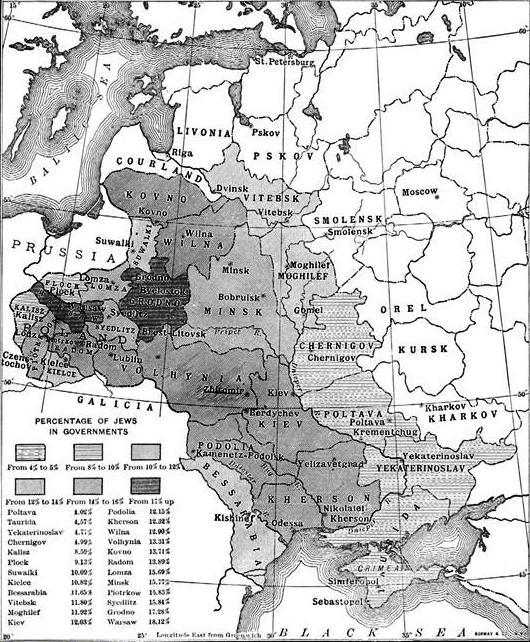
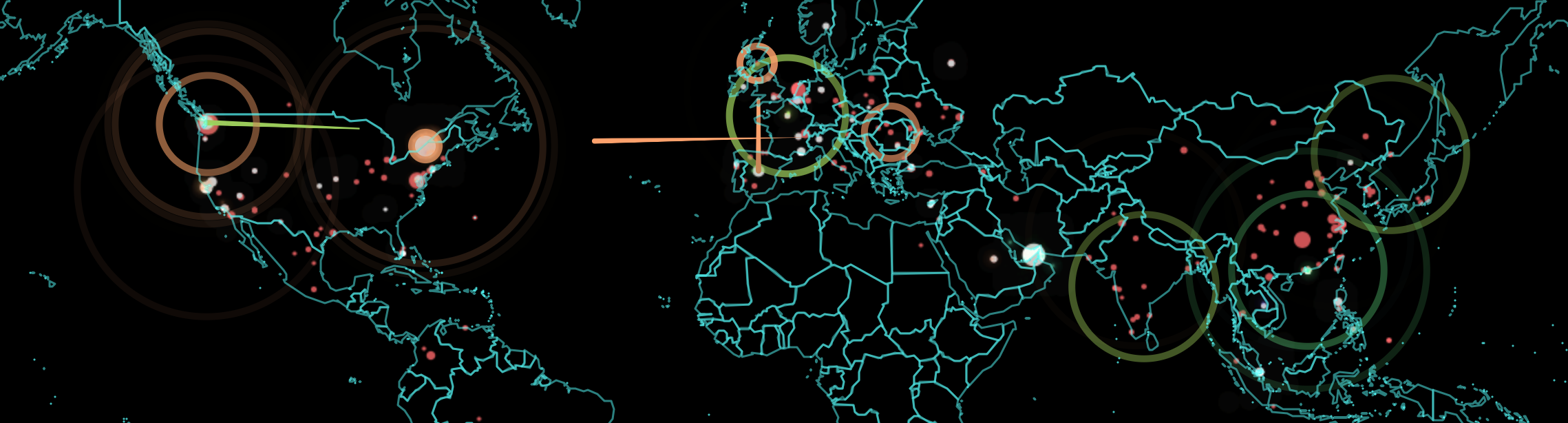
The rush to make a graphic point by mistakenly overlaying concentric circles atop a Web Mercator projection helps to render increasing fears of the range of North Korea’s powerful ballistic missiles. As much as suggest the global import of the confrontation about North Korean missiles through their violent potential to target overseas lands, the effect is to abstract the peculiar stand-ff of a divided country that is a remnant disfigured by the Cold War as if it can be isolated from the division of the peninsula, and viewed as a focus of global attention. But is the isolation of North Korea that they effectively underscore in such cartographically dramatic terms also not a cause for concern? How can the intentions of the opaque government of Pyongyang even be understood save in a close focus on the local dynamics of the Korean peninsula? If North Korea is increasingly effectively a proxy of China–cast as an enabler of the North Korean state, together with Russia–the country is shown, isolated, as if the Democratic Peoples’ Republic of Korea, DPRK, were the last remaining theater for conducting the cold war in a post-Cold War world. A familiar geography of generals suddenly migrated to the media as the confrontation with North Korea was begun to be processed in maps.
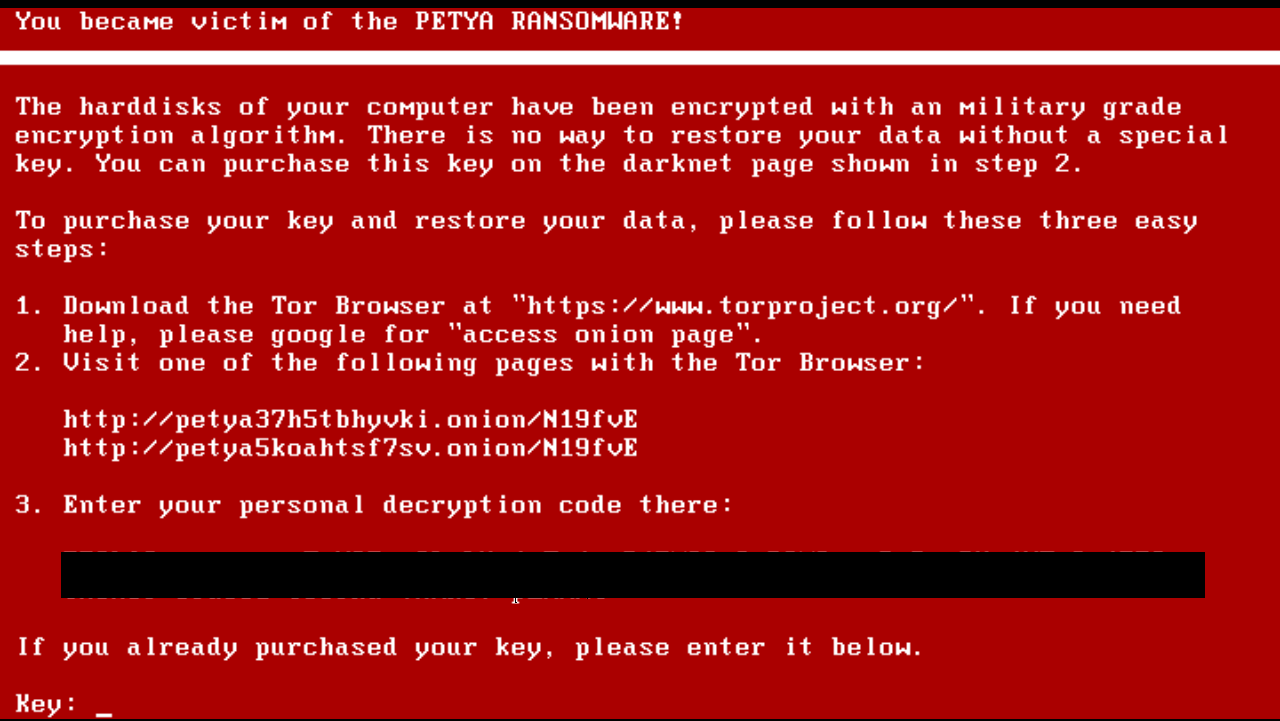
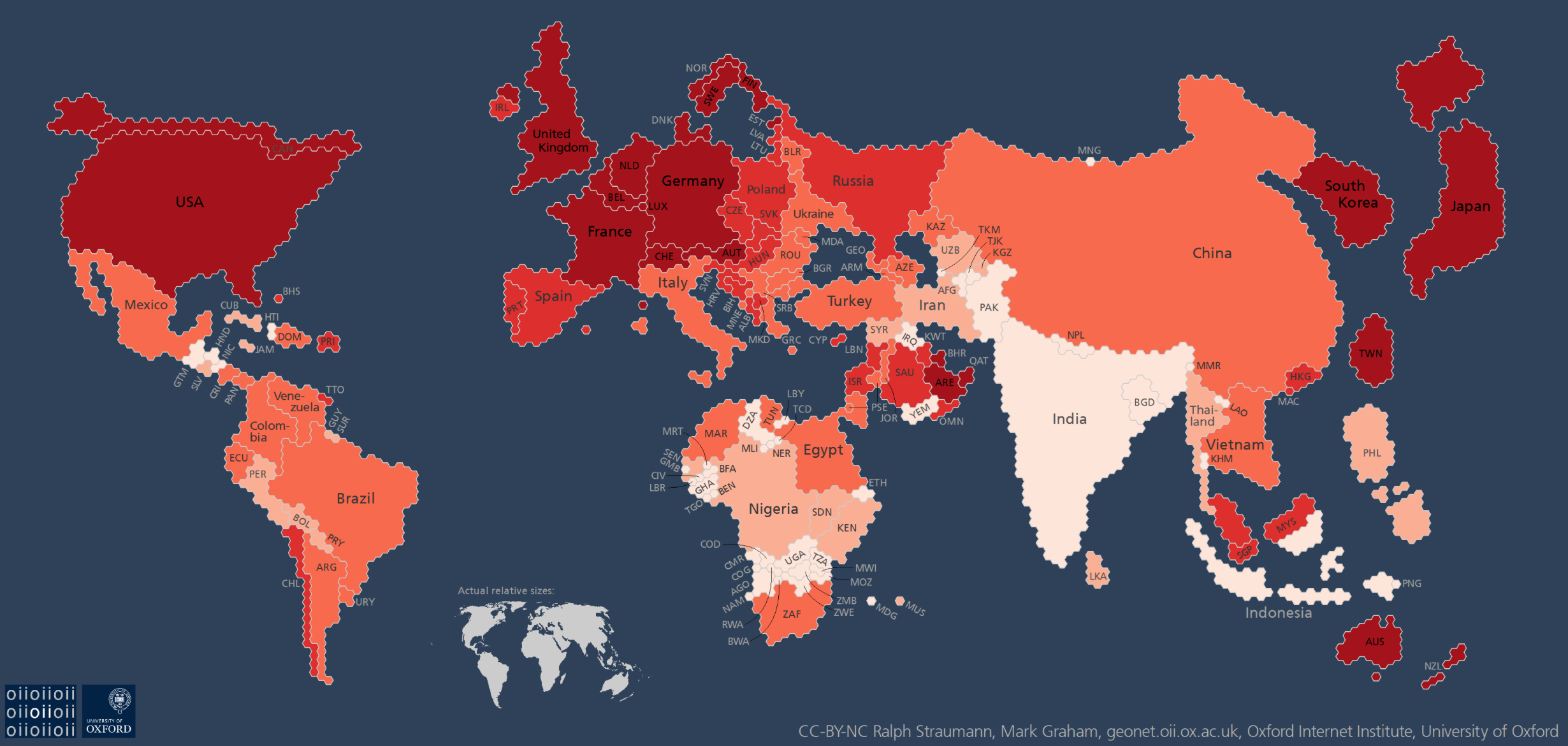
The current migration of this mapping of a global vision of generals to the media presents a problem of the survival of a mental imaginary, able to compromise the pragmatics of a real problem of international relations in dangerous ways. For by magnifying the isolation and marginality of the DPRK in relation to the globe, the maps urge us to focus on the risks that the development of intercontinental missiles pose to world peace. To be sure, they also risk reflecting the very barbed rhetoric of triumphalism and destruction of Pyongyang–a regime that has expressed its eagerness to deliver prophesies of “a merciless sledgehammer blow to U.S. imperialists.” The threats of Kim Jong-un are especially embodied by the creation and possession of his country, for the first time, of Intercontinental Ballistic Missile, and seems to create a narrative less motivated by actual actors, but a drama of atomic, nuclear, or ICBM strikes that is driven by disembodied geopolitical exigencies in a political theater that we don’t know where it will end, but ramps up an all too familiar cartography of fear.
