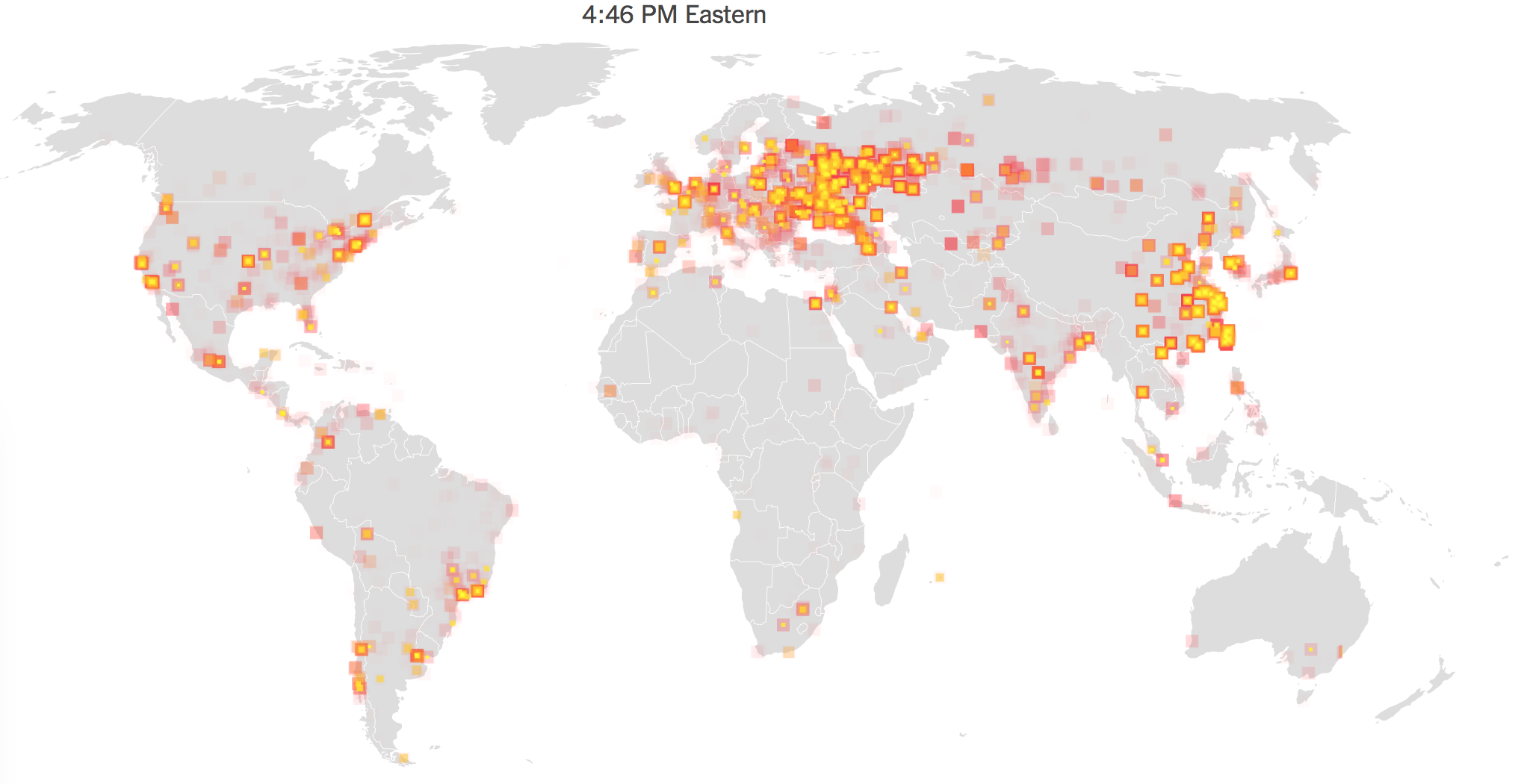
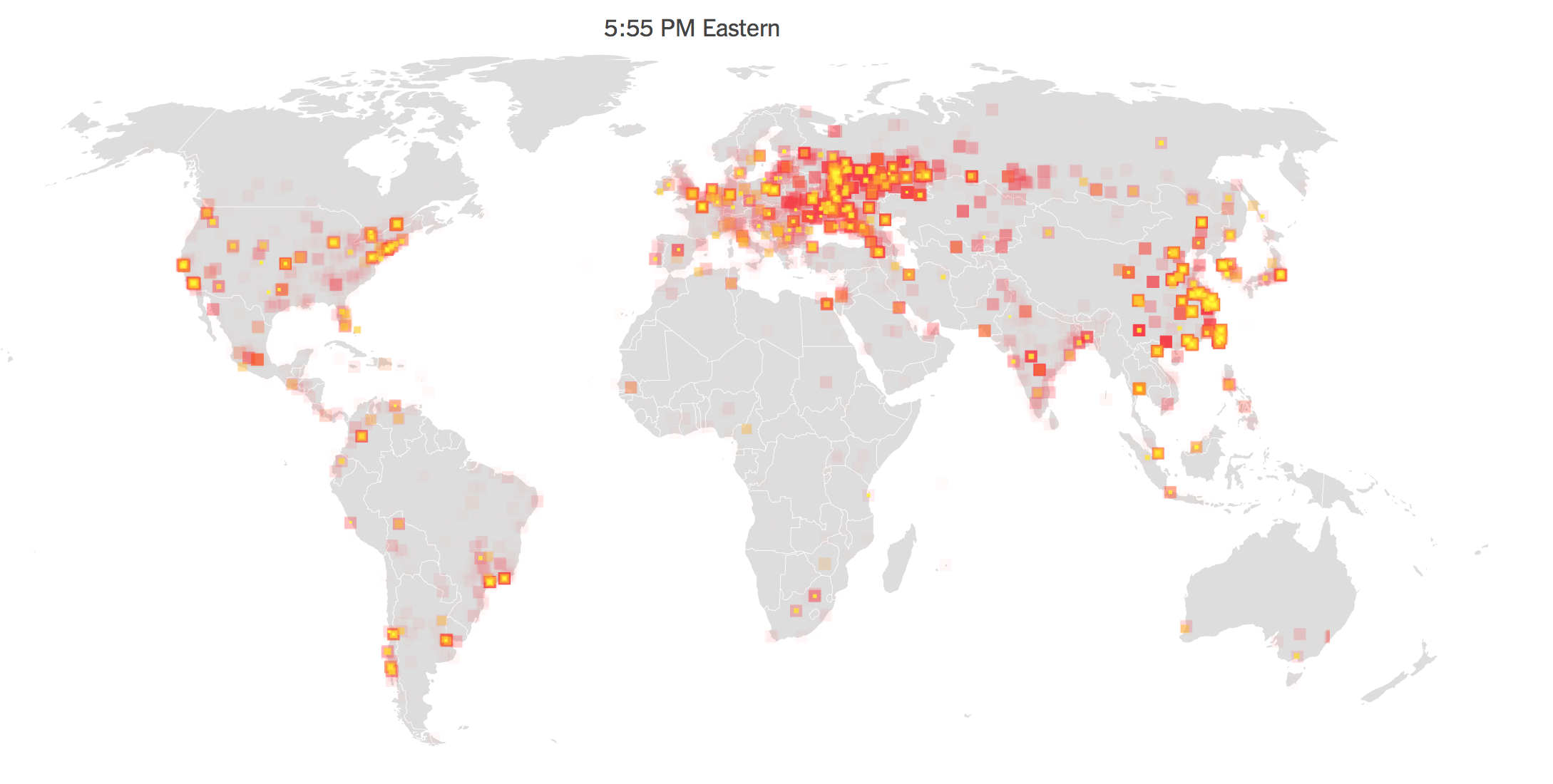
The evidence of the global impact of the infections transmitted along computer networks so dazzlingly illustrated globalization to mask the actual targeting through MeDoc of Ukraine’s economy, with some 75% of targets this time being Ukrainian and most using Ukrainian systems, suggesting a calculated destabilization of Ukrainian software firms. While not easily seen as a violation of state sovereignty, the encrypted virus that this time travelled internationally hidden within a legitimate software update did not reflect an indiscriminate attack of anarchist origins, and the pretext of ransom only a pretext for the disruptive economic effects that the virus had.
Even the instruments of disruption seem the symptoms of globalization that circulated online: using software that probably originated in the online dump of stolen NSA spy tools exploiting Windows platform vulnerabilities reposted by the Shadow Brokers–a Russian-sponsored group that provided tools of potential destabilization in computer environments, before being used by a third party. Following the release of hacking tools used in anti-terrorism methods by the NSA to track money laundering, stolen either from the NSA or a 5EYES ally that constituted a toolkit for attacking cyber vulnerabilities, the demand for ransom that appeared to have infiltrated hard drives and over-written the master boot records of machines in ways that reflexively provoked immediate fears, seems to have been tied far less to the financial ends of gaining ransom monies than the discrediting of the credibility of the software of a firm or nation that provided the basis for the new strain of malicious code that suggests a next generation of ransomware’s rapid viral spread.

The malicious exploitation of online vulnerabilities created a confusion between place and by targeting business environments using Windows platforms was mapped as the the WannaCry ransomware virus quickly spread around the world infecting hundreds of thousands of computers and locking their owners out of files. infecting hundreds of thousands of computers and locking their