These maps resurrect and resonate with the invocation of previous threats of war during the Cold War–when the fear of atomic attack was widely diffused by the U.S. Government as a basis to justify an arms race. Indeed, by rehabilitating a Cold War imaginary of impending conflict able to escalate into nuclear war, maps seem to activate a similar mental imaginary of polarity–albeit disproportionate one, between North Korea and the United States–that reflect one of the few areas in the world where that rhetoric is still alive of identifying the role of the state in promoting nuclear war–leading Kim to praise the “thermonuclear weapon with super explosive power” as made entirely “”by our own efforts and technology and designed to exceed the atomic bomb dropped at Hiroshima. In this context, the fear of a “global threat” can be rehabilitated as destabilizing global balances of power.
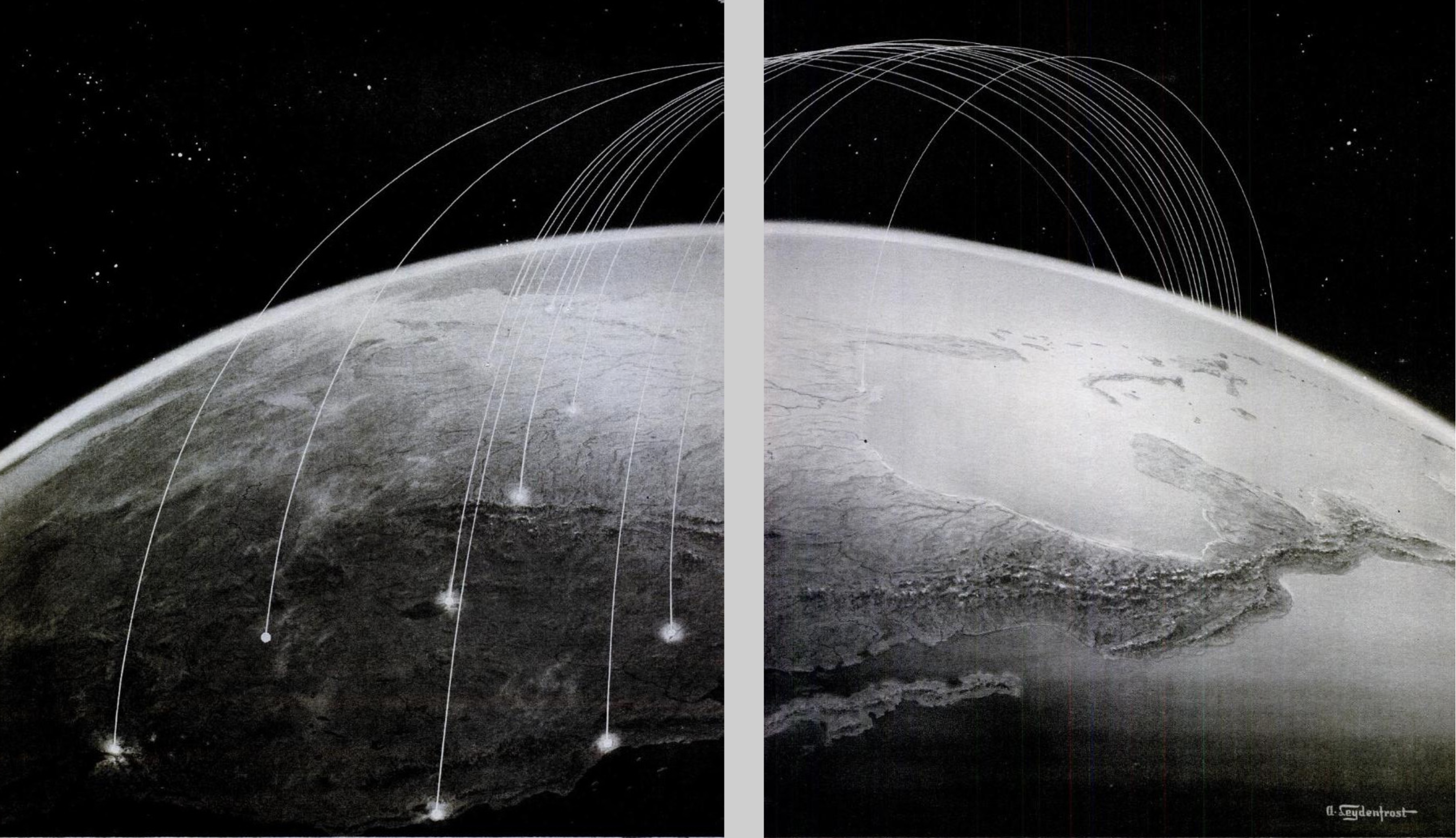
The first scenario of an attack on the United States–cast in fearful and unresolved terms–was diffused in terrifying detail shortly after the bombing of Hiroshima and Nagasaki in 1945, as if in a surge of guilt, by the emigre Hungarian graphic artist Aleksander Leydenfrost, in a bifold spread that appeared in the extremely popular Life magazine, perhaps asking readers to feel a sense of guilt at the destruction caused by dropping two powerful atomic bombs in the Pacific theater of war, that illustrated a memorandum that the commander of the Air Force in the Pacific Theater, Harold “Hap” Arnold, in a “Report to the Army” he wrote in the late summer of 1945. Arnold cautioned against the next war as an episode that would last but thirty-six hours, and for which the United States military must begin to prepare itself, if not to confront the unprecedented scale of destruction that the United States landscape–which war had of course not touched, thankfully–must now take time to prepare itself to face. And the sustained campaign of firebombing Japanese cities after the massive destruction of the second atomic bomb, Fat Man, that was roapped on the port city of Nagasaki unleashed a level of violence that had followed the instant incineration in that city alone of 70,000 had created a landscape of destruction that Leydenfrost’s somber image led Americans to imagine as inflicted on the major cities of the United States, not by the delivery of airborne bombs but the arrival of intercontinental ballistic missiles–what we now call ICBM’s–launched without pilots, akin to German V-2 rockets, but able to reach across the Atlantic, in ways that would redefine what we know as a “theater of war” in globalized terms for the first time. The nightmare of unmanned missiles, viewed from the empyrean heights above the Pacific, seemed to seek o terrify viewers to suggest how quickly and silently an attack could arrive.
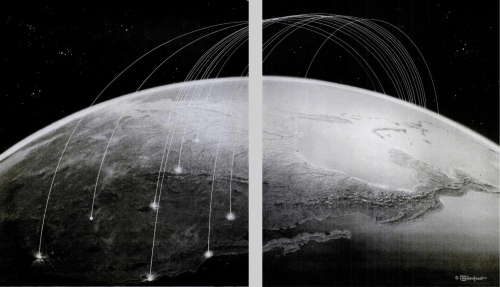
The resurrection of what might be called a map designed by generals such as Harold “Hap” Arnold filled a new need to map the power of destruction that the atom bomb unleashed, and represented both a sort of spin as well as a notion of the stewardship of public debate. Arnold wrote in a context where seemingly responsible “scientific men” were entrusted by the US government to explain to the public the scope of the horrific new power that the atomic bomb unleashed, and to rationalize the devastation of the total destruction of a city destroyed to devastating effects unprecedented in their violence as a decision of the nation, men like James Conant or Vannevar Bush, trusted to create consensus about the use of atomic bombs and the pragmatic basis for atomic policy in a postwar world, at the same time as the popular press quickly predicted the conduct of future wars which minimized all human agency, and perhaps responsibility, by pilotless “robot planes” able to span transoceanic distances and increase the vulnerability of all American cities and industry in the very manner of Japan from a “hail of atomic charges” in 1945.
Leydenfrost’s image, designed for a public announcement of Arnold’s letter, captured this anxiety. It reveals, in a futuristic manner akin to H.G. Wells or recent science fiction, how close to the surface it was as an image of future destruction, able to be harnessed for clear ends as a narrative of imminent fear, even if one that lacked any clear narrative finality as a story which we could ever see as having clear winners. The “revolution in warfare” Conant detected after the destruction of Hiroshima and obliteration of many of the buildings of Nagasaki brought strategies of management of threats in a new global imaginary. Conant quickly acknowledged that there was no real possibility of defense against such a “surprise attack by atomic bombs,” as he dryly put it. Yet the government tried to reorient attention to the immediate