owners out of files. ransomware virus that spread in dizzying fashion across the world, infecting hundreds of thousands of computers with the result of suddenly locking their owners out of files, holding information hostage on Windows platforms that had not been fully updated. The WannaCry ransomware virus quickly spread around the world infecting hundreds of thousands of computers and locking their owners out of files.
The odd combination of targeting both government systems and private industry led to multiple releases of different degrees of being compromised, raising alarms about “attacks aimed at Russian lending institutions” and “unknown viruses” that exploited the nationally rooted nature of Cyber Security institutions, and revealed little or any strategy for international cooperation, as computer systems linked in a global network tried to isolate their IT systems and data from theft, disapbling wifi networks and intranet networks to take staunch local losses. The arrival of the latest ransomware that lies hidden within a legitimate software update from Me.Doc, evading firewalls and compromising the accounting tools of the Ukrainian company, as well as a preponderance of Ukrainian organizations and Ukrainian subsidiaries of international firms, constituted something of a fake-out for maps that revealed the firms targeted, shifting attention from the infiltration of the Ukrainian accounting tools by the global scope of parties affected, and faking out the news media who mapped the malware explosion on a global scale. Despite the potential worm-like spreading abilities of Petya 2017, the majority of the attacks on Windows 7 machines were located in Ukraine, and suggested not only disruption of infrastructure, but a deep undermining of confidence in the operating systems tied to Ukraine–in potentially enduring ways that extended far beyond the temporary inconveniences in infrastructure. Indeed, if clients of Ukrainian software companies like MeDoc can be nudged or moved away from their providers, the hopes of compromising the Ukrainian economy promises benefits that extend far beyond the instabilities that the disruptions of business would create.