problem of survival of the fearful eventuality of an atomic attack. “We are living in a very different world since the explosion of the A-bomb,” Conant began, addressing the problem of what could be done in the event “much of our present civilization” was threatened with extinction. Conant pondered with incredible detachment pondered how “much of our present civilization” was threatened after Hiroshima and Nagasaki, nd to contemplate ways to save the achievements of the United States against such imminent destruction by buried repositories of microfilm,–as if such a parallel responsibility were adequate to the development of the atom bomb. In contrast, Arnold’s “Report to the Army” emphasized the need of responding to a remote atomic strike in ways that created an image of vulnerability to missile strikes that quickly burned into our collective unconscious. Its inheritance might well be reexamined in the light of the fears of global threat of strike from North Korea that has emerged in the very first months of the Presidential administration of Donald J. Trump.
The power of the ICBM warheads that North Korea has developed have, rather eerily, just achieved the level of power of the atom bomb dropped on Hiroshima, enabling exactly the sort of scenario Aleksander Leydenfrost, no doubt with editorial help, was able to so concretely map from a position over the Pacific, which oddly renders North America as an island-like target, as if it could echoe the many flights of United States bombers over Japan. These unmanned rockets, shot from an unspecified country in Africa where the rocket launchers of a nemesis were placed, described the phantasm of the or mental image of the next stage in warfare, rather than an actual map. But the concreteness of the map allowed readers to envision the proximity of a potential strike in particularly powerful ways. And they have been triggered again in the azimuthal equidistant projections that project North Korea at their center, and map the ability of powerful missiles to strike the more populated cities of the United States.

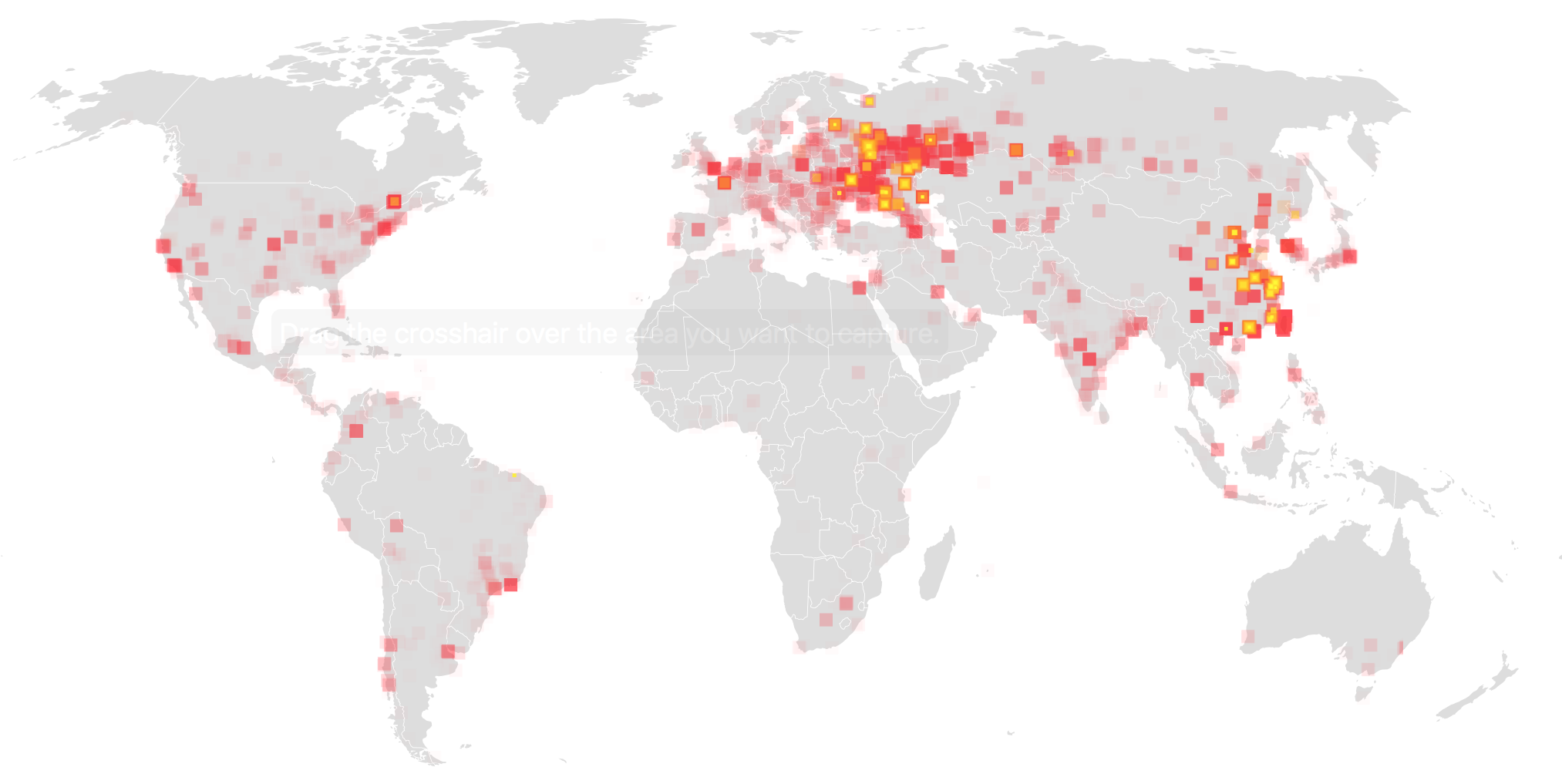
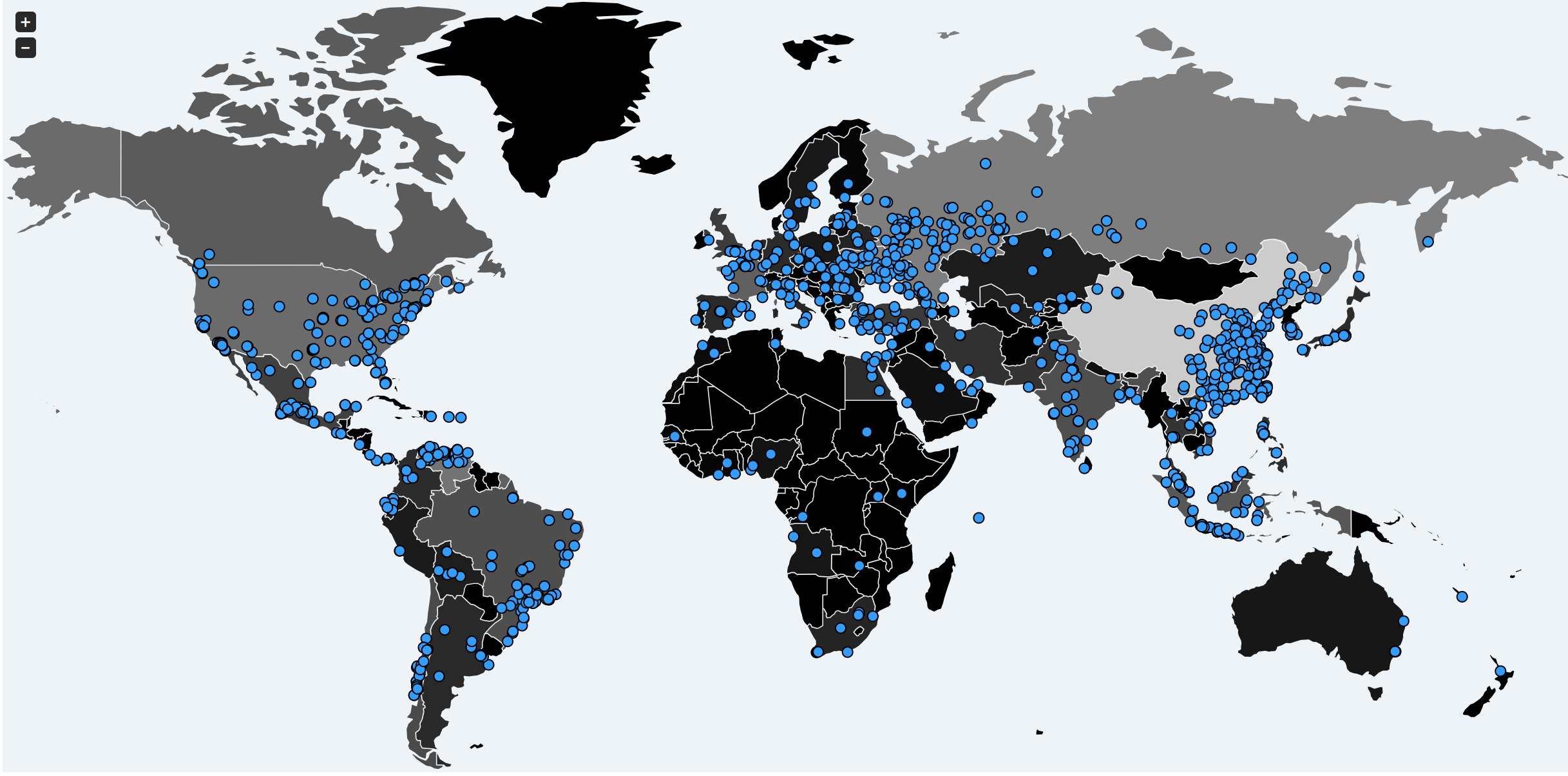
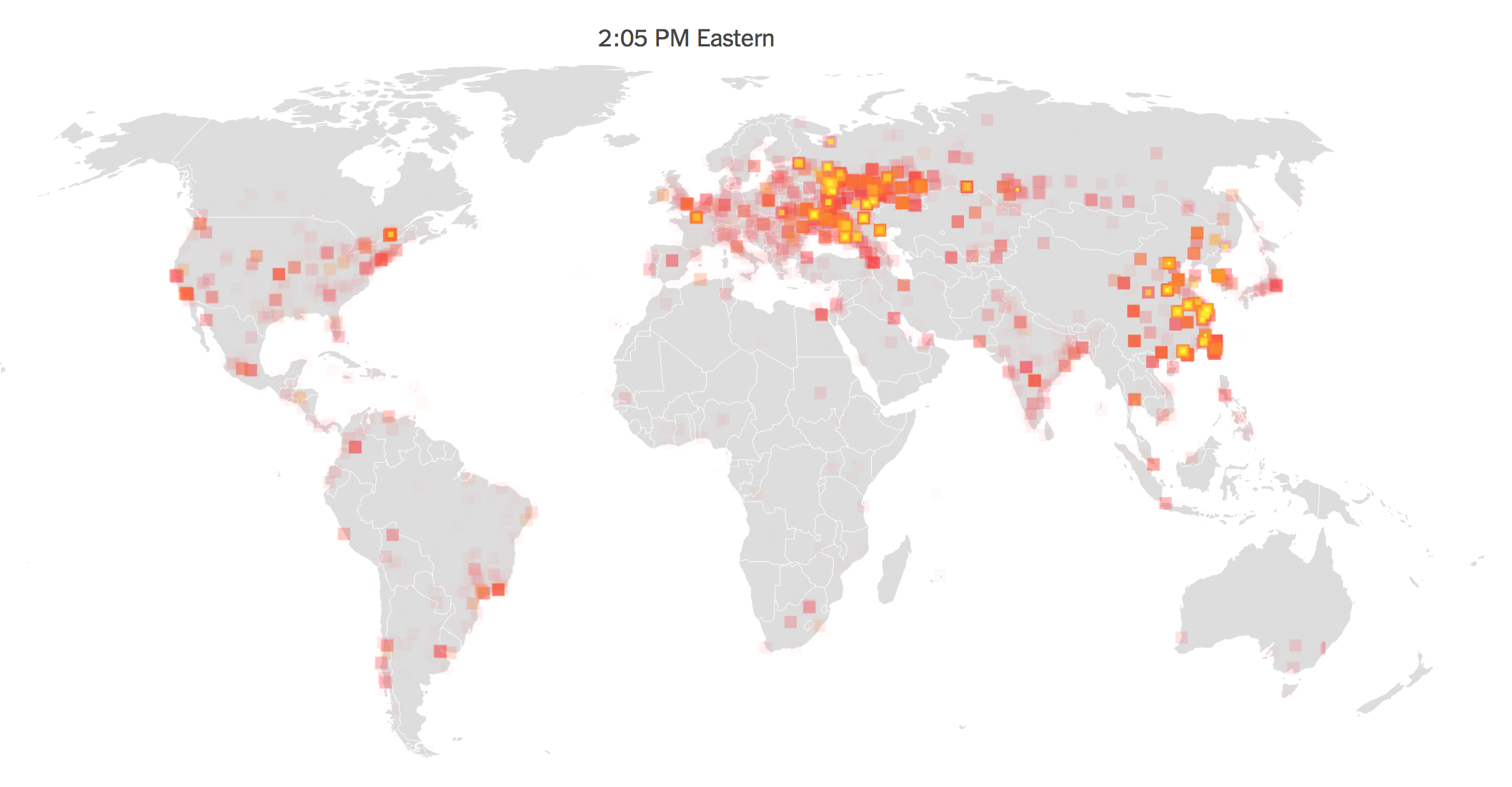
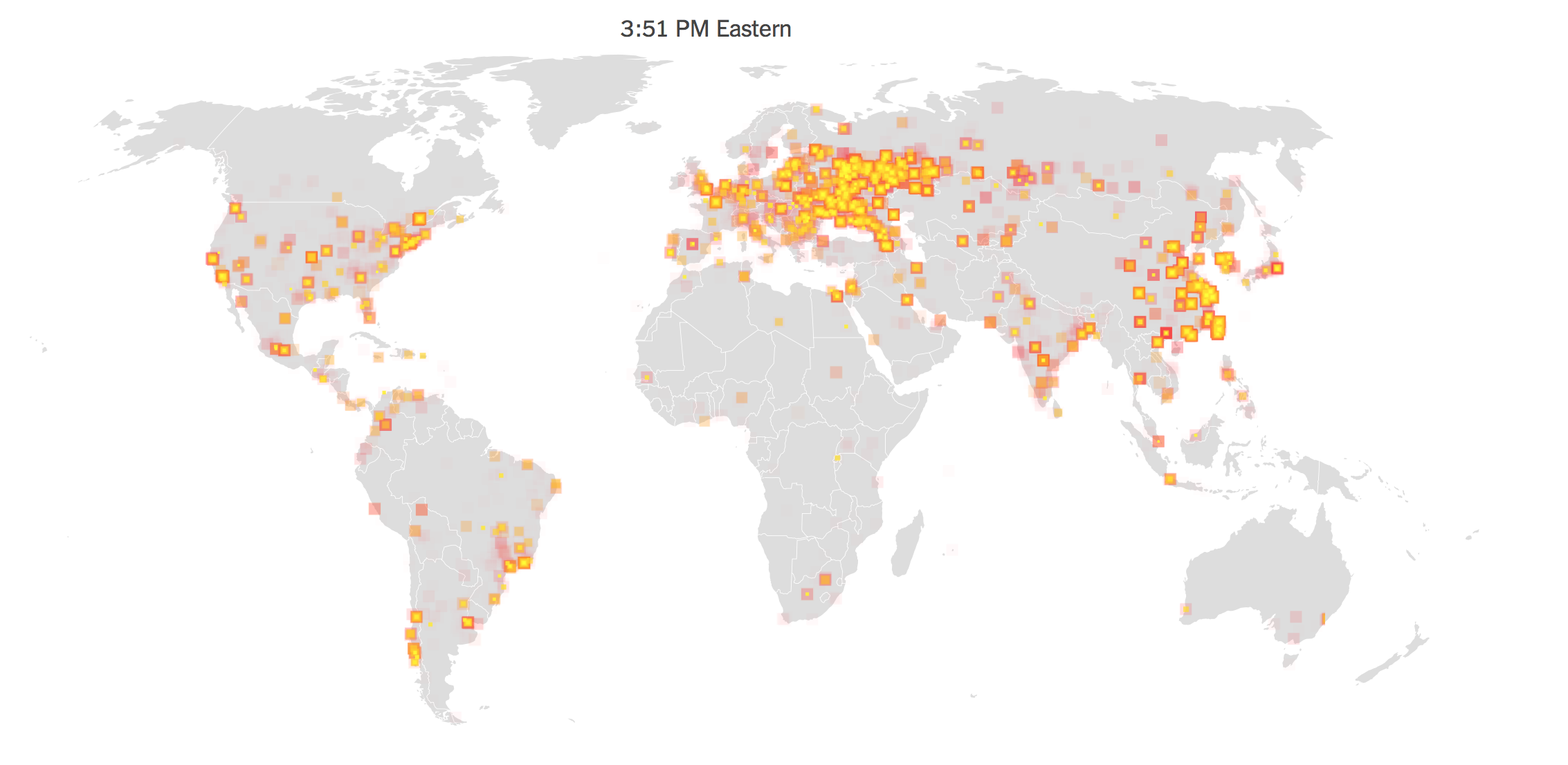
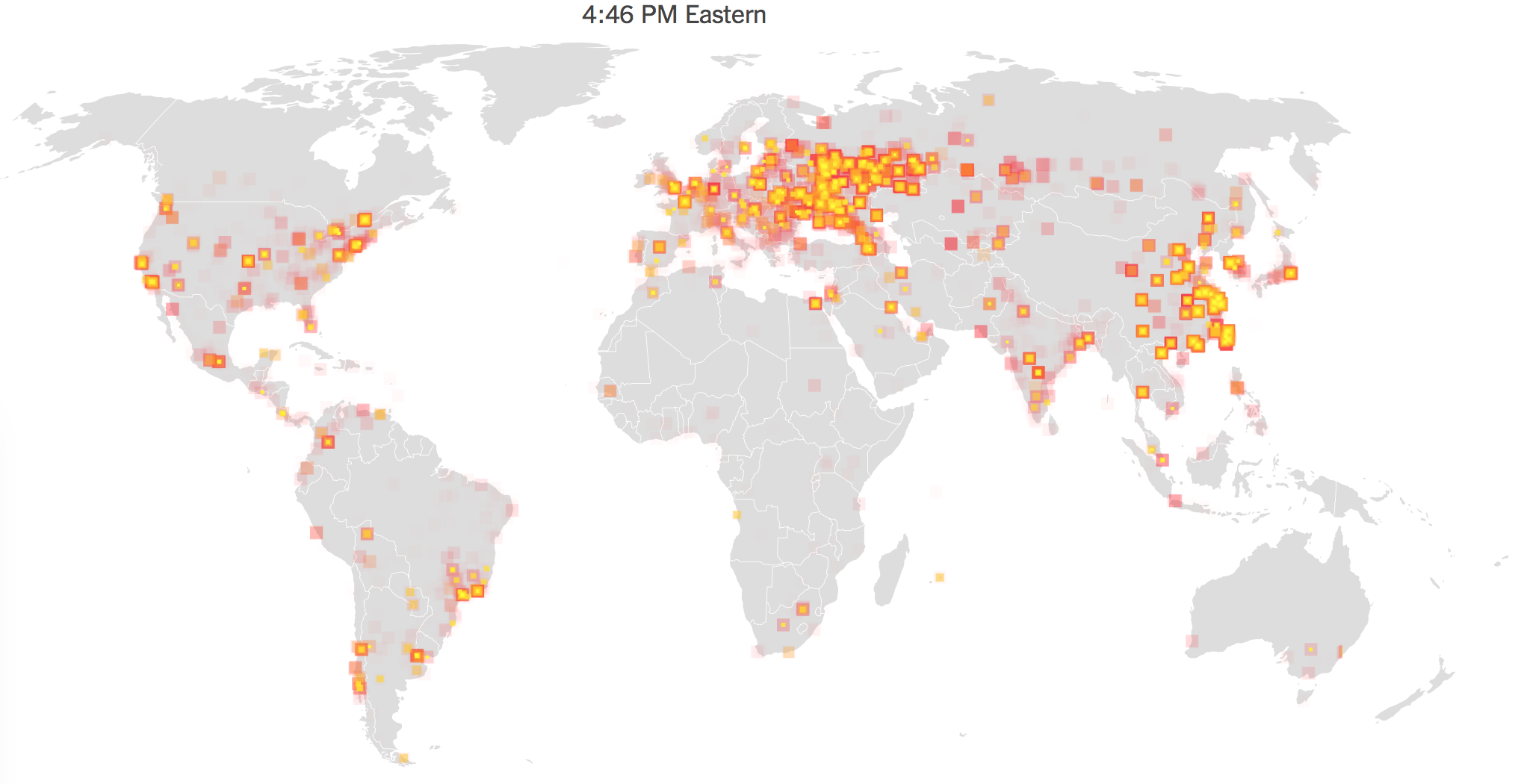
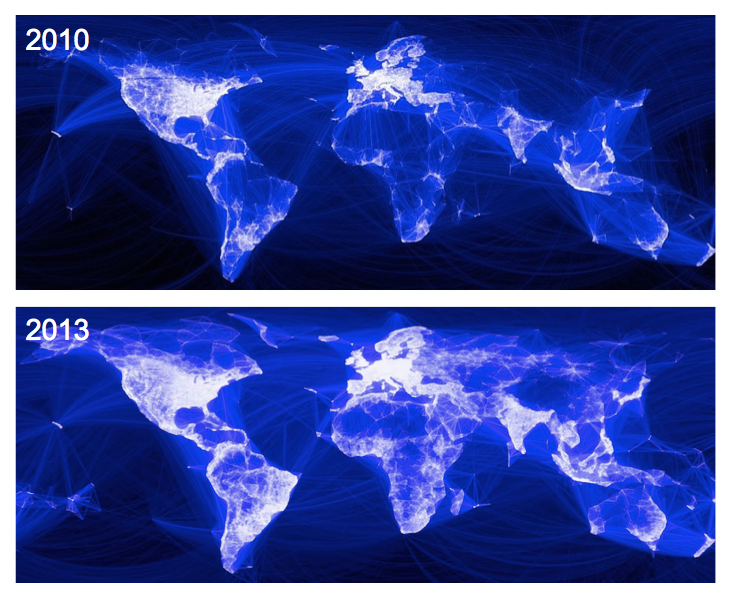
1. Although graphics that render the potentiality of newly powerful missiles developed by Pyongyang work to grab viewers’ attention, they draw attention to the danger of North Korea as if from a general’s point of view. The rush to map the striking range of North Korean missiles, as in the header to this post, often were created by overlays so quickly to perpetuate a sense of a flat earth–particularly embarrassing in an age of web-based maps and spatial tracking. The egregious mis-mapping of a nuclear threat occasioned a volley of objections to the distortions of maps that foreground their danger, and the innocent position of many who are endangered by their missiles, while mismapping their true range. In order to come to terms with the global import of Korea’s generation of ballistic missiles’ of ever greater striking range, web Mercator may irresponsibly effectively shrink the distances missiles travel, with geopolitical consequences, but the mapping of the range of missiles privileges a narrative of overweening nuclear ambitions and aggressive acts that runs the risk of magnifying the military threat posed by Pyongyang, and giving an opportunity for Kim Jong-un to magnify his own sense of grandiosity on a global stage, even in ways that seek to justify the need for a pre-emptive military strike against a North Korean threat. The focus on the hypothetical expansion of missile range and the eagerness to trumpet the new status of North Korean military as able to launch an intercontinental ballistic missile and nuclear strike–long desired by Pyongyang as a sort of metric of global respectability and renown–is a danger but one that repeated exaggerated mipmapping can only magnify.
For in suggesting the blameless nature of other nations before this threat, they direct focus on the aberrant nature of North Korea and its leaders as needing to be contained, and many indeed justify the importance of a “preventive” pre-emptive nuclear strike. The maps open a possibility of alternative narratives, some particularly deadly and undesirable in the extreme, of an immediate launch of warheads not only at American military stationed in South Korea, Japan (especially in Okinawa) or Guam but at the United States as as never before. Indeed, the public statements and postures that Kim Jong-un is “begging for war” seems to map the need for a nuclear confrontation, filled with the frustrated saber-rattling that while “war is never something the United States wants” the “outrageous” testing of a hydrogen bomb only tests its “limited” patience, as North Korea vows its ability to perform a “surprise launch of an ICBM in any place and region at any time,” seeking to prove that “the whole US mainland is within the firing range of DPRK missiles,” as the national news agency KCNA has affirmed.
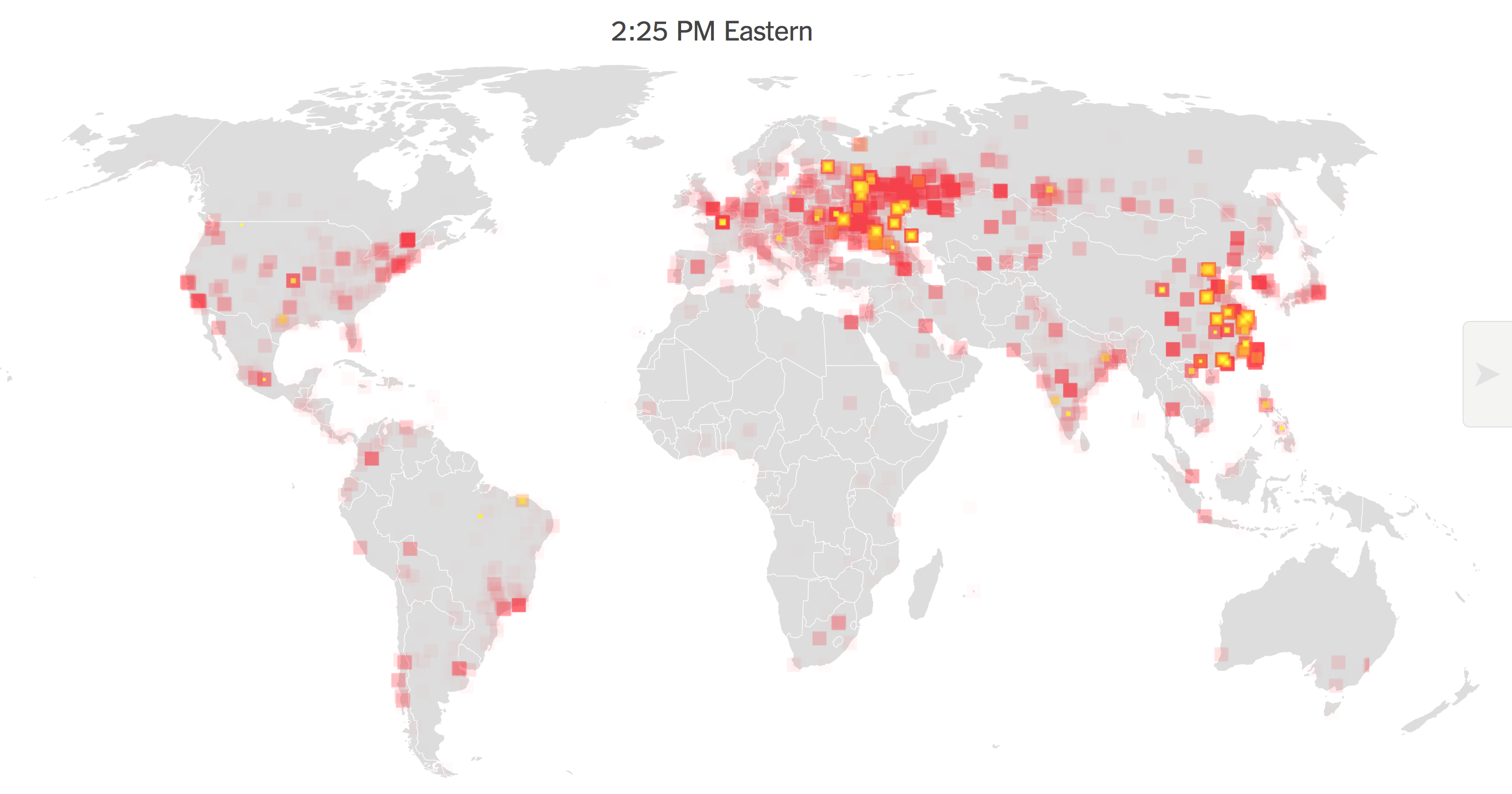
The recent explosion of a bomb with the explosive power of the atomic bomb dropped on Hiroshima by North Korea on the eve its independence celebration provides an illustration of Kim Jong-un’s leadership, even if it is doubted that what seems a thermonuclear device would be able to be attached to a ballistic missile with any reliability. But the expansion of maps of intercontinental range in the global press seems to magnify the threat of immanent attack or aggression from North Korea, as if in a presence to justify what would be an utterly irresponsible decision to launch a military exercise of any limited sort. All too widely reproduced images of the growing range of North Korean missile strikes create an all too real cartography of fear that seem to escalate the danger of a threat and the need for an aggressive military response.
As the actions of Pyongyang have been repeatedly cast as a “global threat” by the Trump administration, from Steven Miller to Rex Tillerson, provoking not so veiled threats of the need to respond with a “precision strike” missiles into nearby waters off the east coast of the peninsula or to strike at the missile test sites, maps of the n this game shifting estimates of the outermost reaches of NK missile strikes by the Democratic People’s Republic of North Korea have provided something of a basis to reveal exactly what the states of that provocation would be and proof of the global threat that North Korea’s missile pose over the unsuspecting and innocent inhabitants of multiple continents. Although the outermost reach of the radius of missile firing is openly acknowledged in the BBC graphic below to be not operational, the claims to have created an ICBM able of intercontinental strikes would place North Korean arms far closer to the United States citizens–as well as to United sates troops stationed in South Korea or Guam–in ways that have been a long aspiration of North Korean governments.
The new justifications of nuclear attack in the aftermath of the apparent explosion of a hydrogen bomb by Pyongyang–and the unrestrained bullying of the North Koreans that “they only understand one thing!”–have pushed the problem of military confrontation to the front pages, with Trump warning of the possibility of a “massive military response” and suggesting if not indeed mapping a targeted nuclear strike of North Korea’s nuclear and missiles sites, as if their destruction could occur without any harm to the world. The threat that Kim Jong-un poses is being cast as a potentially aggressive act–needing to be met with immediate and massive force–even without mapping what his intentions or strategy–as the explosion of a fusion bomb of comparable size to that dropped on Hiroshima is increasingly mapped as a potentially aggressive strike on American cities. The appearance of these charts in the global media no doubt give huge satisfaction to Kim Jong-un, whose dream of seeing his nation as a global power has been realized, as his country suddenly occupies the position of a major threat that the Soviet Union, no less, had occupied in the Cold War.
Indeed, as President Trump responds to questions of his military intentions with North Korea with a shrug intended to be menacing–“We’ll see!”–in a particularly troubling lack of restraint, he seems to be inviting audiences to map the danger signs emanating from North Korea, rather than to establish the security of his own political restraint, by perpetuating myths of the aggressive nature of North Korea. As headlines such as “North Korea Raises the Stakes” have repeated since early July, if not from the first announcement of improving missile technology to complete the construction of an actual ICBM–intercontinental missile–of the sort it has long sought, as if to escape its isolated status, even as South Korea cautioned a proclivity for overstatement of achievement of re-entry technologies, the tenor of recent claims that North Korea raises the stakes may have shifted the metaphor of this test of wills from over thought moves in a game of chess to a contest of truth or dare or to a global game of Russian roulette.
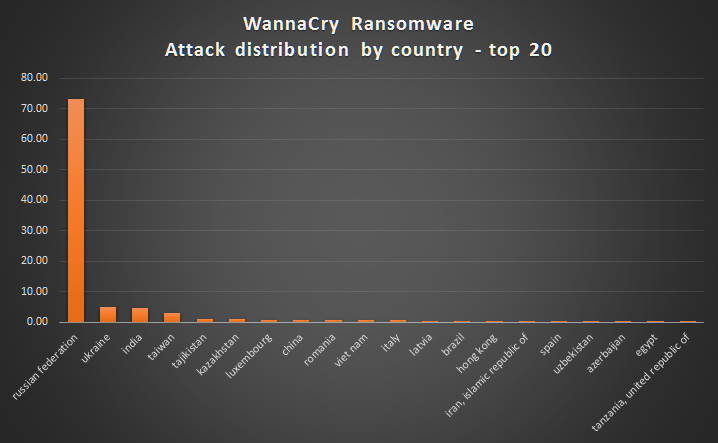
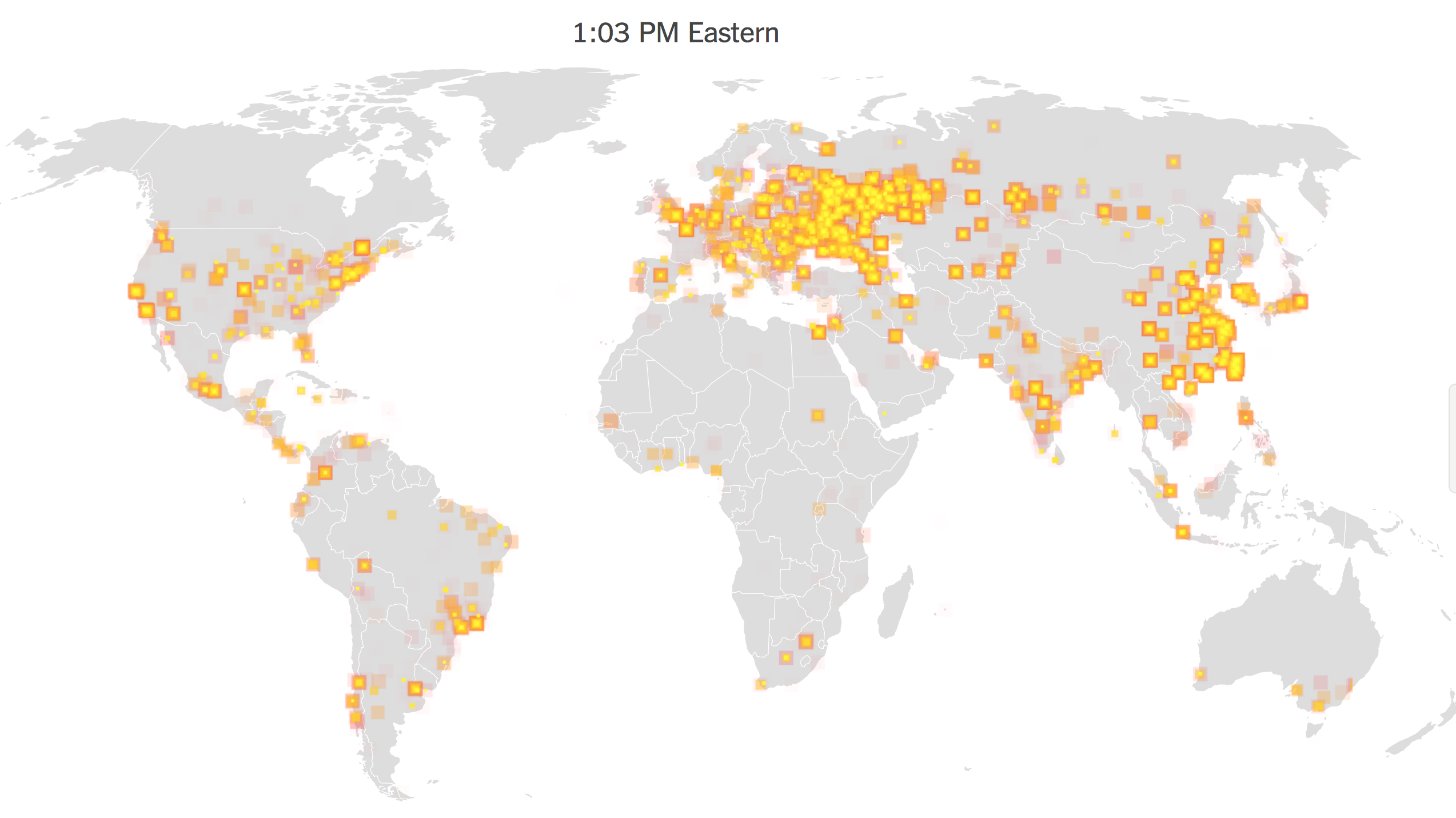
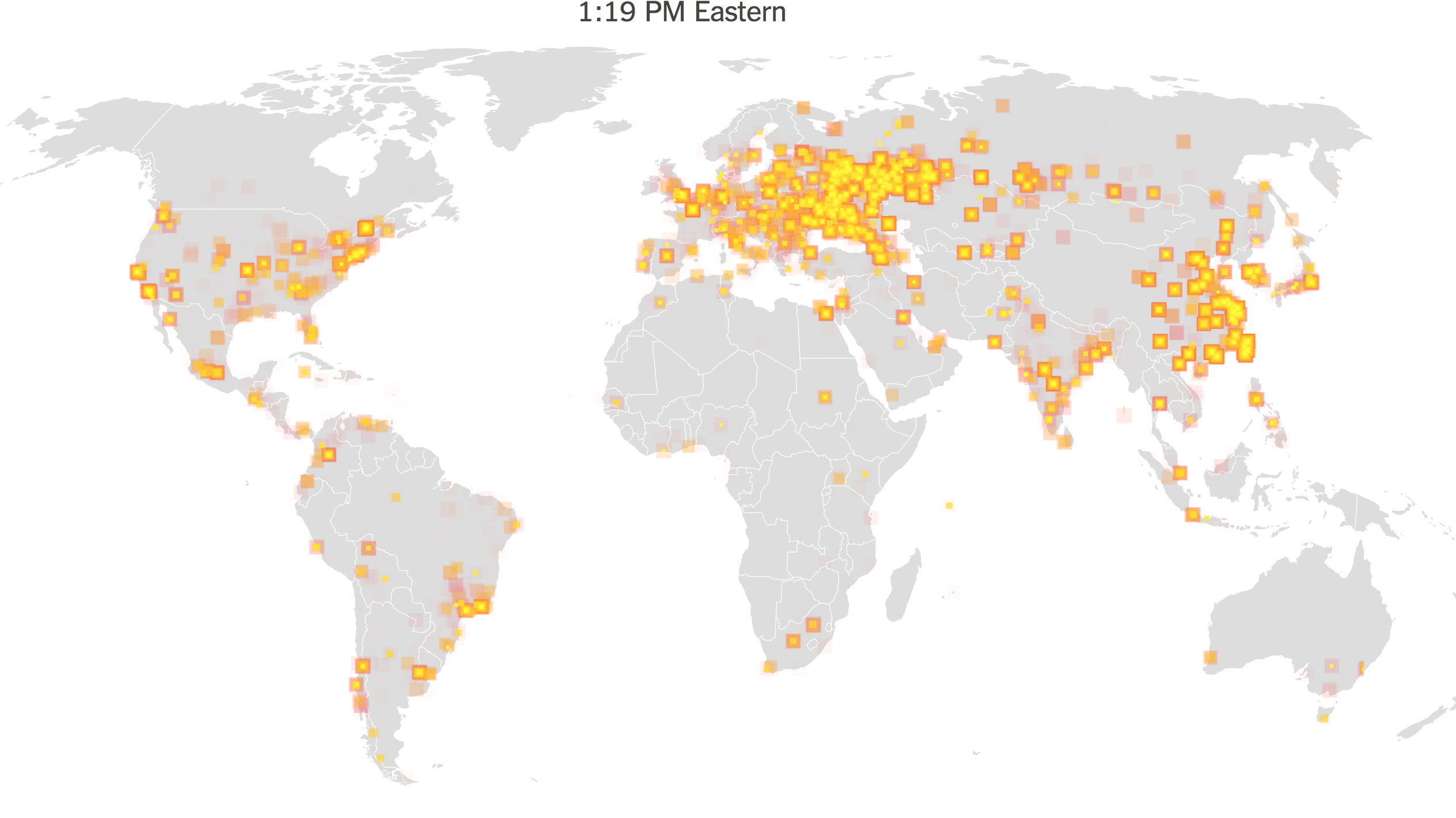
2. Although the maps raise red alarms as they show long-range missiles able to strike the United States, the rush to use a tool plagued with distortions on a global scale is bound to create distortions or suggest the persistence to flat-earth thinking, rather than warp the striking range to acknowledge the spatial distortions of the earth’s surface within theMercator projection. But the readiness to map the ranges of newly tested missiles–and even missiles in development–suggest a rush to affirm a “direct threat to the United States”–as former CIA analyst Bruce Klingner puts it–that threaten to extend the missile range of missiles in development to beyond 13,000 km, which would place the entire United States within its striking range and endanger all who live in the expanded radius. In facing such often unsourced if impressive figures deriving from Japanese news outlets or South Korea, the interests of the maps that derive from such figures demand critical review; ties alleged between military contractors and agencies that create such maps not only terrify, but trigger a powerful memory theater of rapid strikes of an increasingly broad array of long-range missiles, reminiscent of a cartography of fear tracking missiles’ arrival in United States territory from the Cold War.
As North Korea continues to profess commitment to a nuclear deterrent in the face of American bases in South Korea and Guam, charging “persistent moves to launch a nuclear war on the Korean peninsula,” and indeed the precareity of North Korea to American strikes, many visualizations of the growth based on fired missiles public South Korean statements provide a basis to foreground global tensions with an alleged objectivity that invest missiles’ striking range with an unprecedented of accuracy. They may lack such accuracy–despite their imminent danger–but the cartography of fear that they create surely seems to escalate their threat and the rapidity of their possible arrival–even if they may well exaggerate the likelihood of their striking range, without noting how operational even the most recent Hwasong-12 medium long-range missile is.

3. But in mapping the extent of such “striking range” to cover most–or indeed almost all–of the United States, such graphics manufacture an all too real danger by cartographic artifice alone, given the range of missile strikes a reality that they may well not be able to achieve in terms of either atmospheric re-entry or precision targeting, although this is an objection which we surely don’t want to have to test to find out.
The implied danger of provoking such a strike–or allowing such a strike not to be defended against–has in fact undoubtedly interested the Heritage Foundation, a conservative educational institution once prominent in setting the agenda for the nation in the Reagan administration, and now eager to bill itself again as an institution able to “transform America” by being at the forefront of conservative thinking, from the curtailing of “excessive” environmental regulations, to the use of tax reform to “grow” the economy, to the end of universal health insurance, to the distribution of military gear to local police. The interest of increasing the military budget in the Trump years is promoted through the mapping of an impending and immanent nuclear threat from North Korea–
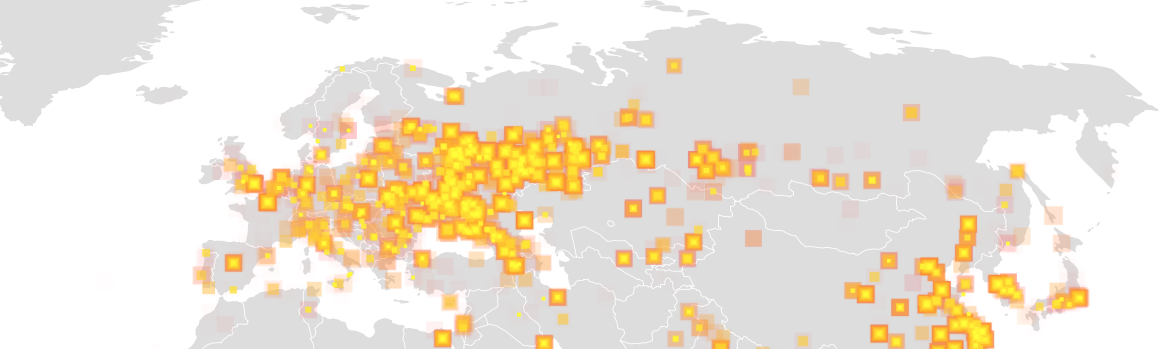
 February 11 and 16, 2016; December 2, 2016
February 11 and 16, 2016; December 2, 2016
–that is abstracted from the military presence of the United States in the Korean peninsula, or indeed the political dynamics of the peninsula itself and the region, in particularly dangerous and short-sighted ways. The notions of a nuclear terror that such images accentuate–ignoring the question of whenter such missiles are perpetuate all too familiar narratives of the victimhood of those whose lives are endangered by the growing reach of bombs are particularly canny in their use of the objective rhetoric of cartography to make an unsubtle point, and suggest a sense of inevitability in the expanding ranges that North Korean missiles are able to target cities. The sense of such strikes–and the narratives of inevitability and a needed response that they trigger–have a long history, even if they are meant to describe actualities. For they have worked to help rationalize such a pre-emptive nuclear strike, as FOX experts speculated if “it may be time for a preemptive strike” if America should “risk Los Angeles,” imagining the waves of regret if a missile approaching the United States should a missile interceptors located at US bases not work in the thirty minutes before it arrives, in a landscape we have seen evoked before.
It did not, in fact, take long at all from the dropping of atomic bombs on Hiroshima and Nagasaki for the General leading the American Air Force to imagine the new landscape of mutually assured destruction that defined the landscape of fear of the Cold War. Even though intercontinental ballistic missiles did not yet exist, save as imagined threats, or on the drawing board, the vision of strike from atom bombs arriving from overseas was presented an immediate fear to Americans, and enlisted as a compelling basis for justifying the expansion of the post-war military budget–and even equipping the nation with underground silos for storing and firing missiles able to respond to impending missile attacks. Within months after the destruction of Hiroshima and Nagasaki, when the ICBM’s that haunt the current global landscape–Intercontinental Ballistic Missiles–did not actually exist, save as imagined threats, the powerful images of destruction in what was assured to be a coming “Thirty-Six Hour War” begun by atomic bombs descending on the United States engraved a fearsome image of the danger of the first unprovoked first strike of the atomic age.
The mapping of an atomic threat to the United States invited Americans to envision the possibility of attack. A similar spatial imaginary seems, indeed, resurgent in the nuclear standoff with North Korea, cannot help but recall the imminent arrival of those arcs of already fired atomic warheads or bombs, which smoothly move toward American cities through the night sky to target an unsuspecting population lying in bed at night, even if the projections of missile ranges of the missiles being tested by the North Korean army and their leader, Kim Jong-un, do not arc so elegantly over a landscape. The same landscape haunts both images. If the escalation of tensions between North Korea–N.K.–and the U.S. is mapped to process the threat of the increasing power of rockets carrying nuclear warheads, the maps advance threats of a nuclear strike on the United States in the header to this post that mirror those designed to instill panic and escalate defenses shortly after World War II, and are an odd throwback to the Cold War imaginary. But it seems to have reignited a Cold War imagery of threatened attacks on cities of North America, all too reminiscent of Cold War maps of missile range strikes.
While it is terrifying to not know the intentions of Pyongyang, or the ever-smiling Kim Jong-un, the image of a Cold War spatial imaginary seems to mediate Donald Trump’s geopolitics, and the increased fear that Trump may not disavow a nuclear first strike, not so long ago condemned by Republicans as revealing liberal naiveté on issues of national defense–even if agreement against first-use of nuclear arms has been broad world-wide and recently won broad endorsement as a needed means of controlling nuclear weapons. It is important to note that the map of impending missile strikes far more conditioned the United States than the North Korean government’s response. But the spatial imaginary of missile threats has helped enable a rhetoric of confrontation and saber-rattling that Donald Trump has enjoyed effectively conjuring the threat of an immanent nuclear conflict more than Pyongyang, although the sense that an over-sensitive North Korea was only saber rattling may have been overestimated. The odd symbolic form used for mapping of the range of NK missiles as a target centered on Pyongyang in public media sources, however, keyed o the Nodong, Taepodong-1, Musudan, and Taepodong-2 missiles, suggests the two-fold message of such maps, even more than the maps from Graphiq, which similarly placed Alaska in rapid striking range.

Although these maps tend to fail to distinguish clearly between missiles that have been observed or are in development–as most of the ICBM’s capable of striking the United States were believed to be–the range of US military bases within striking distance of NK missiles are both increasingly aggressive, and seem almost desperate attempts to come to terms with the rapid growth of their rockets’ power. Images that hypothesize the expanded ranges of rockets register the shock of North Korea’s creation of intercontinental missiles and process fears of impending missile strikes from its expanded nuclear arsenal. Such fears were of course foregrounded in North Korean media’s showcasing of Kim Jong-un’s apparent delight in the use of maps to suggest the range of those missiles he has developed at considerable sacrifices for his country–
 Kim Jong-un studying the flight of the Hwasong-12, which reached an altitude of 1,312 feet Reuters/KCNA (May 14, 2017)
Kim Jong-un studying the flight of the Hwasong-12, which reached an altitude of 1,312 feet Reuters/KCNA (May 14, 2017)










 Al Drago/New York Times
Al Drago/New York Times